BREAKING: #TikTok admits to using app data to spy on journalists including @CristinaCriddle & people connected to them.
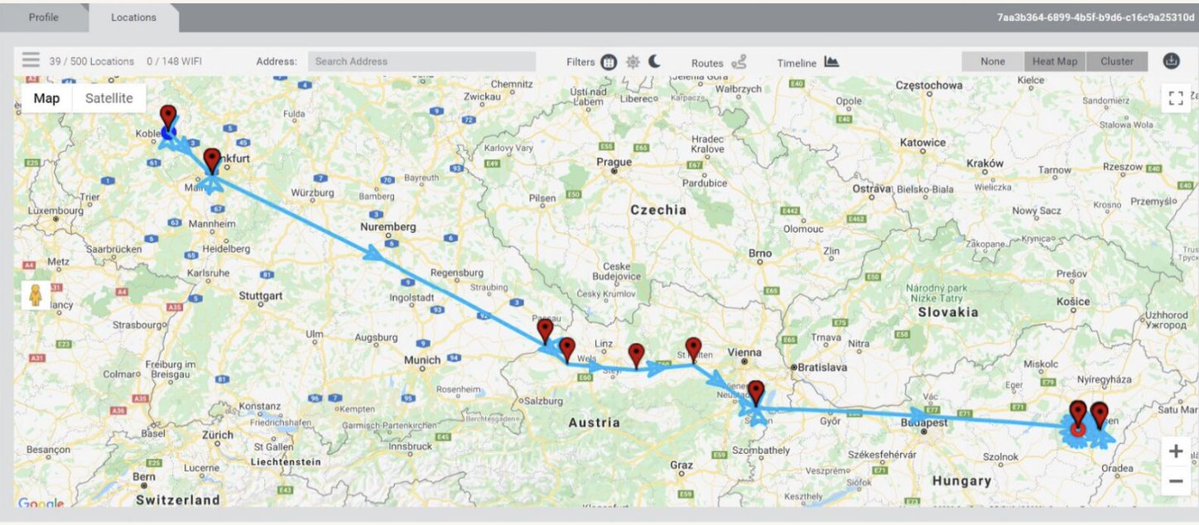
Tracked their movements.
By @MsHannahMurphy
ft.com/content/e873b9…
Tracked their movements.
By @MsHannahMurphy
ft.com/content/e873b9…

Looks like #TikTok is trying the "few bad apples" approach with their journalist spying internal investigation. 

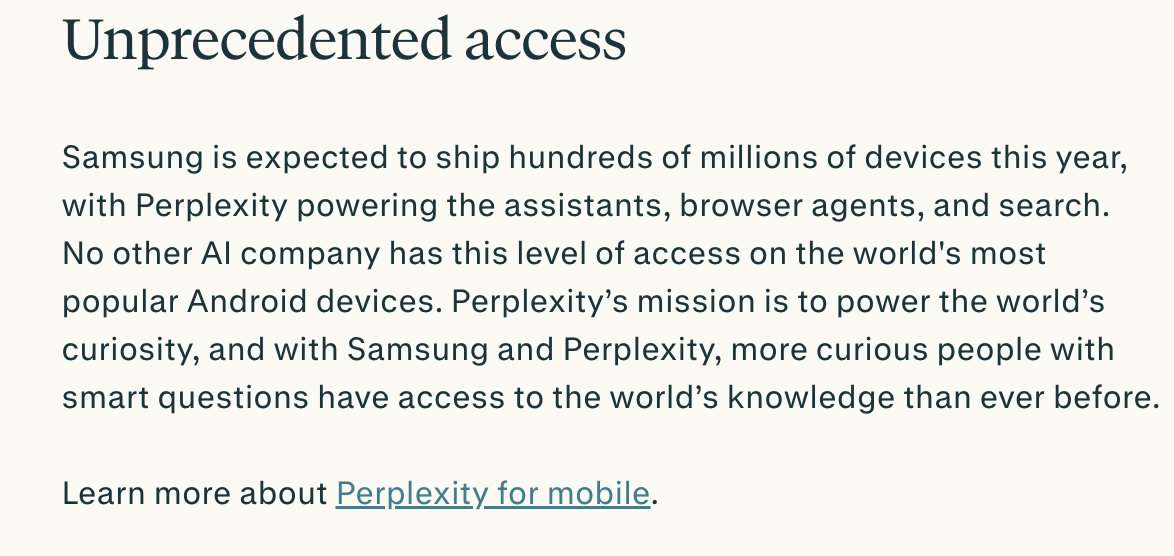
#TikTok spying on journalists proves that #LocationPrivacy matters.
You have no idea who is getting & leveraging logs of your movements.
Right now, the whole issue is a wild west in most jurisdictions.
Including the US.
You have no idea who is getting & leveraging logs of your movements.
Right now, the whole issue is a wild west in most jurisdictions.
Including the US.
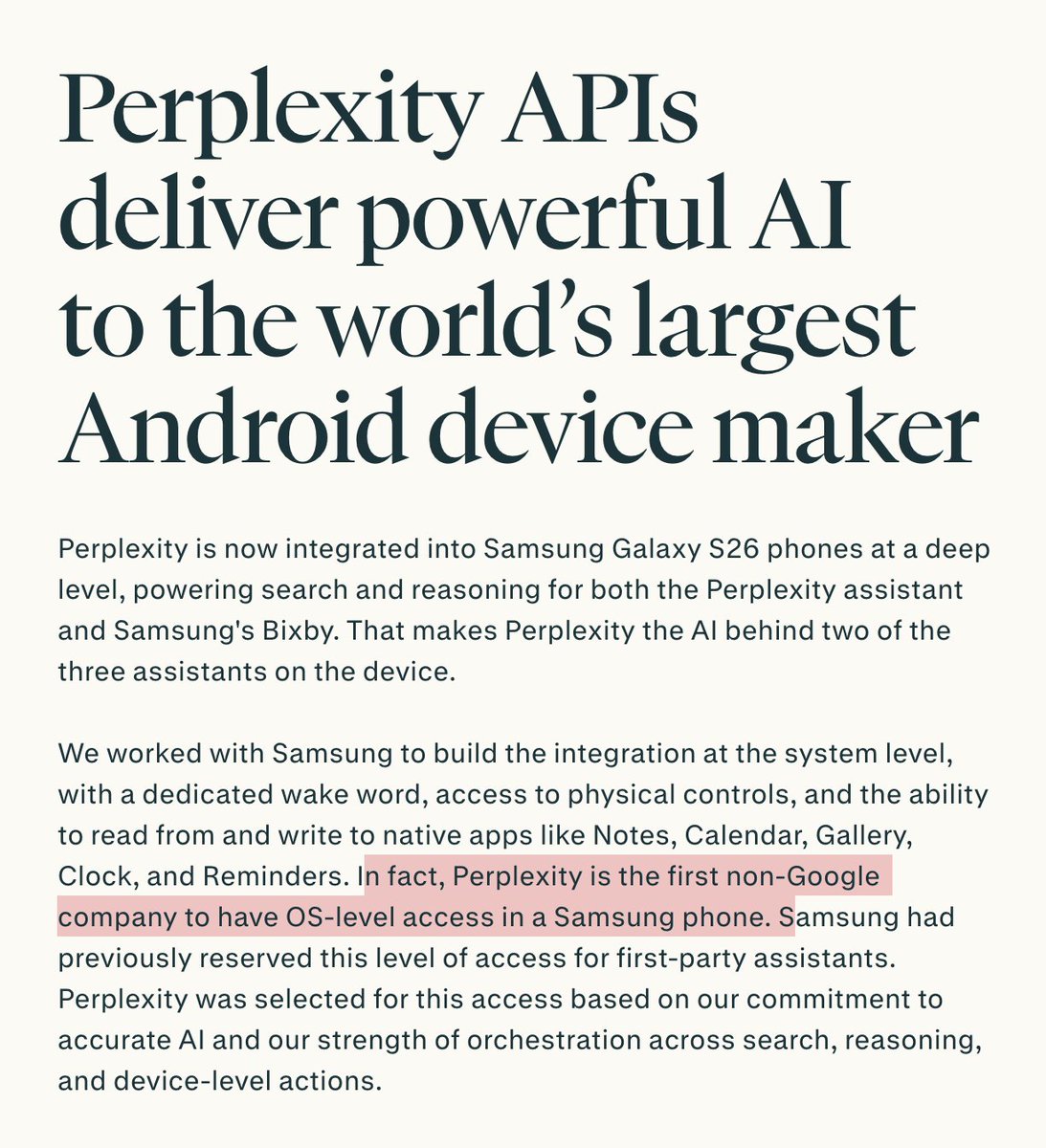
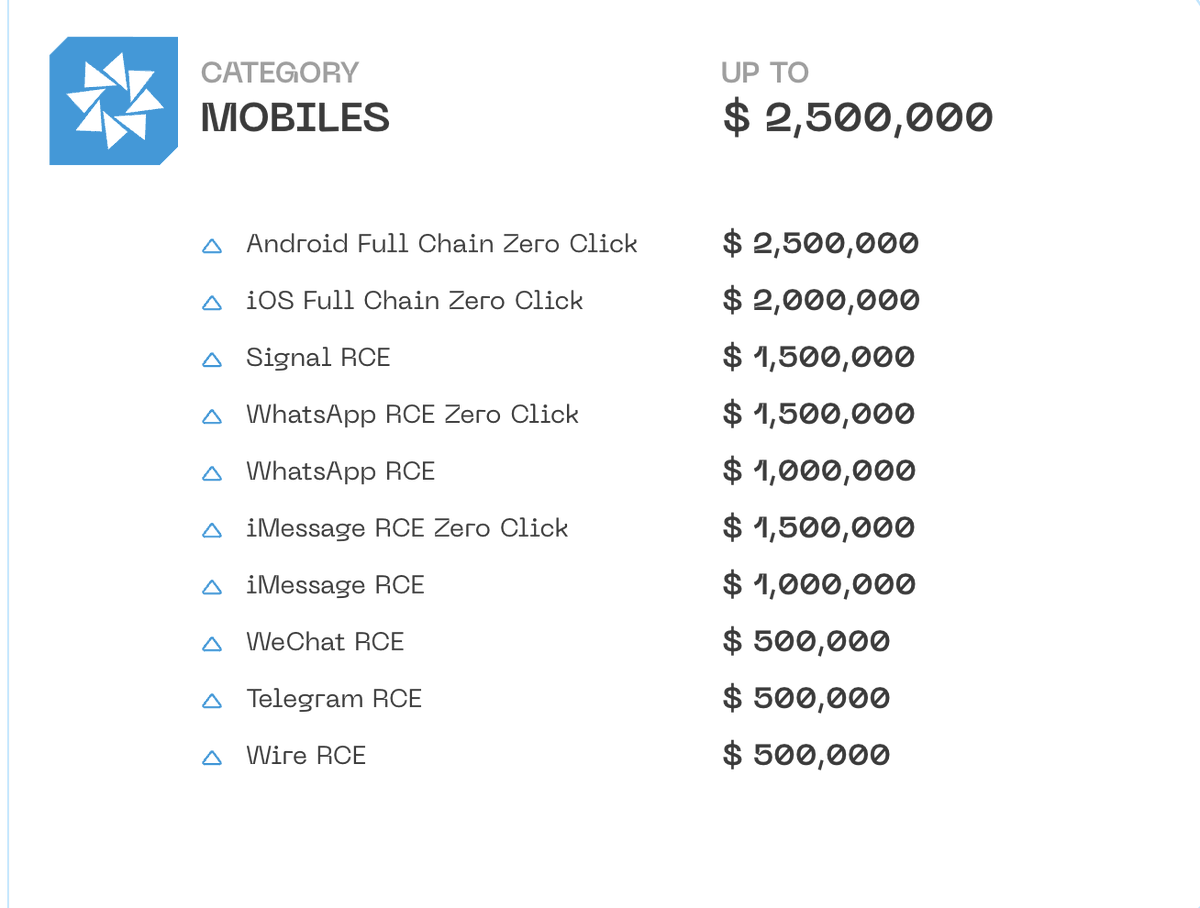
The #TikTok spying situation shows: an app doesn't need to have any special design features to be turned into an espionage tool.
So many apps soak up much more than they should.
All it takes is the desire and access to the backend... and that data is going to be abused.
So many apps soak up much more than they should.
All it takes is the desire and access to the backend... and that data is going to be abused.
Another way to parse the few-bad-apples-defense?
A bad thing was kept to a small group within #TikTok in an effort to keep it a secret...
A bad thing was kept to a small group within #TikTok in an effort to keep it a secret...

You probably have apps where you do *work* things.
But you might also have apps that feel more personal.
And that contain your 'personal' social graph.
Like #TikTok.
But those fun apps can bite.
And be leveraged to track your work activities. And those of your friends.
But you might also have apps that feel more personal.
And that contain your 'personal' social graph.
Like #TikTok.
But those fun apps can bite.
And be leveraged to track your work activities. And those of your friends.

UPDATE: @Forbes reports that #TikTok ALSO tracked multiple Forbes journalists.
This is very bad.
But it gets worse...
By @ebakerwhite forbes.com/sites/emilybak…
This is very bad.
But it gets worse...
By @ebakerwhite forbes.com/sites/emilybak…

As @ebakerwhite reports: in October, TikTok explicitly said they didn't spy on journalists.
That's exactly what they had done.
That's exactly what they had done.

The @Forbes journalists we now know were covertly spied on by #TikTok: @ebakerwhite @SchwabKatharine & @richardjnieva.
It makes you wonder: just what else has TikTok done?
It makes you wonder: just what else has TikTok done?

• • •
Missing some Tweet in this thread? You can try to
force a refresh