
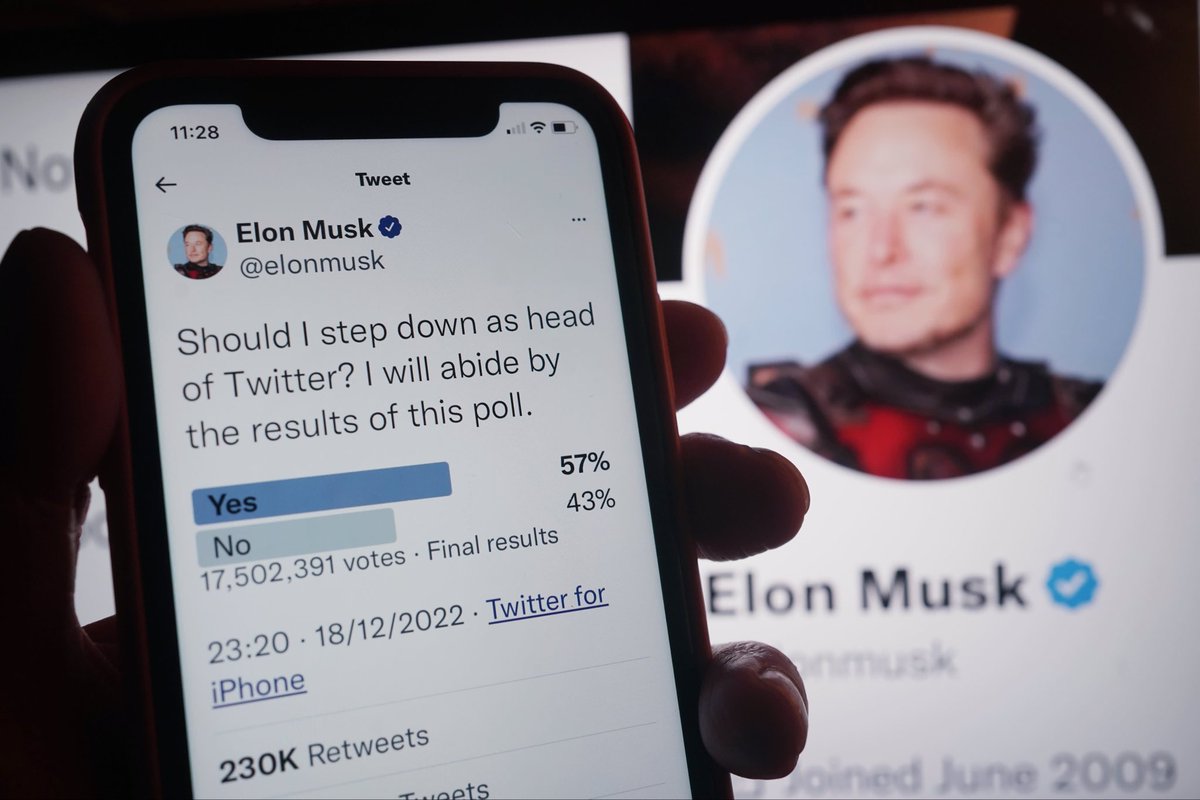
Per @RachelTobac: 75% of Twitter 2FA users are using SMS-based authentication. In theory those users could switch to authenticator apps (or pay 😂) but they probably won’t.
People keep saying things like “but authenticator apps will still be free and those won’t require you to pay, plus they’re more secure.” That’s true! But also completely misunderstands what’s about to happen.
What sets SMS 2FA apart is that it’s almost “free” from a user-effort perspective. If you own a phone, the feature is already built-in and enabled. Setup is nearly effortless. Backup is taken care of. Unfortunately none of the same things are true for HOTP/authenticator apps.
The cognitive overhead of installing an authenticator app (and then worrying about what happens when you lose your phone) is absolutely ridiculous. The overall experience is just stunningly bad, given that it’s one of the best defenses we have.
Free one-time code authenticators *should* be built into every phone. They *should* be enabled on the default keyboard. They *should* be securely backed up to an end-to-end encrypted account. If Google/Apple did this, adoption would be high.
Instead we have this ecosystem of crappy apps that you have to install manually. Some have weird cloud backup built in, of unknown security level. Some require you to back up manually with a QR code (ugh, Google Authenticator). It’s such garbage. 

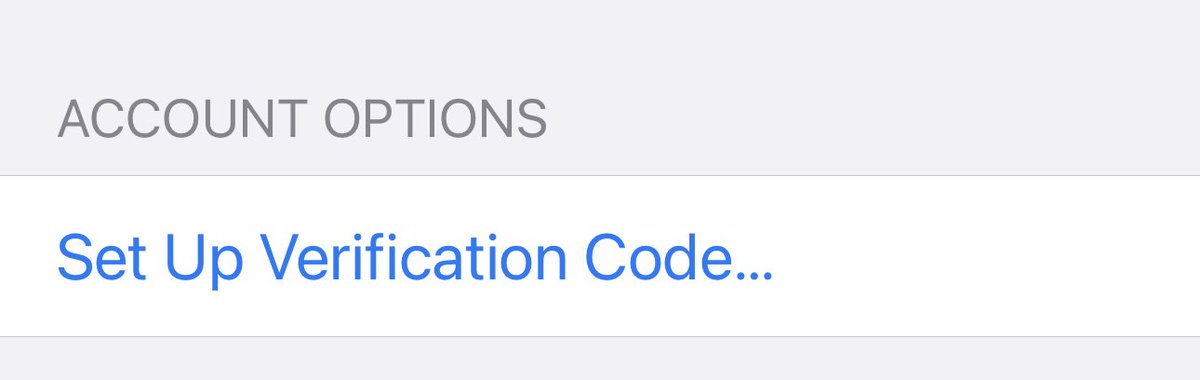
I learned recently that iOS has authenticator capability built in, and it will even back up to iCloud Keychain (using end-to-end encryption)!
All you have to do is navigate to a hidden submenu buried under “Settings”. It really sucks. But at least it’s better than Android.
All you have to do is navigate to a hidden submenu buried under “Settings”. It really sucks. But at least it’s better than Android.
I know companies like Apple and Google have all these great ideas like “let’s eliminate passwords using cool new ideas, eg ‘passkeys’”. Maybe that’ll work out. I hope so! I hate that these companies are slow-rolling security *today* so things can be “perfect” tomorrow.
Anyway. I’m certainly no expert on usable security. My only superpower is that *I am extremely lazy.*
SMS 2FA sucks sucks sucks, but I empathize with the Twitter users who chose it — and I understand why the alternative will be “no 2FA.” Too bad for Twitter.
SMS 2FA sucks sucks sucks, but I empathize with the Twitter users who chose it — and I understand why the alternative will be “no 2FA.” Too bad for Twitter.
• • •
Missing some Tweet in this thread? You can try to
force a refresh




