my friend sophie got fired from her job at Facebook and turned down a $64,000 severance package in order to leak this, so u better read it. buzzfeednews.com/article/craigs…
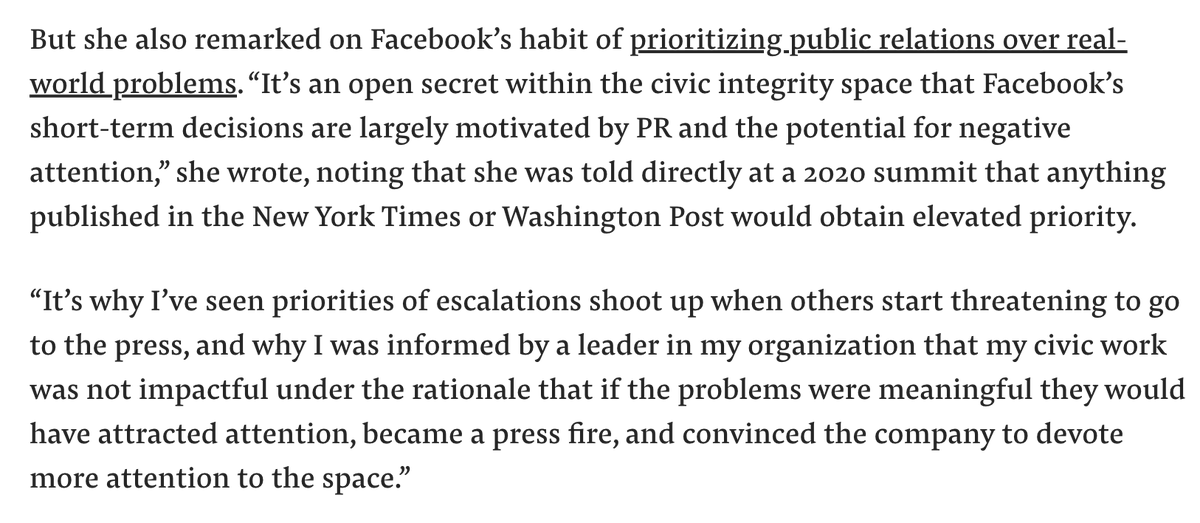
my biggest takeaway from this article is that FB could be doing a lot more to prevent politically-motivated bot activity, but they choose not to because they don't see any immediate revenue or PR benefit from doing so. 
clarification: in order to leak this *internally* at Facebook
FYI Sophie did NOT leak this memo to Buzzfeed. she posted it internally at FB, and then @BuzzFeed published this article without her permission.
I'm disappointed in @BuzzFeed for not respecting their source's wishes on when and how to publish their information.
I'm disappointed in @BuzzFeed for not respecting their source's wishes on when and how to publish their information.
• • •
Missing some Tweet in this thread? You can try to
force a refresh