Is there a good way to use the Wayback Machine to view the hashes of deleted Git repositories?
My naive poking around in the Wayback/GitHub Web interface keeps bringing me to dead UI elements (as expected). But maybe there’s a static page I should know to look for. 
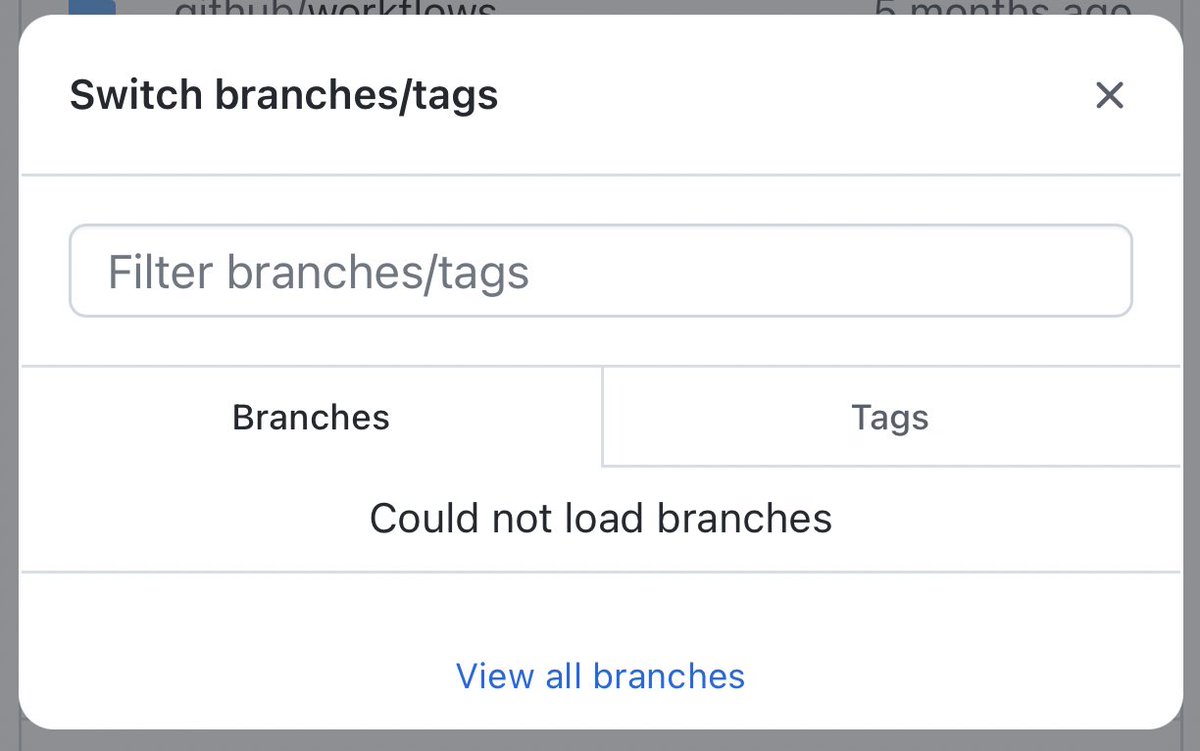
The sudden deletion of important Git repos from GitHub is now a thing, and while that *shouldn’t* mean all copies of the software are gone (thanks to Git being decentralized), it does make it hard to verify purported clones w/o knowing the hashes.
This service seems pretty great!
https://twitter.com/rgrunblatt/status/1558494230179373056
• • •
Missing some Tweet in this thread? You can try to
force a refresh