
This is part 3 of the thread about signatures in Ethereum.
In this thread, we will learn:
- Replay attacks
- Signature Malleability
- EIP-2
- Nonces
Ok, let's get started! 🏃♂️
In this thread, we will learn:
- Replay attacks
- Signature Malleability
- EIP-2
- Nonces
Ok, let's get started! 🏃♂️
https://twitter.com/immunefi/status/1480527067951292419
With signatures in Ethereum, there may be an issue if a valid signature might be used several times in other places where it’s not intended to be used.
This types of security issues are called Replay Attacks. ⏮🤺
More about them 👇
This types of security issues are called Replay Attacks. ⏮🤺
More about them 👇
Imagine a scenario where we have a function that transfers funds, but only when a valid signature is provided.
At first glance, the code looks good.
But the devil is in the details 😈
At first glance, the code looks good.
But the devil is in the details 😈

So, what happens in the code?
We check the address of the ECDSA signature by providing `v,r,s` values.
We compare the returned address with the owner address, and if it’s an owner, we proceed with the transfer of funds.
What are we missing? 🤔
We check the address of the ECDSA signature by providing `v,r,s` values.
We compare the returned address with the owner address, and if it’s an owner, we proceed with the transfer of funds.
What are we missing? 🤔
The problem is in the signed message.
The message only contains the receiver address and the amount to be unlocked.
There is nothing in the message that could prevent the same signatures from being used multiple times.😨
How can we prevent that?
The message only contains the receiver address and the amount to be unlocked.
There is nothing in the message that could prevent the same signatures from being used multiple times.😨
How can we prevent that?
To prevent the signature replay attack, we can store the signature we used in the `executed` mapping.
This way, whenever someone would want to replay our signature, it would fail, as we can check if this signature was already used by simply checking the mapping.
Code below:
This way, whenever someone would want to replay our signature, it would fail, as we can check if this signature was already used by simply checking the mapping.
Code below:
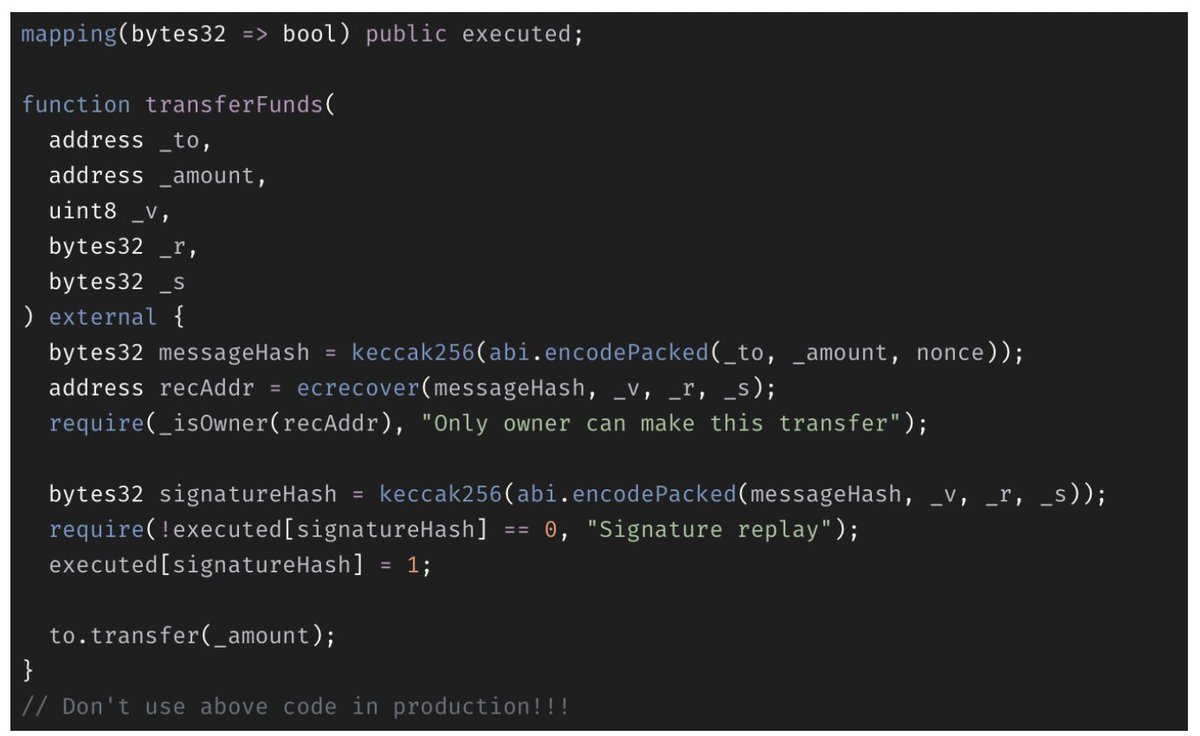
There are still issues with the code above ☝️
It does not follow the recommended best practice for signature verification, especially the `S` value.
This can lead to signature malleability.
What does that mean?
It does not follow the recommended best practice for signature verification, especially the `S` value.
This can lead to signature malleability.
What does that mean?
Within Solidity, an ECDSA signature is represented by its *r, s* and *v* values.
The relationship between the public key, the message hash, *r*, *s*, and *v* can be checked to ensure that only the person who knows the corresponding *private* key calculates *r*, *s*, and *v*...
The relationship between the public key, the message hash, *r*, *s*, and *v* can be checked to ensure that only the person who knows the corresponding *private* key calculates *r*, *s*, and *v*...
...However, due to the symmetric structure of elliptic curves, for every set of *r*, *s*, and *v*, there is another set of *r*, *s*, and *v* that *also* has the same precise mathematical relationship.
This results in TWO valid signatures 🤯
This results in TWO valid signatures 🤯
Fortunately, it’s easy to detect the duplicate signature 😎
Not going much into mathematical details, we need to choose the proper "half" of the eliptic curve.
Value of *s* is the one that helps us determine which half we need.
Not going much into mathematical details, we need to choose the proper "half" of the eliptic curve.
Value of *s* is the one that helps us determine which half we need.
As seen below, an Elliptic Curve is symmetric on the X-axis, meaning two points can exist with the same X value.
We can carefully adjust *s* to produce a valid signature for the same *r* on the other side of the X-axis.
We can carefully adjust *s* to produce a valid signature for the same *r* on the other side of the X-axis.
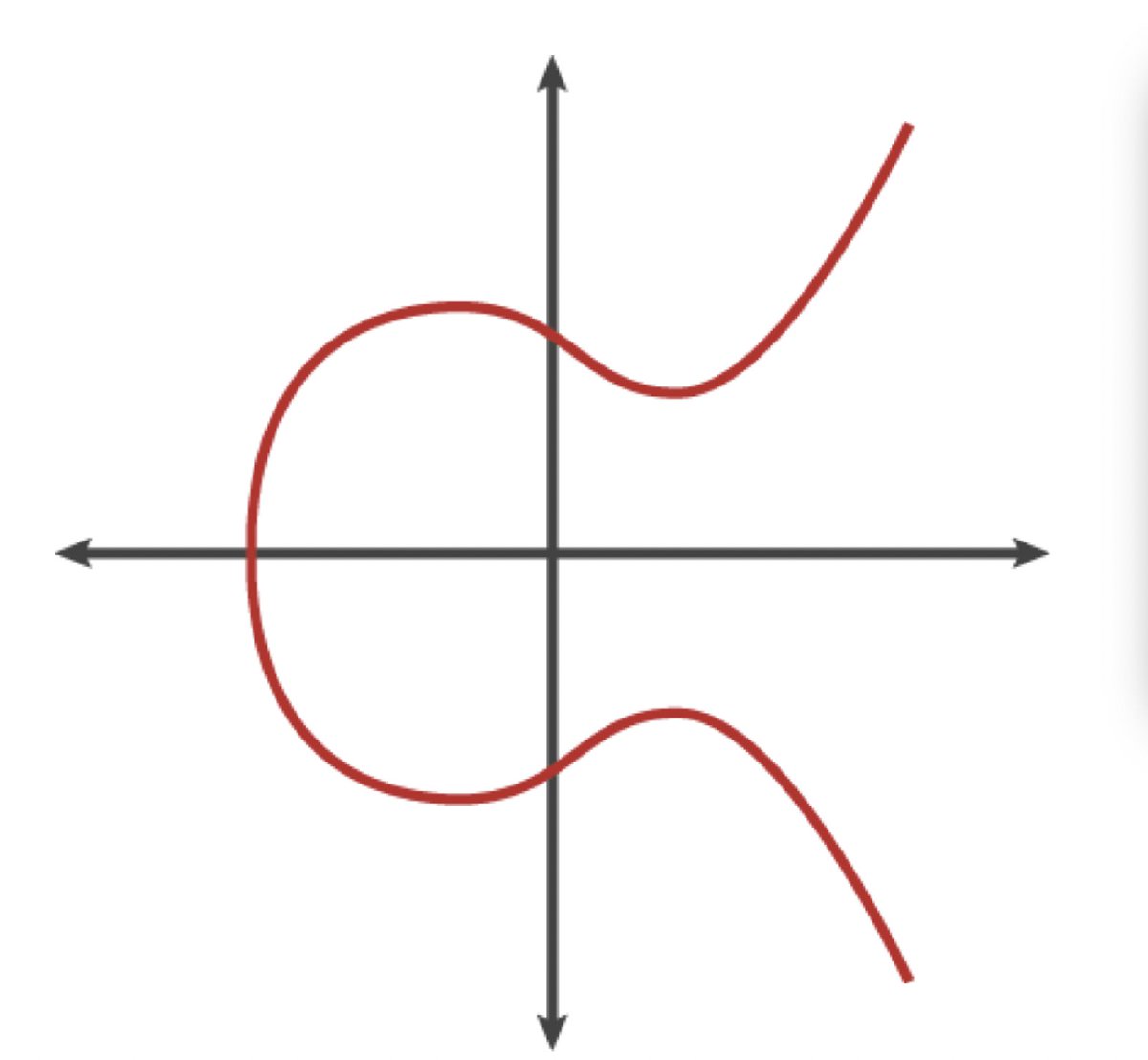
The meaning behind all of this is we can invert one valid signature to get another valid signature which will still be valid and basically replay a signature!
There is a way to prevent that, and the first major hard-fork of Ethereum introduced a solution to this:
EIP-2
There is a way to prevent that, and the first major hard-fork of Ethereum introduced a solution to this:
EIP-2
EIP-2 introduced limits on the *s* values to prevent signature malleability by only considering lower levels of *s* as valid.
By restricting valid range, EIP-2 effectively removes half the points from the group, ensuring there is at most one valid point at each **x** coordinate.
By restricting valid range, EIP-2 effectively removes half the points from the group, ensuring there is at most one valid point at each **x** coordinate.
EIP-2 was introduced into EVM, it didn’t affect the precompiled contract `ecrecover`
So, whenever we’re using plain `ecrecover`, we’re still prone to signature malleability!
Don’t worry, because OpenZeppelin created an appropriate library ECDSA.sol that solves this issue.
So, whenever we’re using plain `ecrecover`, we’re still prone to signature malleability!
Don’t worry, because OpenZeppelin created an appropriate library ECDSA.sol that solves this issue.
Another way to combat signature malleability *and* replay is the usage of an application-level nonce.
“Nonce” is cryptographer short-hand for “number used once”.
We can use a nonce for every signature and store the next nonce inside the contract.
“Nonce” is cryptographer short-hand for “number used once”.
We can use a nonce for every signature and store the next nonce inside the contract.

This covers the most *common* issues with signatures.
We still need to cover EIP-712 but that's in another 🧶
And if you prefer reading a blog post instead of a 🧵, check out awesome article at our Medium:
medium.com/immunefi/intro…
We still need to cover EIP-712 but that's in another 🧶
And if you prefer reading a blog post instead of a 🧵, check out awesome article at our Medium:
medium.com/immunefi/intro…
If you enjoyed this thread, please like and retweet to share the knowledge at #immunefischool and other Web3 communities.
The more you know, the safer the ecosystem!⛑
See ya in the next one!👋
The more you know, the safer the ecosystem!⛑
See ya in the next one!👋
• • •
Missing some Tweet in this thread? You can try to
force a refresh




