Meet @cryptoaover1111, @cryptodover1111, @cryptofover1111, @cryptoiover1111, @cryptopover1111, @cryptosover1111, @cryptogover1111, and @cryptolover1111, an octet of similarly-named Twitter accounts that you probably don't want to purchase.
cc: @ZellaQuixote
cc: @ZellaQuixote
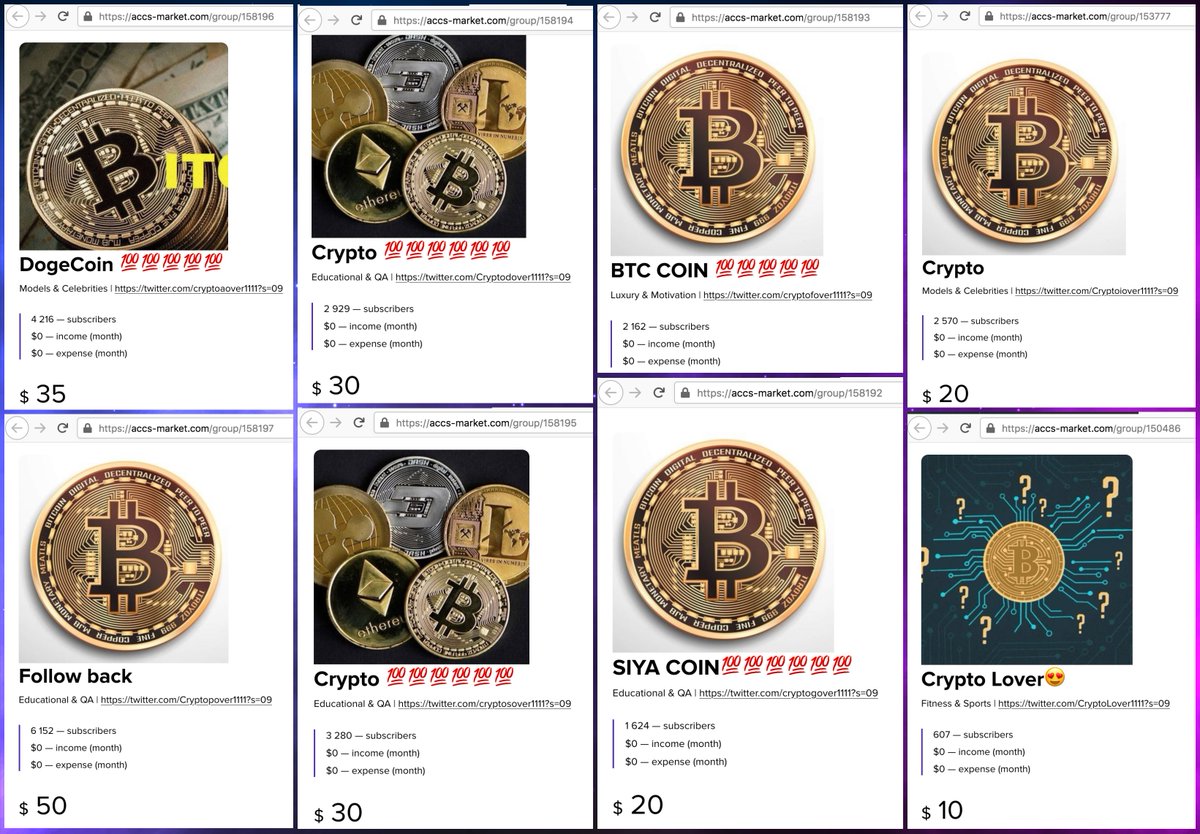
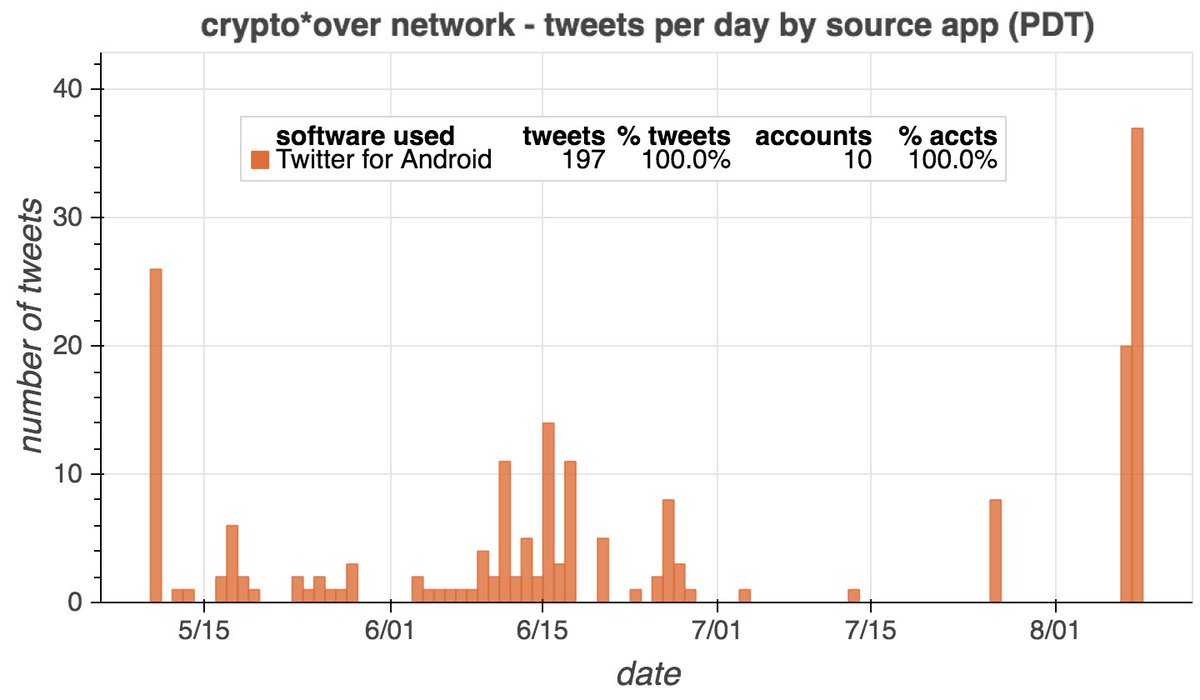
In addition to the eight accounts presently up for sale, we found two others with the same naming scheme: @cryptotover1111 and @cryptouover1111. All ten accounts were created in 2021 and have tweeted/retweeted a small amount of cryptocurrency content via Twitter for Android. 


(BTW, buying/selling Twitter accounts is against TOS, and websites offering such services should be regarded as potentially unsafe and one should take precautions when visiting then, such as using Tor.)
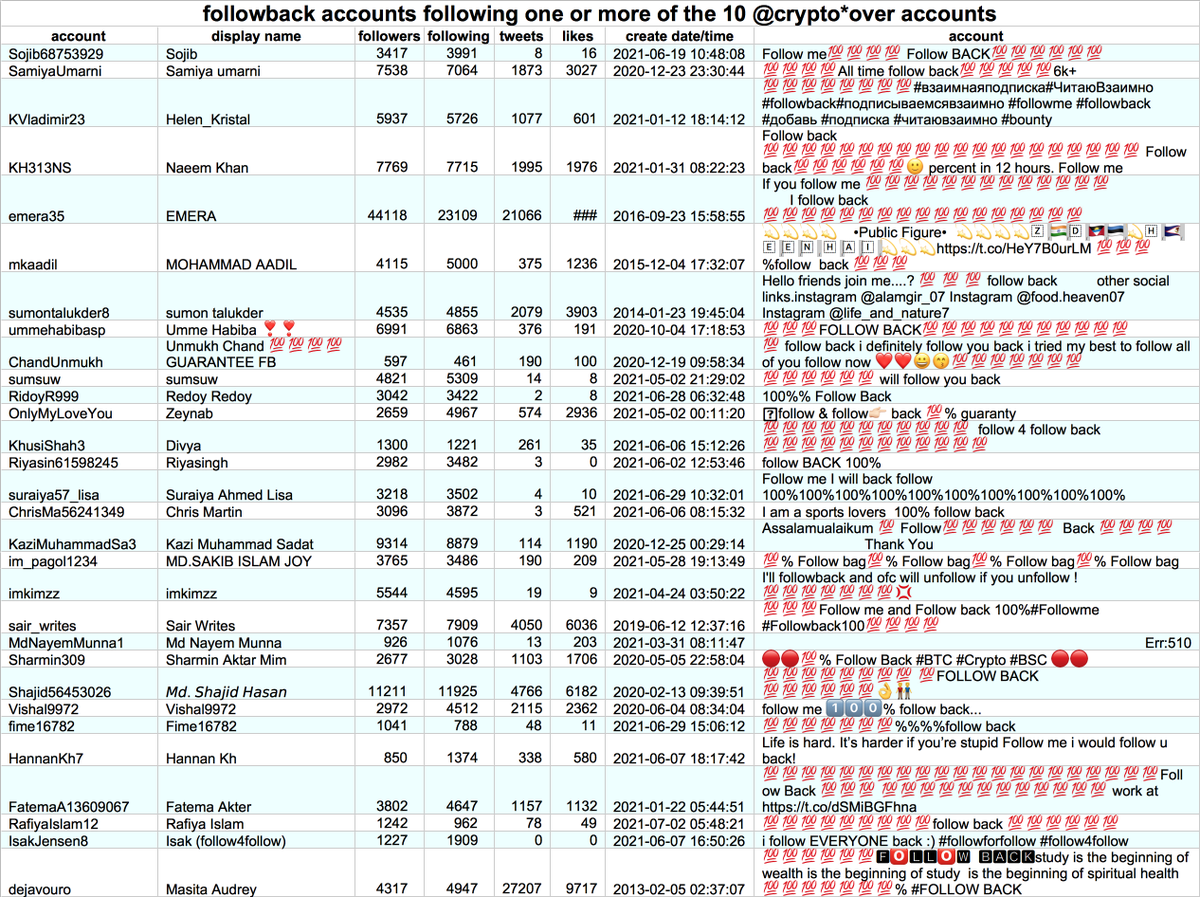
Interestingly, @cryptoaover1111 and its nine similarly-named friends have a lot of the same followers. These appear to be a mix of legitimate cryptocurrency accounts, followback accounts, and various spam networks.
4022 of the accounts following one or more of the ten crypto*over1111 accounts are "followback" accounts - accounts that advertise in their profiles that they will follow any account back. This table shows some examples: 
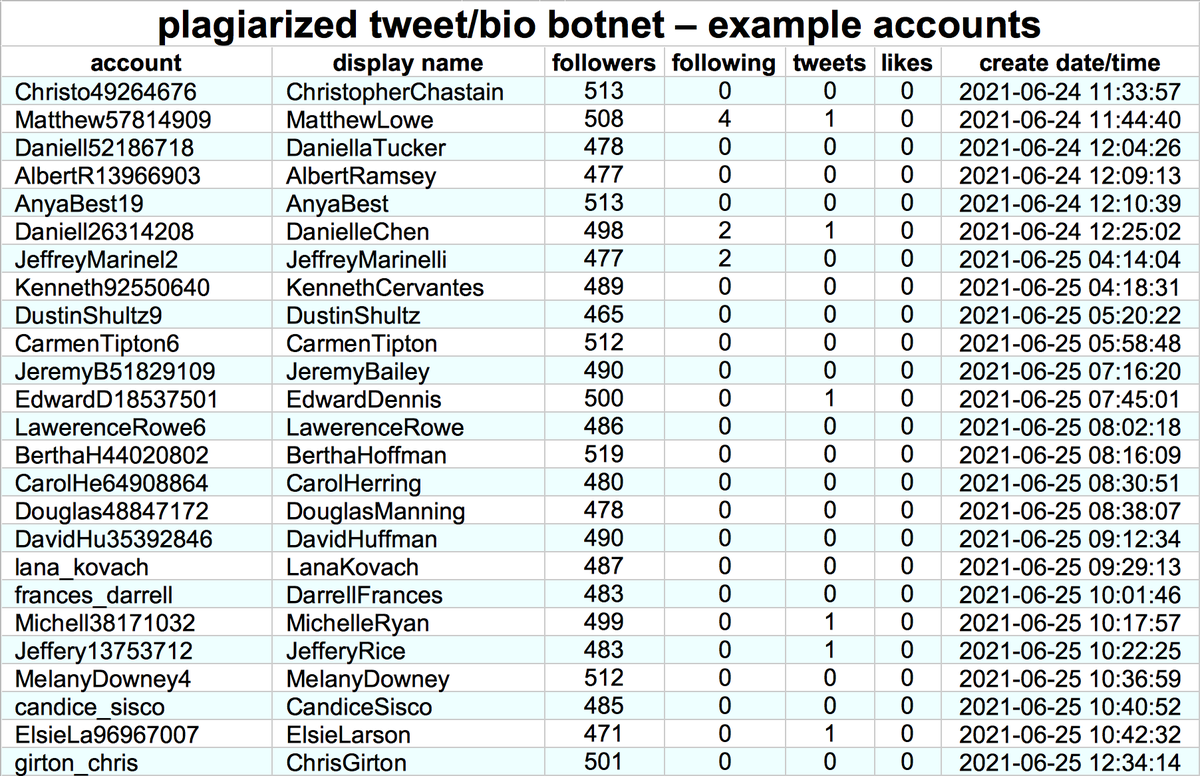
89 of the most recent followers of @cryptoaover1111 and its nine similarly-named friends are part of a much larger botnet whose members (so far) mostly follow one another. (The plagiarism mentioned in the graph title is explained further down the thread.) 
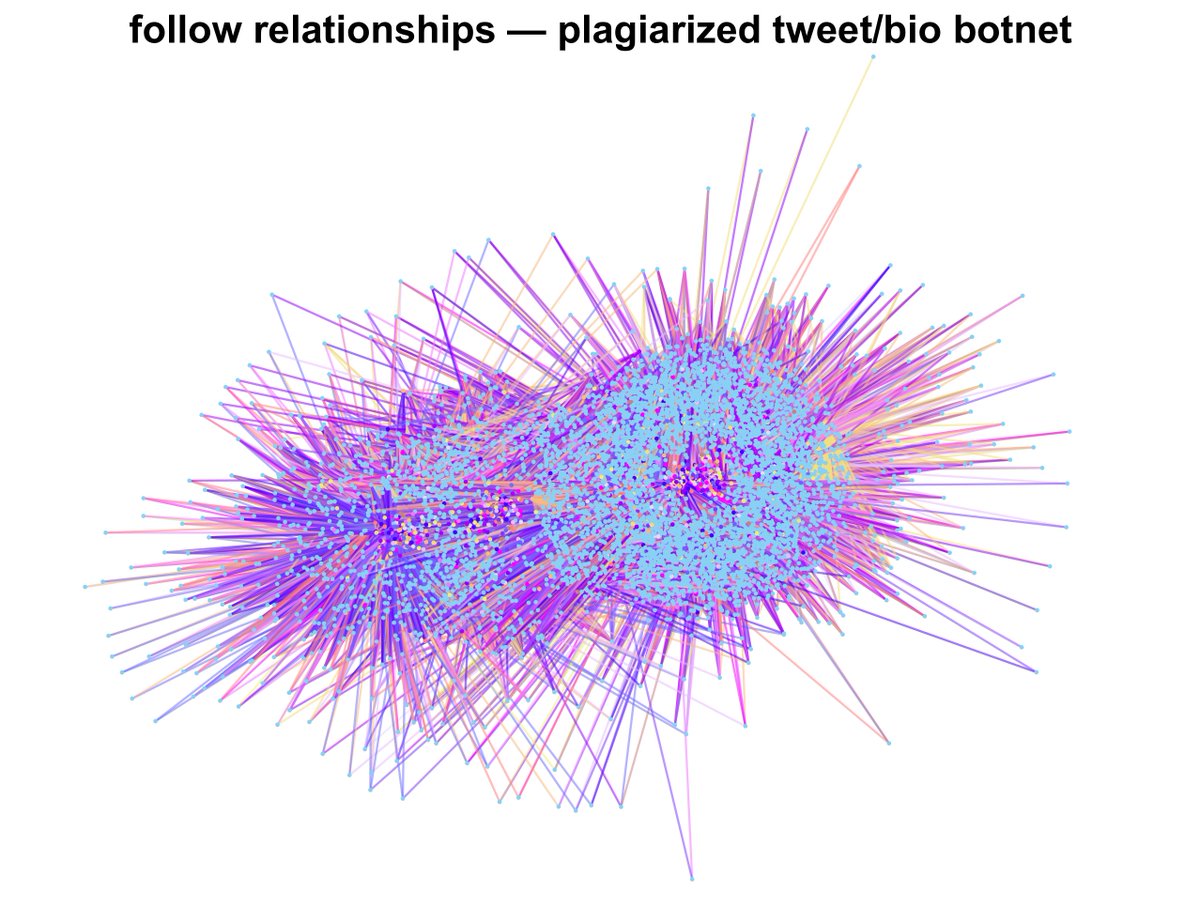
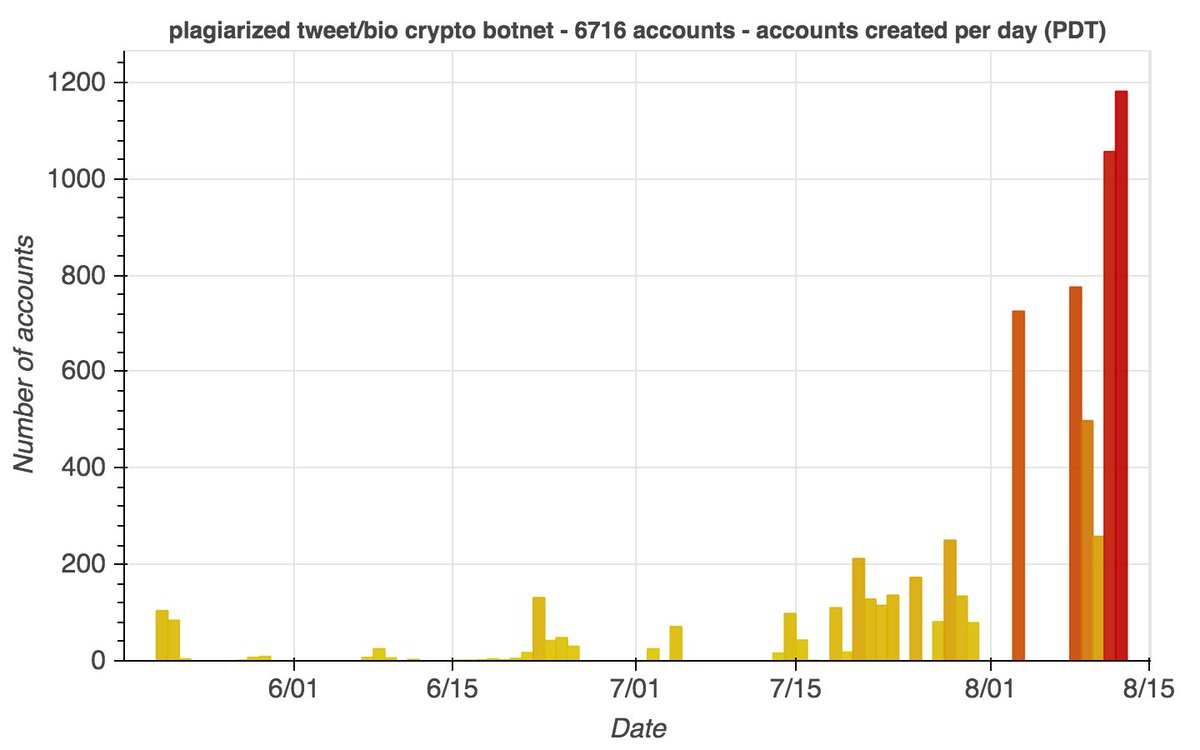
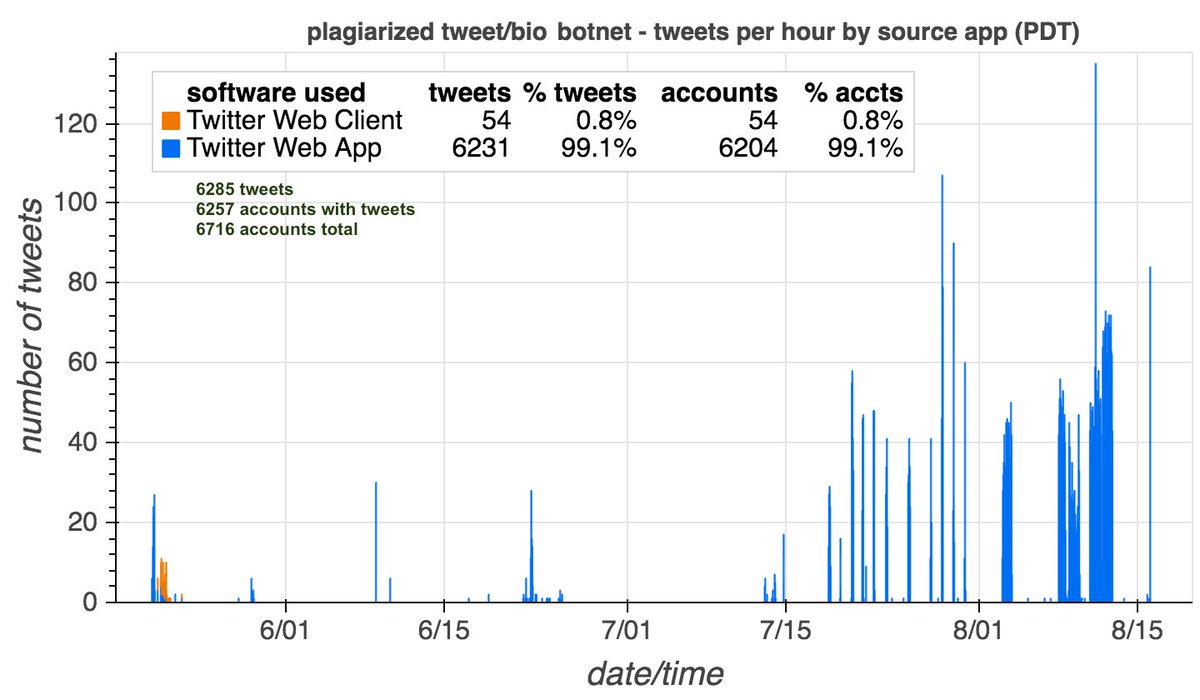
This botnet consists of 6716 accounts created in batches between May and August 2021. Most have tweeted exactly once, although some have no tweets and a few have up to five. None has ever liked a tweet, and all follow hundreds or thousands of other members of the botnet. 



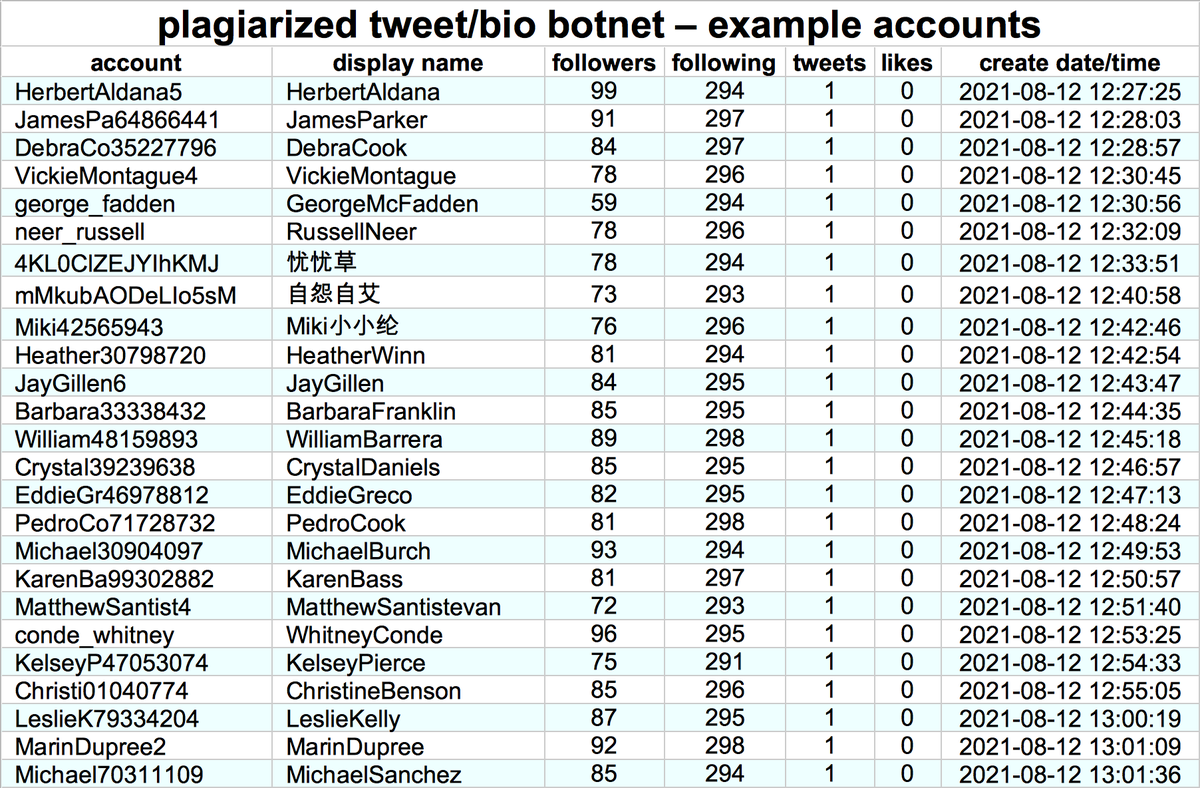

This network has (allegedly) posted all of its tweets thus far with Twitter web products, both the current "Twitter Web App" and the "Twitter Web Client" that Twitter shut down a year before these accounts were created. Tweet content is in a mix of English and Chinese. 

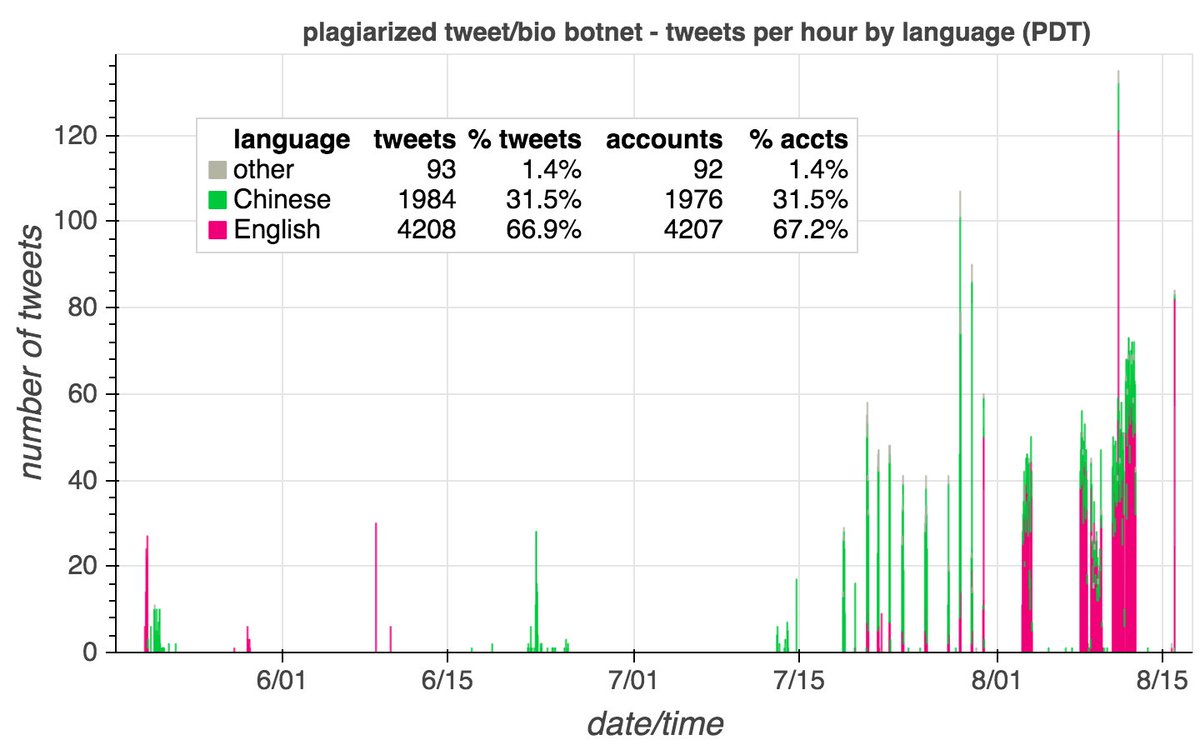
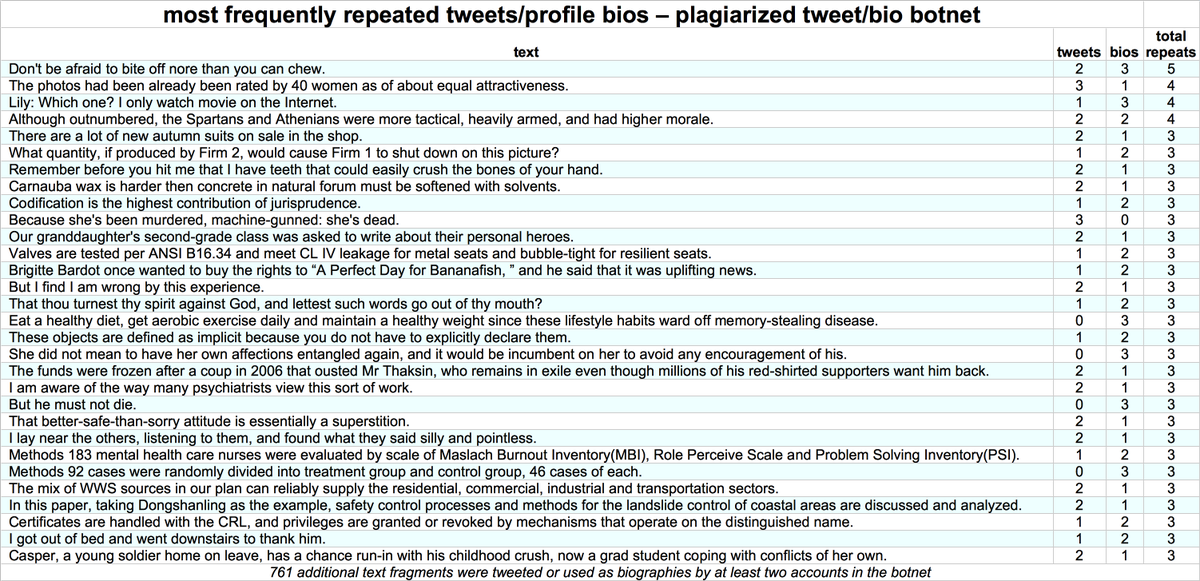
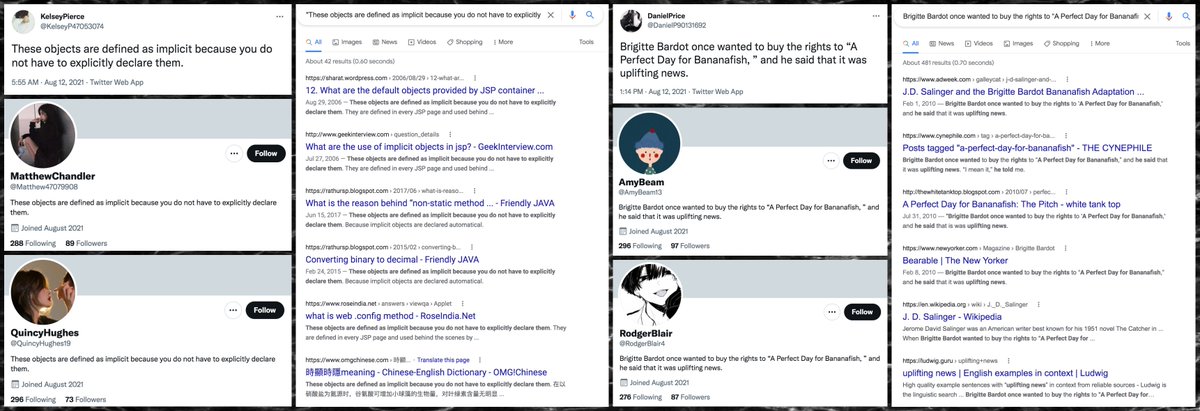
The accounts in this botnet use the same pool of repeated phrases for both tweet content and profile biographies. The phrases appear to be plagiarized from all over the internet, and are centered on no particular topic. 


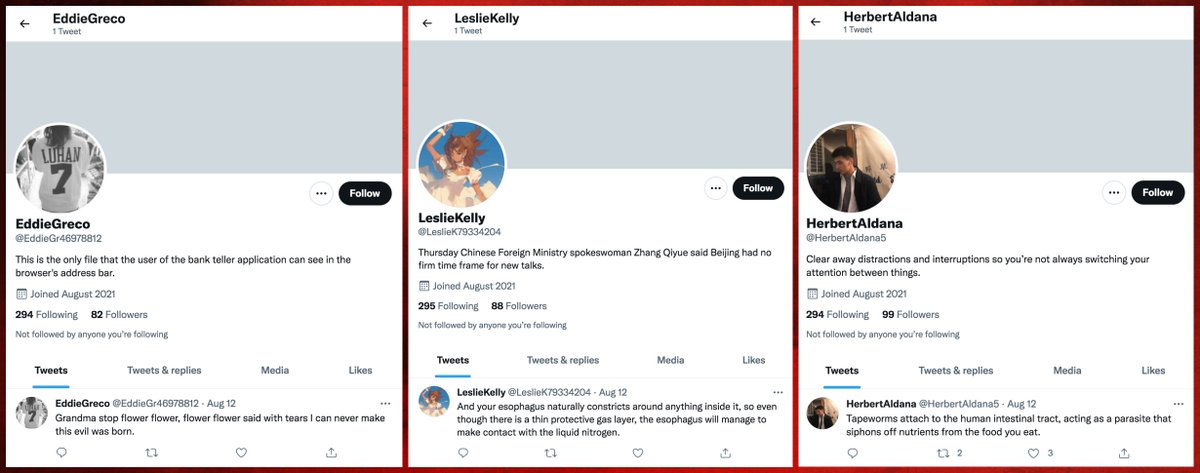
As with their tweet content and biographies, the profile images used by these bots are stolen. (A few have default pics rather than stolen ones.) TinEye and Google outperformed Yandex at tracking down previous uses of this set of images. 

• • •
Missing some Tweet in this thread? You can try to
force a refresh































