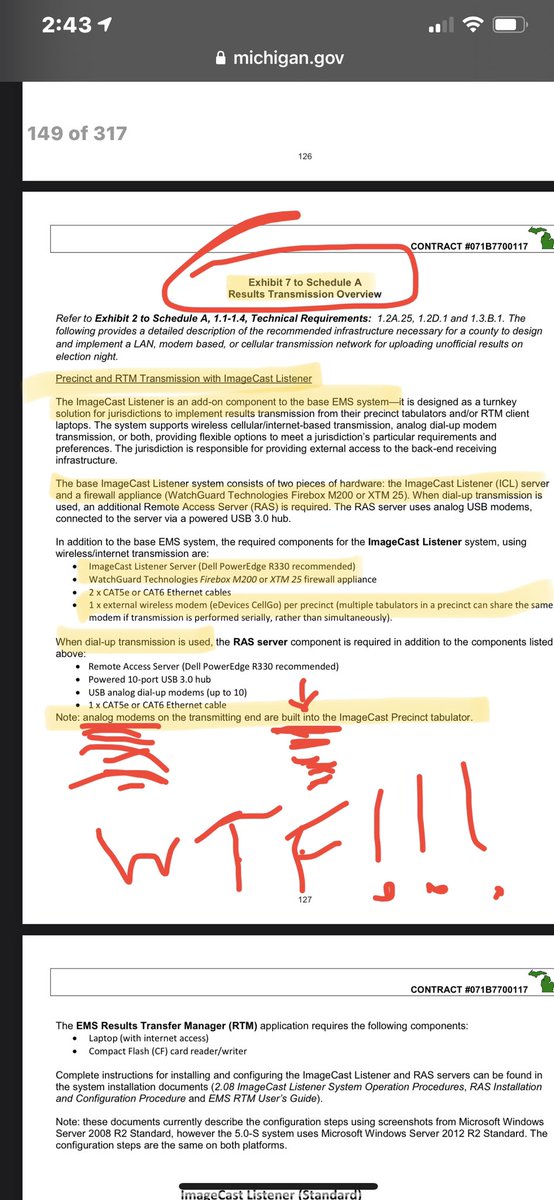
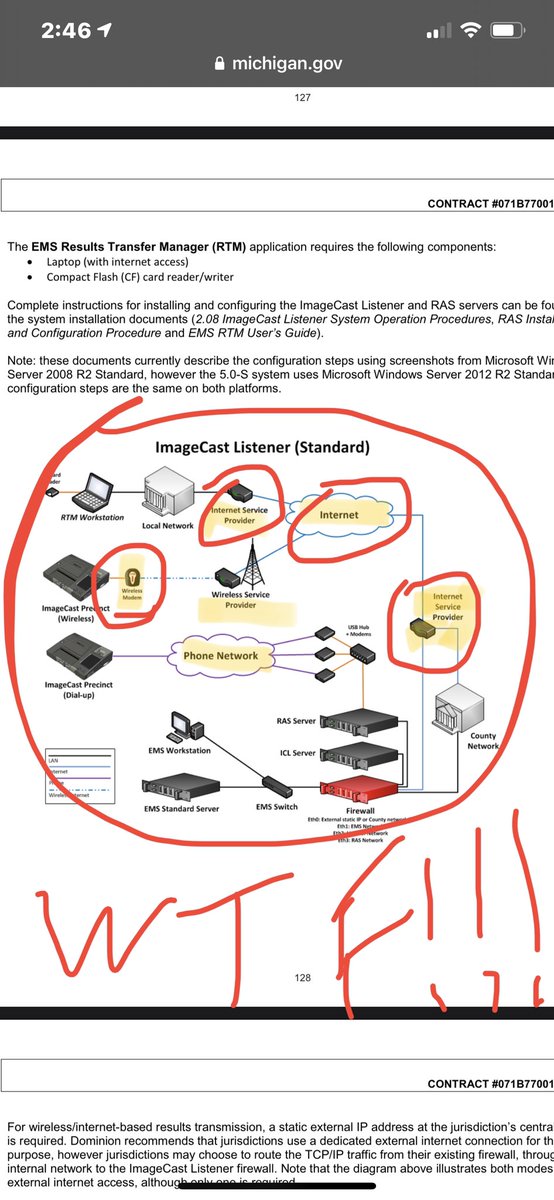
Wtf!!!! So Michigan was using cellular modems to connect wirelessly and to the internet, encryption can be broken, or packets intercepted with MIM.
Does everyone understand that this is a direct lie from @dananessel and @GovWhitmer ?
@mdeperno @CannConActual
Does everyone understand that this is a direct lie from @dananessel and @GovWhitmer ?
@mdeperno @CannConActual
https://twitter.com/JovanHPulitzer/status/1418641030421823495
So everyone understands, cellular modems are WORSE than a shared network infrastructure with firewall and gateway. At least you can confirm the security has been breached this way, with a cell modem somebody could utilize a stingray or cell simulator and MiM attack unnoticed.
Lookie lookie what I found…. 😎
michigan.gov/documents/loca…
Damn I’m good at this Google thing sometimes.
Backup saved already so don’t bother deleting it @GovWhitmer
@JovanHPulitzer @mdeperno @AmericanREI5


michigan.gov/documents/loca…
Damn I’m good at this Google thing sometimes.
Backup saved already so don’t bother deleting it @GovWhitmer
@JovanHPulitzer @mdeperno @AmericanREI5



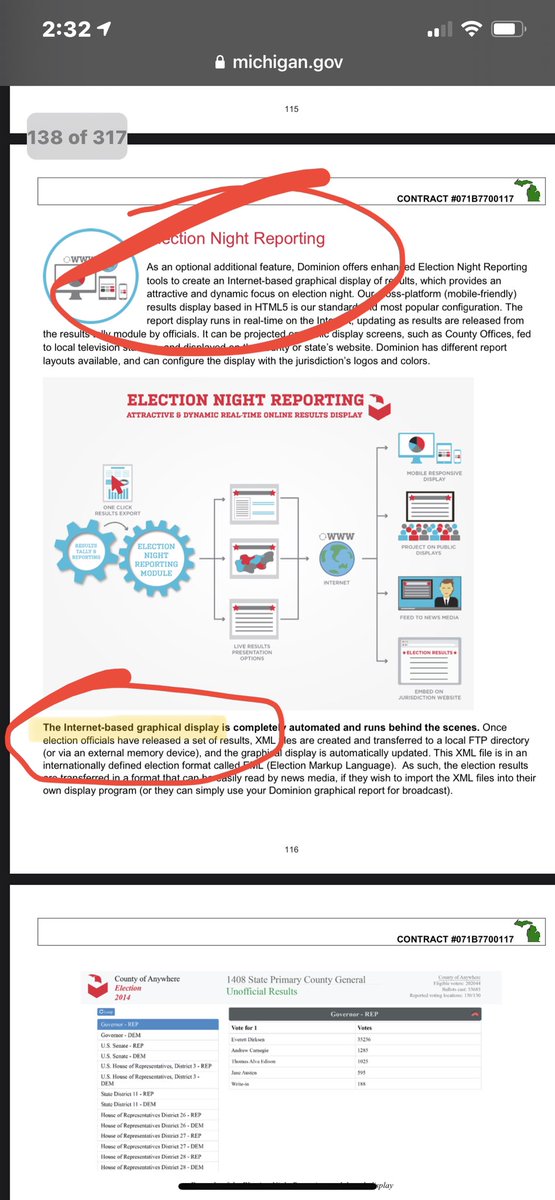
Wow Michigan purchased dominion systems when they were NOT EAC CERTIFIED. At the time of contract the system was NOT EAC certified. 
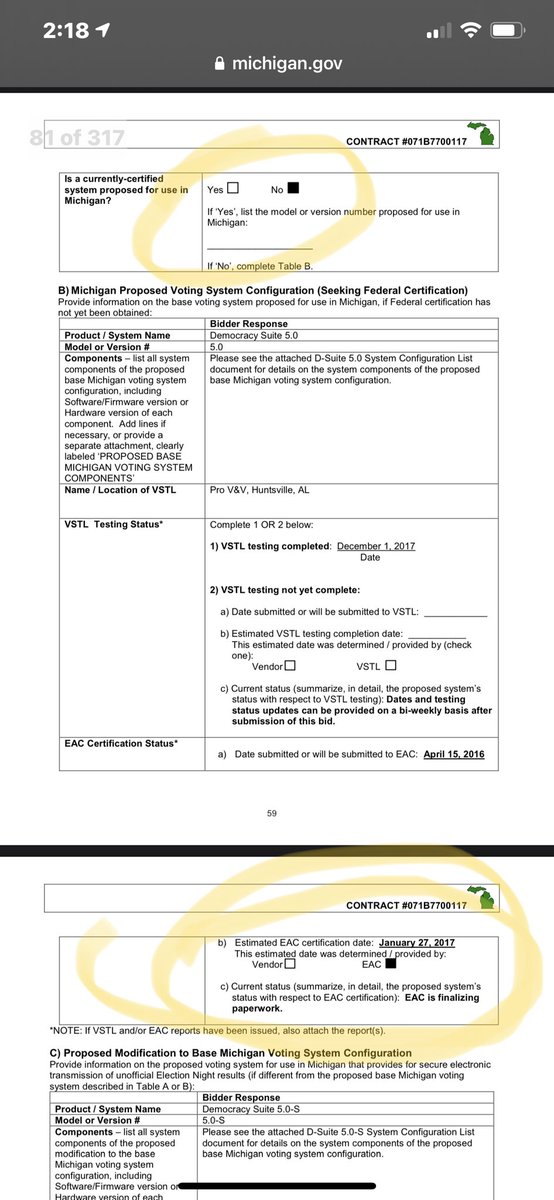
Ohhhhhh snap!! Hit pay dirt! The dominion tabulators in Michigan have been modified from the base bid to provide wireless access. They have an internal modem and can utilize 3G via an external module.
WIRELESS COMMS REMOVES EAC CERTIFICATION!!!!!!
@mdeperno @JovanHPulitzer
WIRELESS COMMS REMOVES EAC CERTIFICATION!!!!!!
@mdeperno @JovanHPulitzer
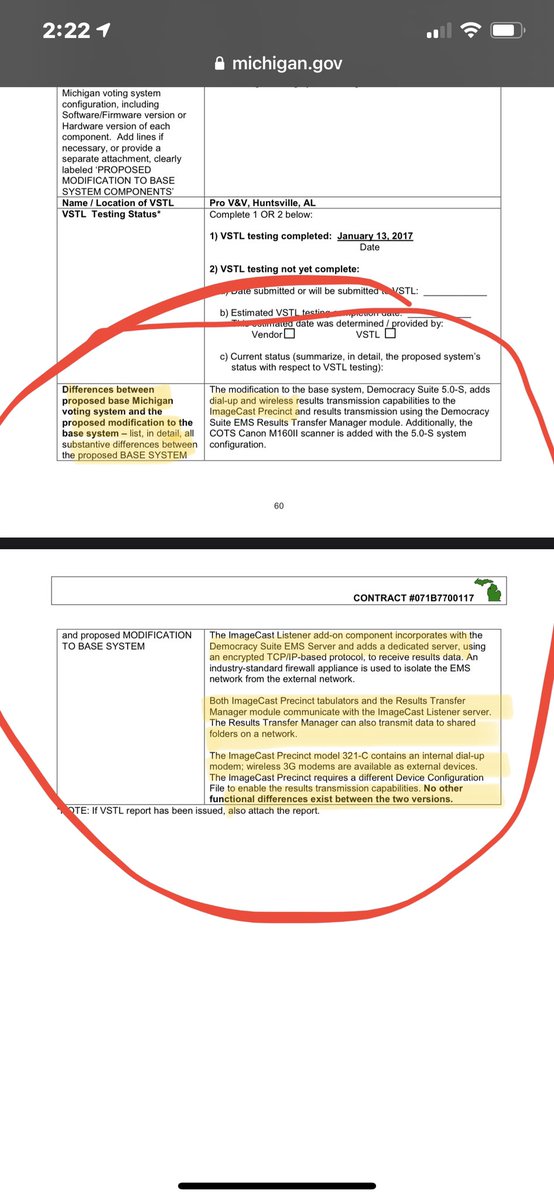
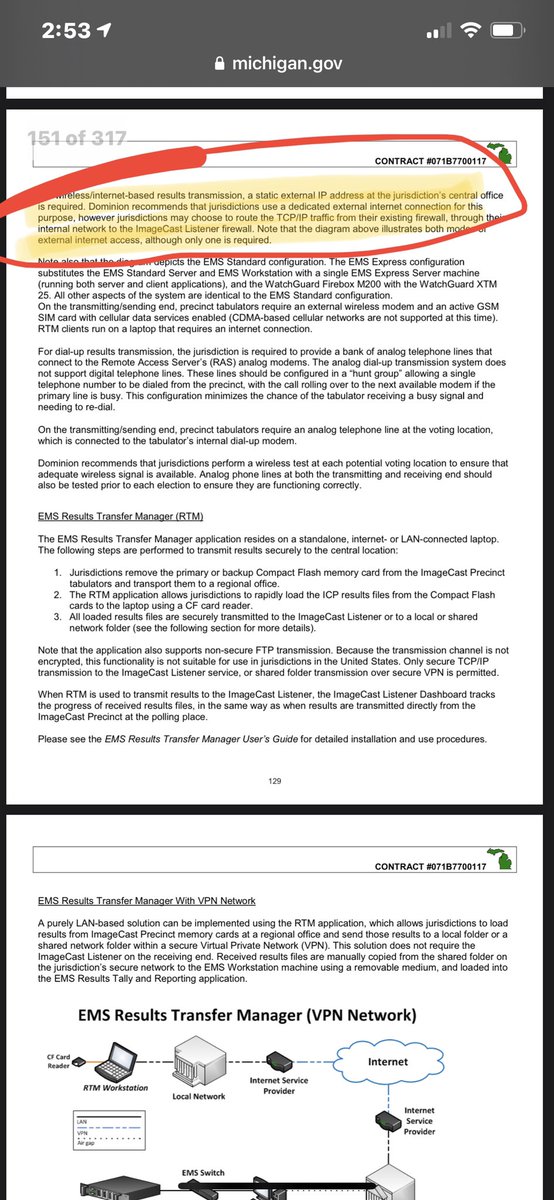
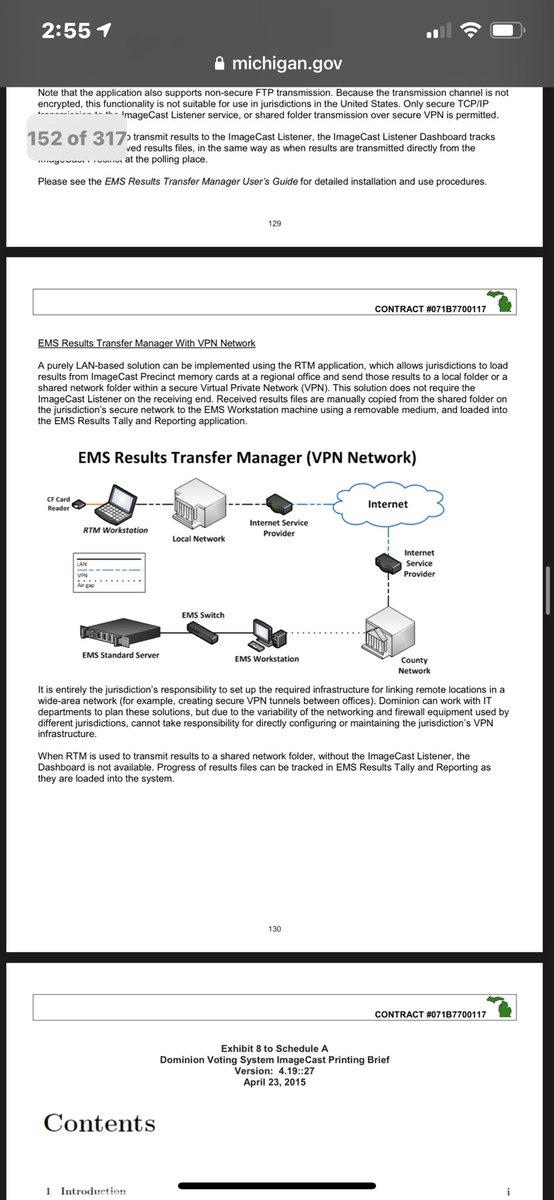
Oh would you look at that. The TABULATORS are connected wirelessly. In addition to the RTR server also having a wireless connection. The tabulators utilize a listener module (cellular switch/router basically) to communicate to the EMS.
Remember. This is straight from .gov


Remember. This is straight from .gov
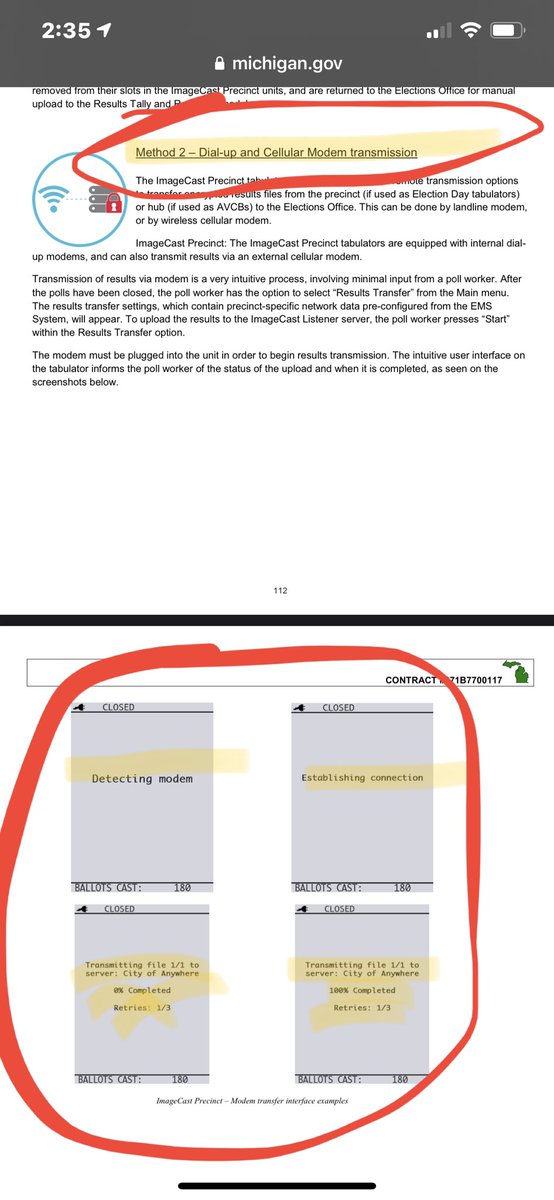
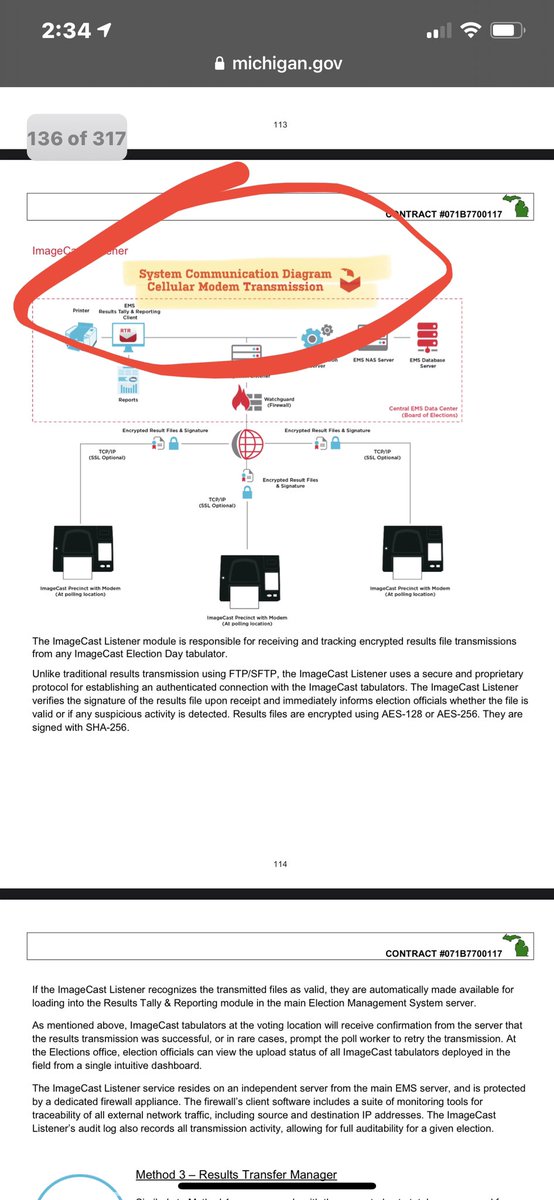
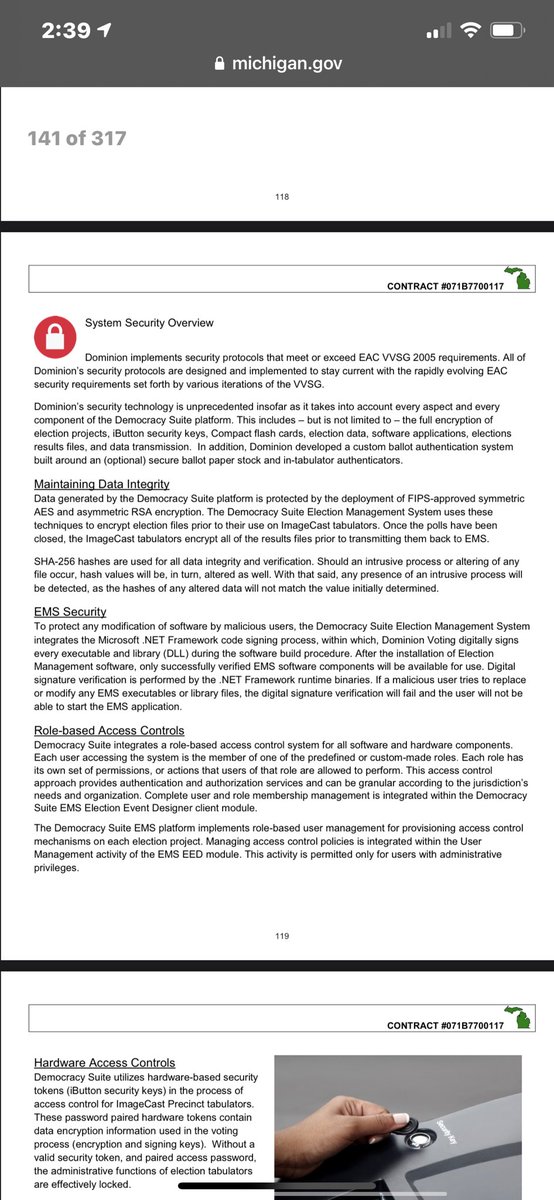
Because I am so sure that NO Hacker had cracked the .net framework and encryption that they are using, let alone back trace the election results RTR transmissions to know exactly where/what to attack if they monitored results server.
Oh wait… they did exactly this in past.
Oh wait… they did exactly this in past.
What. The. Actual. Fuck.
@GovWhitmer you have some explaining to do. This is STRAIGHT FROM YOUR CONTRACT!!!!!!
@mdeperno @pjcolbeck @CannConActual

@GovWhitmer you have some explaining to do. This is STRAIGHT FROM YOUR CONTRACT!!!!!!
@mdeperno @pjcolbeck @CannConActual
I literally am in shock right now. Literally.
EVERYTHING THEY HAVE SAID IS A BALL FACED LIE! To the judges in @mdeperno court cases, to the state, to the country.
To all of us.
I am sick to my stomach. I am going to sleep. Backups saved if they remove it.

EVERYTHING THEY HAVE SAID IS A BALL FACED LIE! To the judges in @mdeperno court cases, to the state, to the country.
To all of us.
I am sick to my stomach. I am going to sleep. Backups saved if they remove it.
@RaheemKassam @DarrenJBeattie @nataliegwinters @FoxNews @pepesgrandma @KandissTaylor @RepVernonJones @BarnettforAZ @FannKfann @SonnyBorrelli @WendyRogersAZ
Dominion lied, under oath, numerous times. Suggest you review contracts in your states. Thread got jumbled up by twttr.
Dominion lied, under oath, numerous times. Suggest you review contracts in your states. Thread got jumbled up by twttr.
• • •
Missing some Tweet in this thread? You can try to
force a refresh















