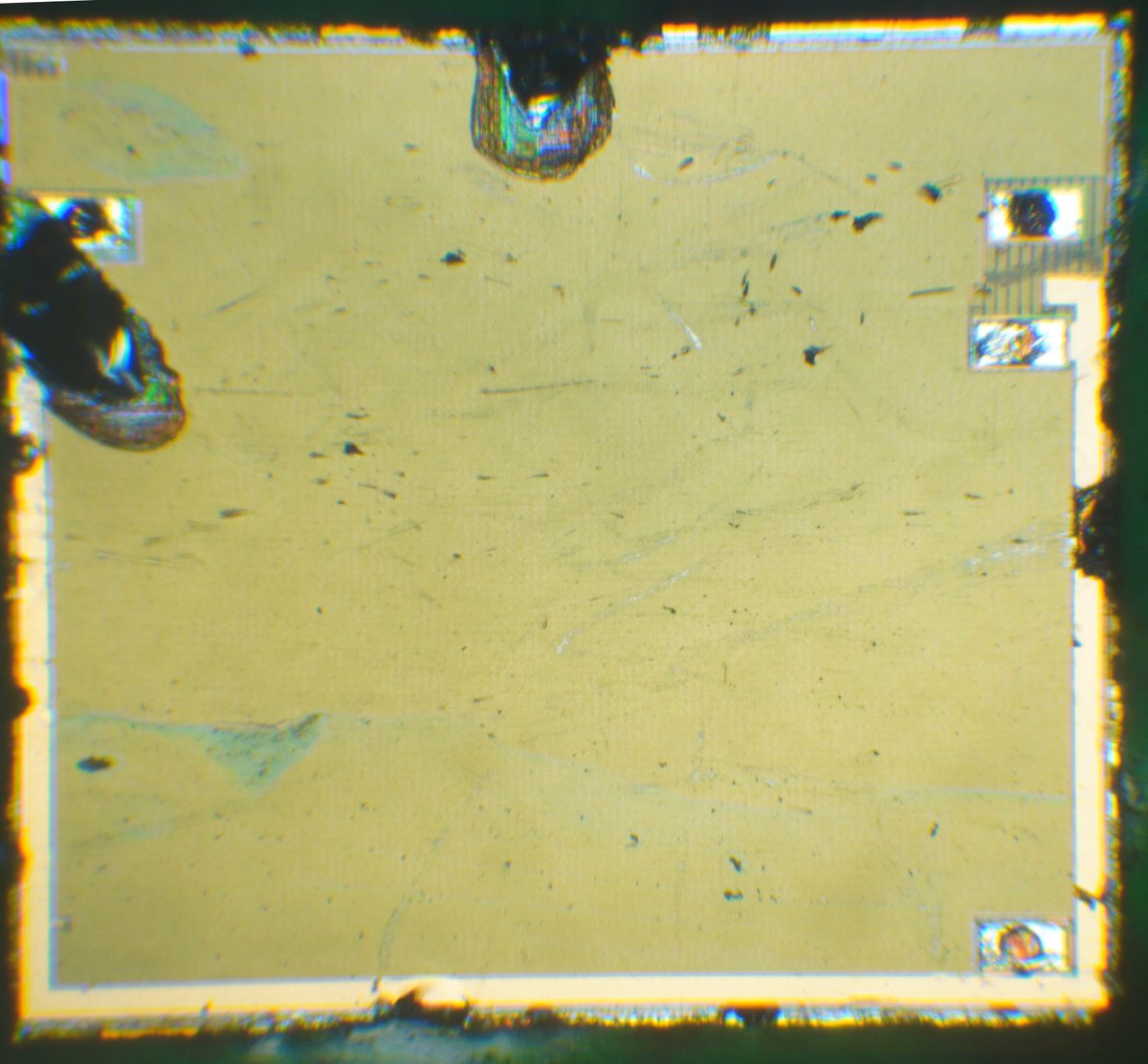
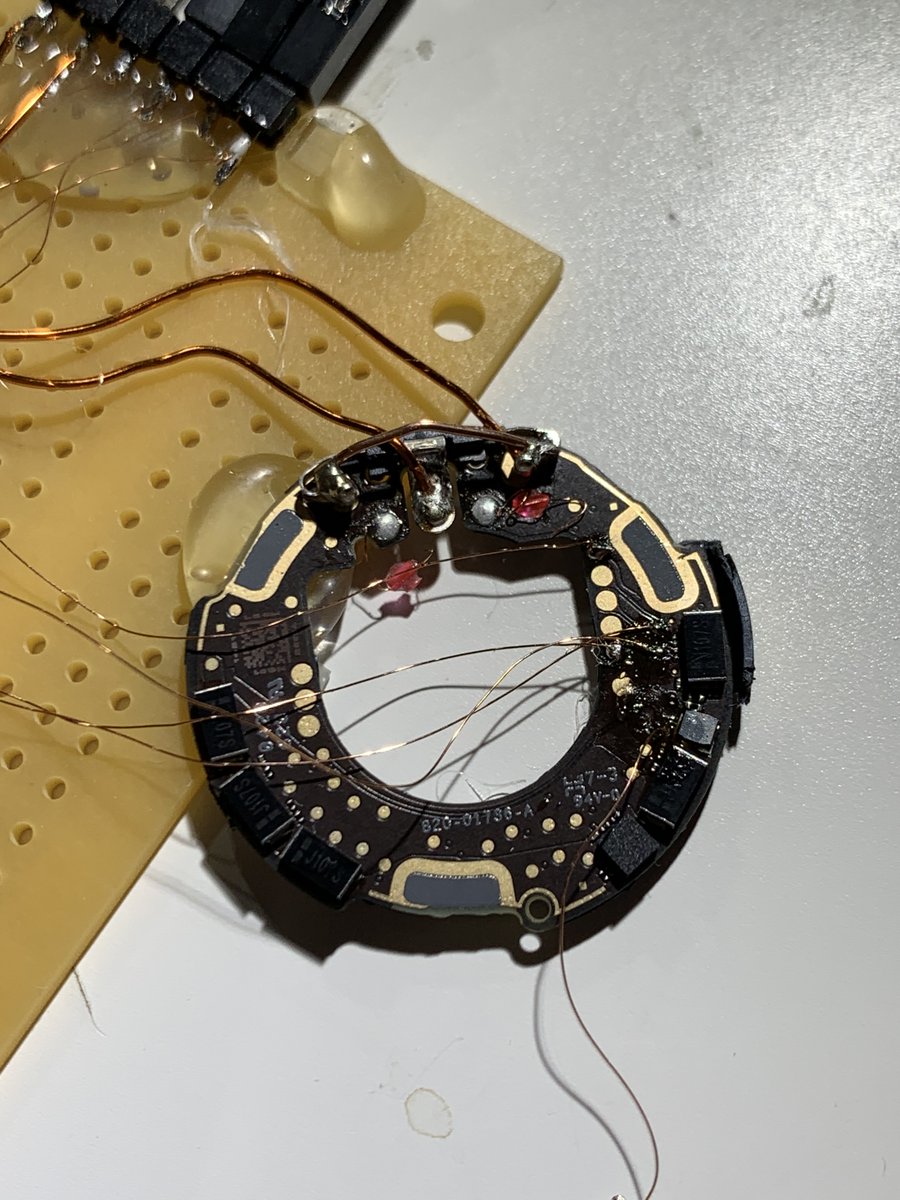
Yesss!!! After hours of trying (and bricking 2 AirTags) I managed to break into the microcontroller of the AirTag! 🥳🥳🥳
/cc @colinoflynn @LennertWo

/cc @colinoflynn @LennertWo

Dumped the firmware and some important areas😀(am I missing any other important ones from the nRF52?) 

Thanks to @colinoflynn for the test point mapping (and nerdsniping me with the AirTags in the first place), and also for listening to my rambling/cursing/etc :)
And confirmed that we can re-flash the microcontroller! Woohoo.
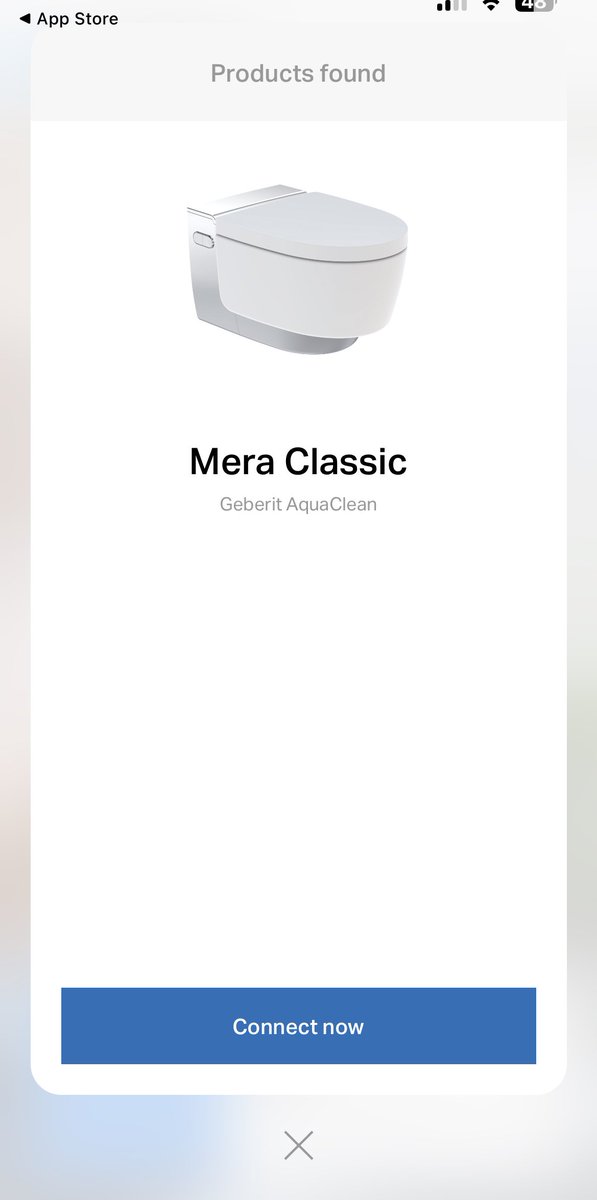
Built a quick demo: AirTag with modified NFC URL 😎
(Cables only used for power)
(Cables only used for power)
And with that it’s time for me to get some sleep :) This was a ton of fun!
(Also, can I now claim I was first to “hack” an Apple device?!)
(Also, can I now claim I was first to “hack” an Apple device?!)
• • •
Missing some Tweet in this thread? You can try to
force a refresh