Continuing the tweet-chain of @colinoflynn on AirTag hacking, we will look at the flash contents now!
https://twitter.com/colinoflynn/status/1390486554586587139
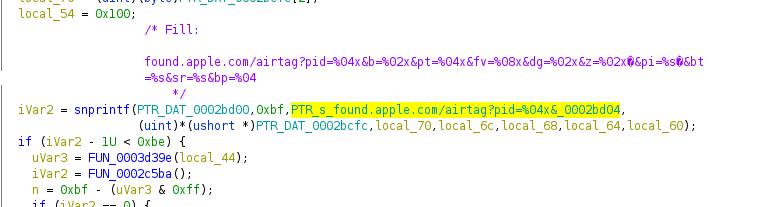
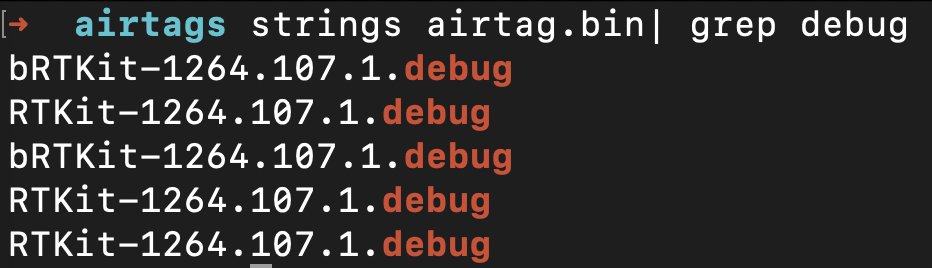
Similar to most Apple embedded devices, the AirTags also seem to run RTKit... And this is where it gets interesting: It's a DEBUG build - debug builds have more functionality, and sometimes more logs & co - this is good news!
/cc @naehrdine
/cc @naehrdine
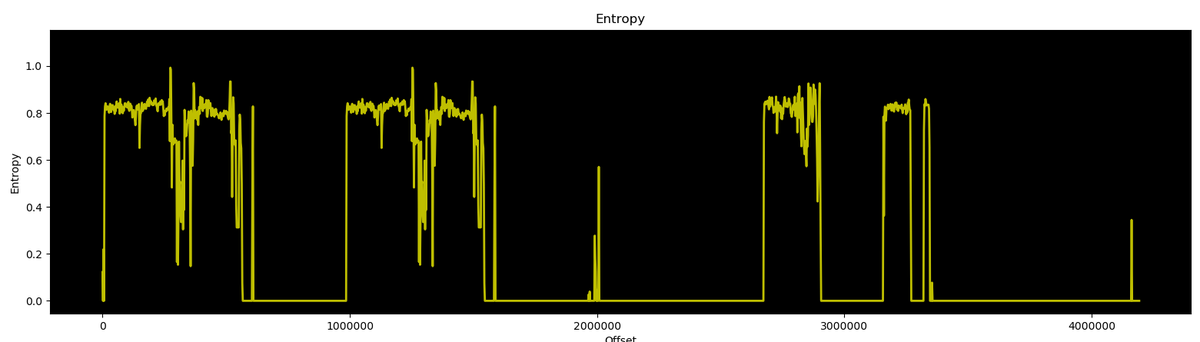
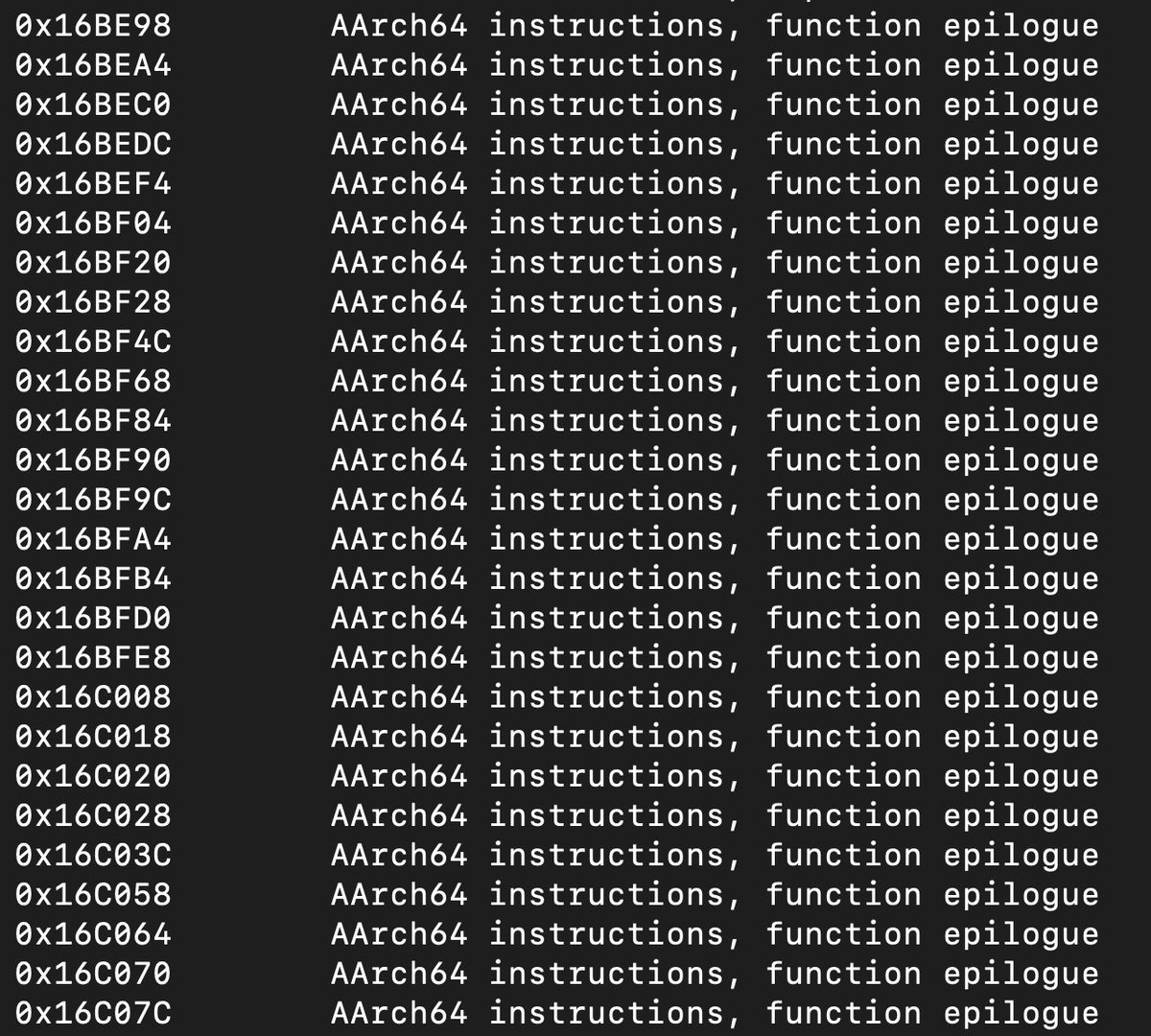
Also looks like the firmware for the U1 DSP is on the flash, as you can find a ton of AArch64 instructions 
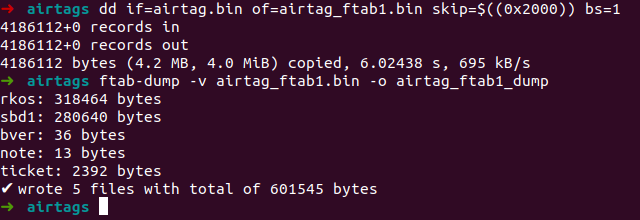
Next step: Dump the rkos images contained in the firmware...
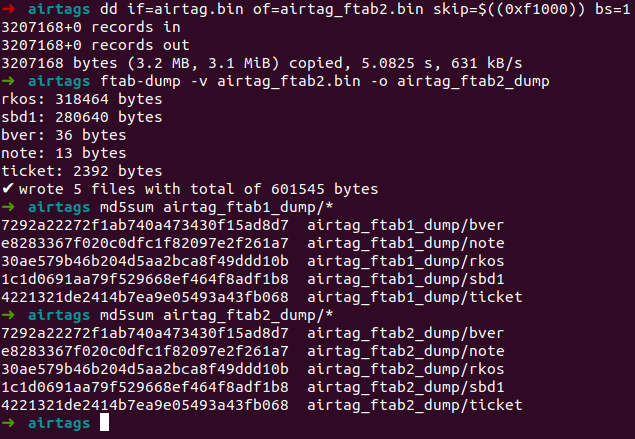
Using ftab-dump (github.com/19h/ftab-dump) it's as simple as this 😀 
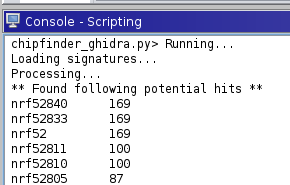
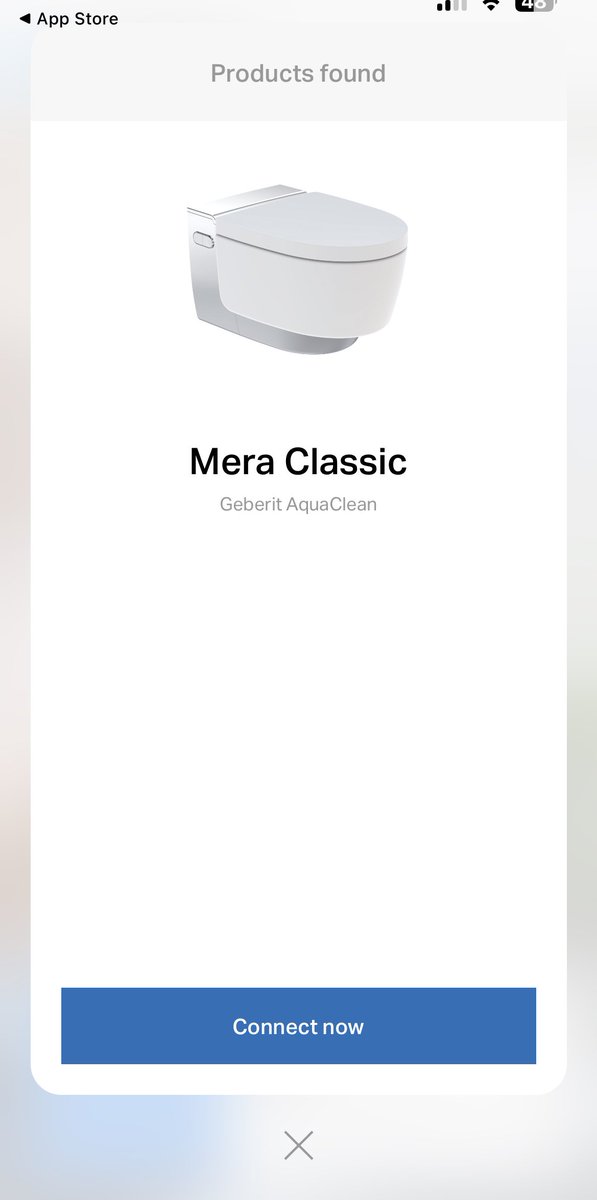
Ohhh, what do we have here? This looks a lot like it might be an nRF52 firmware, which is the microcontroller used on the AirTag! 
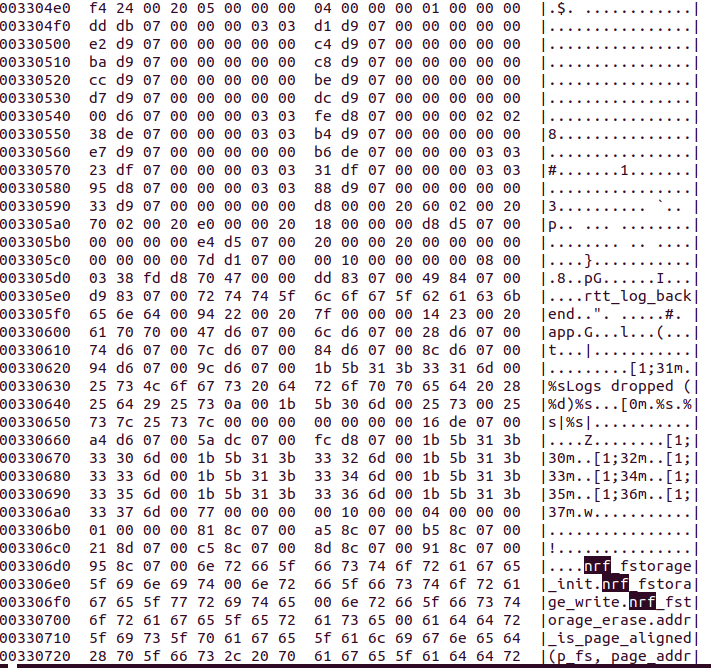
Hmm too bad, looks like it's just a reset vector, not actual firmware :)
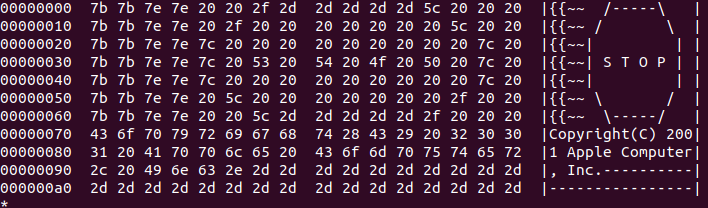
I still remember when I first saw this Apple note - in the firmware images of my 3rd generation iPod when I just got started with hardware/firmware reversing 😀 
(If someone close to Stuttgart has too many AirTags and can spare one.. hit me up 👀)
For those playing along at home: Loaded the firmware starting at 0x28D000 into Ghidra, loading offset seems to be 0x1c000 - guessing that there's a bootloader in front of that?!
Then used SVD-Loader to load an nrf52 SVD I found - it's not super detailed but gets the job done
Then used SVD-Loader to load an nrf52 SVD I found - it's not super detailed but gets the job done
Sweet, picking some tags up in an hour, that should be fun😬
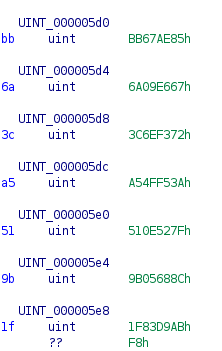
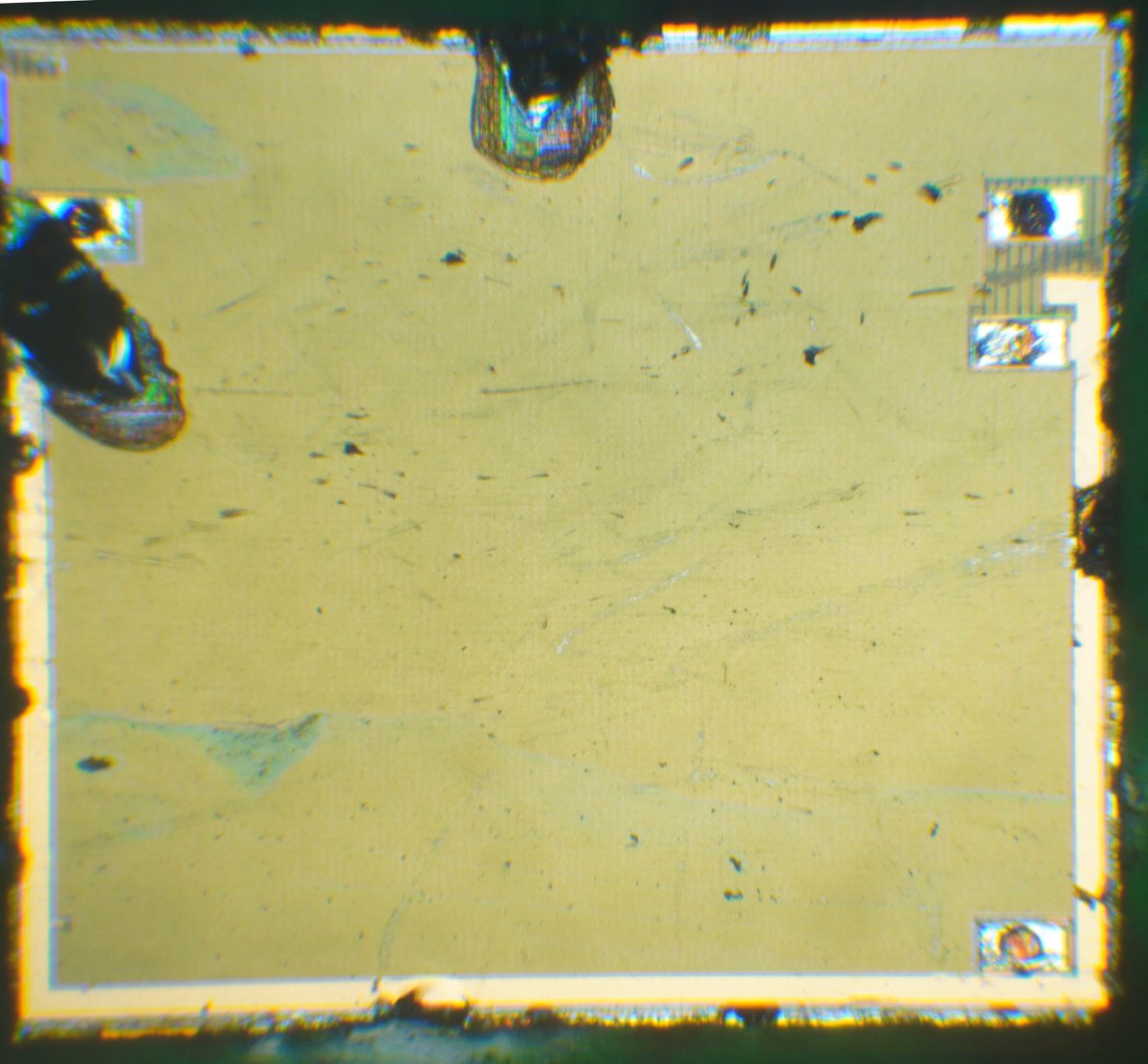
And found the SoftDevice firmware used on the AirTag - thanks for the hint that it's at the beginning of the flash @JAlDhalemi :) 

As so often I’m stuck in writing tools: this time a dual SPI analyzer that gives me the data in the format I need :)
• • •
Missing some Tweet in this thread? You can try to
force a refresh