NEW @citizenlab joint-report with @MsftSecIntel: "Hooking Candiru," in which we provide an interesting look into the global proliferation of spyware from Candiru: another big player that sells hacking tools to govts, including known surveillance abusers citizenlab.ca/2021/07/hookin…
Our analysis is based on a "patient zero", a Western European politically active individual. We extracted a copy of Candiru's spyware from their computer, after identifying that their computer was communicating with Candiru spyware servers. So how did we find our "patient zero"?
Well, first, @citizenlab found a 2017 OPSEC mistake by Candiru, where six of their supposedly "hidden" spyware servers accidentally returned a TLS certificate (seen here on @censysio) with "candirusecurity[.]com" (oops!!!) 

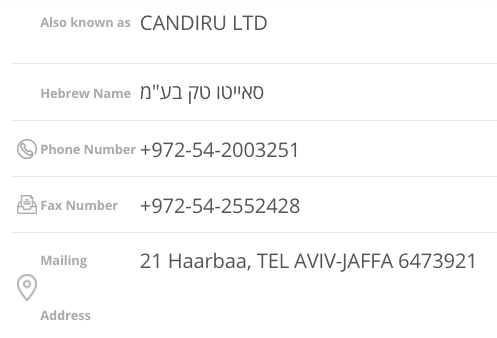
We linked this "candirusecurity[.]com" domain to a spyware vendor "Candiru Ltd", using WHOIS info for a second domain name that was registered with a candirusecurity[.]com email *and also* a phone number belonging to Candiru (per a business directory) 


We later saw different weird self-signed TLS certs returned by these servers, and used @censysio and @RiskIQ to uncover 100s of similar certs on 100s of IPs (pointed to by 750+ domains) that we link to Candiru. Here are some @censysio queries we used so you can follow at home! 



We then leveraged @teamcymru telemetry for the Candiru servers that we detected, which together with our @citizenlab civil-society connections, led us to our "patient zero." We analyzed their computer, ID'd components that talked to Candiru servers, and extracted the spyware!
@teamcymru @citizenlab We shared the spyware with Microsoft's @MsftSecIntel, who (surprise surprise) found that Candiru's Windows spyware was being used to target 100+ people, including journalists, activists, and other members of civil society. microsoft.com/security/blog/…
Also, @MsftSecIntel landed a pretty substantial blow against Candiru by detecting and patching *TWO* zero-day Windows privilege escalation exploits they were using (CVE-2021-31979 and CVE-2021-33771). Microsoft's patch went live during this week's Patch Tuesday. 

Of course, like any spyware company worth its salt, Candiru also offers spyware that can infect mobile devices (according to a Candiru proposal published by @TheMarker), though their mobile spyware has not (yet) been captured and publicly analyzed. 

• • •
Missing some Tweet in this thread? You can try to
force a refresh








