
1/ Windows Error Reporting (WER) can provide investigators with a wealth of data including:
• SHA1 hashes of crashed processes
• Snapshot of process trees at time of crash
• Loaded modules of crash
• Process minidumps
#DFIR #Threathunting
See 🧵 for new #Velociraptor artefact
• SHA1 hashes of crashed processes
• Snapshot of process trees at time of crash
• Loaded modules of crash
• Process minidumps
#DFIR #Threathunting
See 🧵 for new #Velociraptor artefact

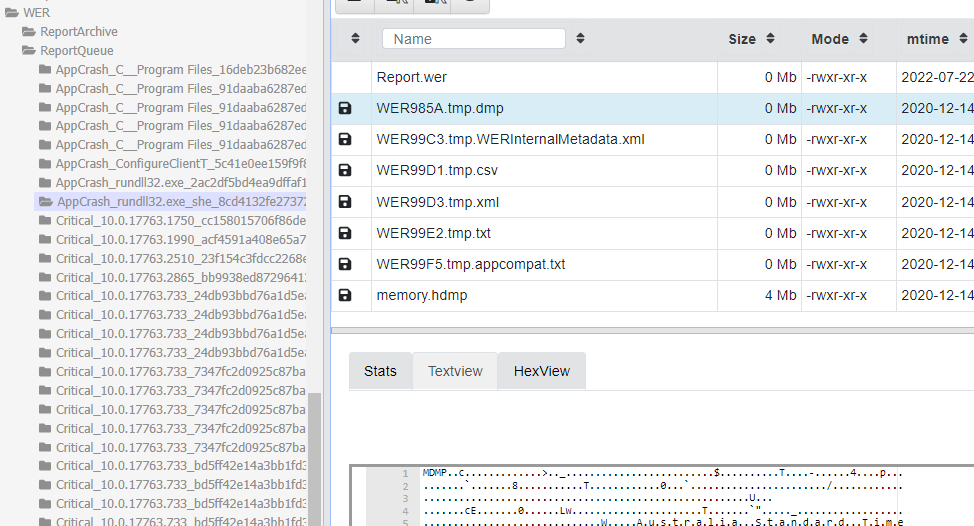
2/ WER files are found in the following locations which include a range of information to typically address an application crash, however we can use it for investigation!
C:/Users/*/AppData/Local/Microsoft/Windows/WER
C:/ProgramData/Microsoft/Windows/WER

C:/Users/*/AppData/Local/Microsoft/Windows/WER
C:/ProgramData/Microsoft/Windows/WER

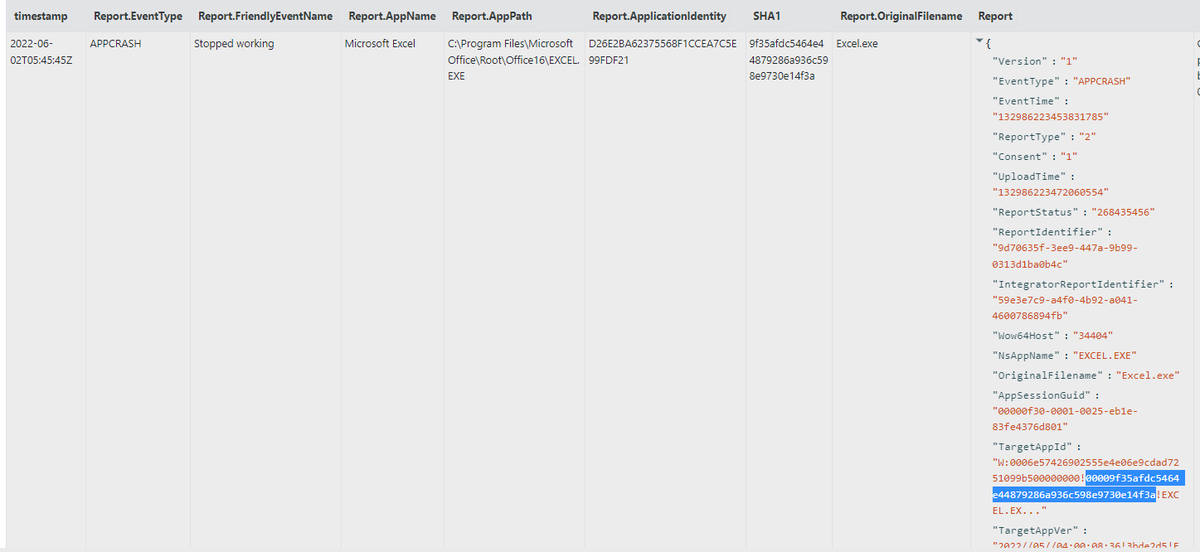
3/ The "Report.wer" file includes binary information and binary path. In Windows 10 and above the field "TaskAppId" contain the SHA1 hash of the process (similar to Amcache). 


4/ WER registry settings can be found here:
• HKU/Software/Microsoft/Windows/Windows Error Reporting
• HKLM/Software/Microsoft/Windows/Windows Error Reporting
In testing it appears Windows Server has more of these features on by default.
• HKU/Software/Microsoft/Windows/Windows Error Reporting
• HKLM/Software/Microsoft/Windows/Windows Error Reporting
In testing it appears Windows Server has more of these features on by default.
5/ You can see the process list at the time of the crash in a CSV file "WERXXX.tmp.csv". You can also see the process and parent process information the "WERInternalMetadata.xml" file.
Commonly we see rundll32 crashing (pic) when it is used to execute malware, or injected into.

Commonly we see rundll32 crashing (pic) when it is used to execute malware, or injected into.


6/ These files are all parsed by the @velocidex #Velociraptor artefact Windows.System.WindowsErrorReporting in the artefact exchange - docs.velociraptor.app/exchange/artif… 

7/ Bonus: If crash dumps are enabled you can find memory dumps saved in the WER Folder and:
C:/Users/*/AppData/Local/CrashDumps/*.dmp
You can use #yara and #Velociraptor (Generic.Detection.Yara.Glob) to scan minidump files for malware. Windbg can also be used to analyse these.

C:/Users/*/AppData/Local/CrashDumps/*.dmp
You can use #yara and #Velociraptor (Generic.Detection.Yara.Glob) to scan minidump files for malware. Windbg can also be used to analyse these.


8/ If you want to read more about WER, check out:
-0xdabbad00.com/wp-content/upl… (@0xdabbad00)
-medium.com/dfir-dudes/amc… (@martinkorman)
-journeyintoir.blogspot.com/2014/02/explor… (@corey_harrell)
docs.microsoft.com/en-us/windows/…
-0xdabbad00.com/wp-content/upl… (@0xdabbad00)
-medium.com/dfir-dudes/amc… (@martinkorman)
-journeyintoir.blogspot.com/2014/02/explor… (@corey_harrell)
docs.microsoft.com/en-us/windows/…
9/ Adding some extra info. Just like Amcache, the SHA1 hash in Report.wer is only based on the first 31,457,280 bytes, so keep it in mind for large files.
Also @bmcder02 has a awesome blog on analysing cobalt strike beacons from WER dumps bmcder.com/blog/extractin…
Also @bmcder02 has a awesome blog on analysing cobalt strike beacons from WER dumps bmcder.com/blog/extractin…
• • •
Missing some Tweet in this thread? You can try to
force a refresh



