🚨 Update your @apple products immediately!
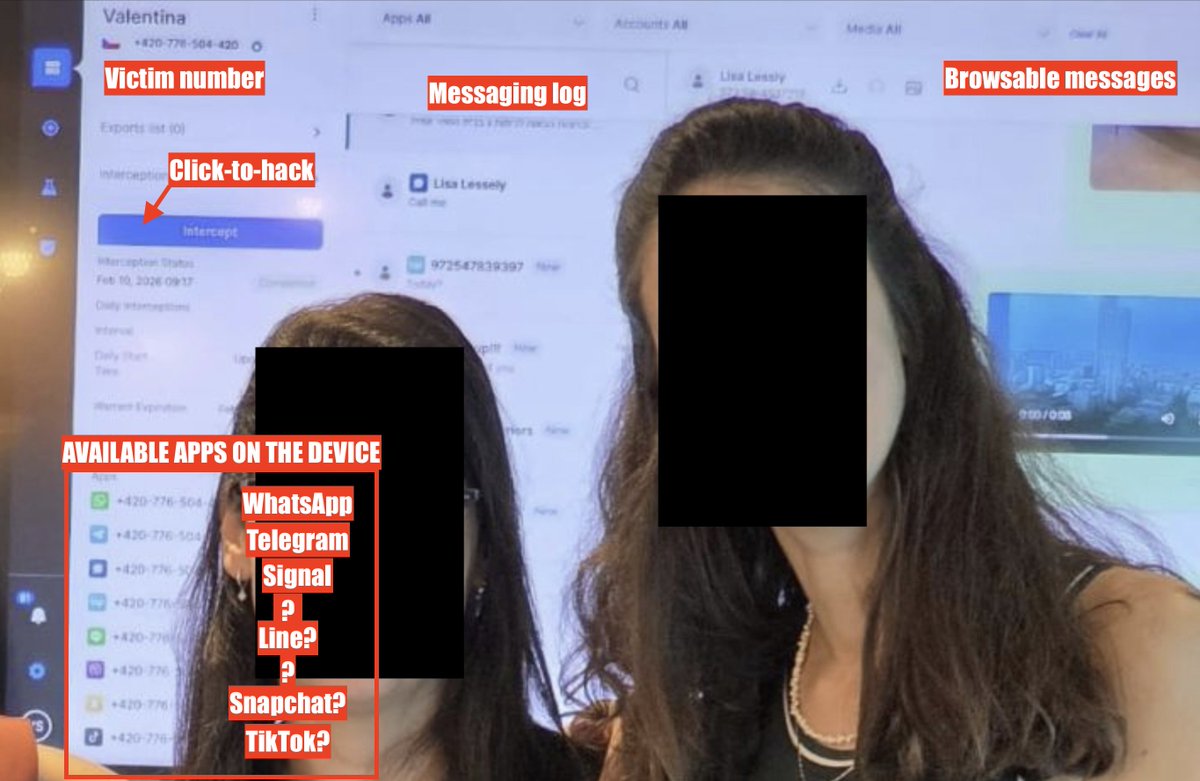
Last week we @citizenlab discovered a new #Pegasus zero-click exploit chain.
(No clicking required to infect latest iOS!)
Found while checking civil society.
Disclosed to Apple which rushed a patch 1/
citizenlab.ca/2023/09/blastp…

Last week we @citizenlab discovered a new #Pegasus zero-click exploit chain.
(No clicking required to infect latest iOS!)
Found while checking civil society.
Disclosed to Apple which rushed a patch 1/
citizenlab.ca/2023/09/blastp…

2/ We found the #BLASTPASS exploit chain thanks to an unnamed victim.
Once more, civil society, is serving as the cybersecurity early warning system for... billions of devices around the world.
Including you, if you're reading this on your iPhone. Or Mac.
Once more, civil society, is serving as the cybersecurity early warning system for... billions of devices around the world.
Including you, if you're reading this on your iPhone. Or Mac.

3/Update your #iPhone right away.
And then, if you are at risk because of who you are or what you do, enable #Lockdown mode.
As my colleague @billmarczak says "it's the one weird trick NSO hates"
And then, if you are at risk because of who you are or what you do, enable #Lockdown mode.
As my colleague @billmarczak says "it's the one weird trick NSO hates"

4/ UPDATE on #BLASTDOOR exploit:
We believe, and @Apple's Security Engineering and Architecture team has confirmed to us, that Lockdown Mode blocks this particular attack.
(Obviously you should also make sure to update!)
We believe, and @Apple's Security Engineering and Architecture team has confirmed to us, that Lockdown Mode blocks this particular attack.
(Obviously you should also make sure to update!)

5/ What's Lockdown Mode?
✅available to anyone with a recent iPhone
✅Enabled in seconds.
✅Locks down routes hackers often use to infect phones.
Result:
✅phone in your pocket is much more expensive to hack.
You should probably use it.
support.apple.com/en-ca/HT212650

✅available to anyone with a recent iPhone
✅Enabled in seconds.
✅Locks down routes hackers often use to infect phones.
Result:
✅phone in your pocket is much more expensive to hack.
You should probably use it.
support.apple.com/en-ca/HT212650

• • •
Missing some Tweet in this thread? You can try to
force a refresh