🚨UPDATE your @Apple products now!
We @citizenlab w/TAG's @maddiestone caught #predator spyware attacks against a prominent pro-democracy Egyptian politician after he announced presidential ambitions.
Apple rushed a patch.
It gets crazier 1/
citizenlab.ca/2023/09/predat…

We @citizenlab w/TAG's @maddiestone caught #predator spyware attacks against a prominent pro-democracy Egyptian politician after he announced presidential ambitions.
Apple rushed a patch.
It gets crazier 1/
citizenlab.ca/2023/09/predat…

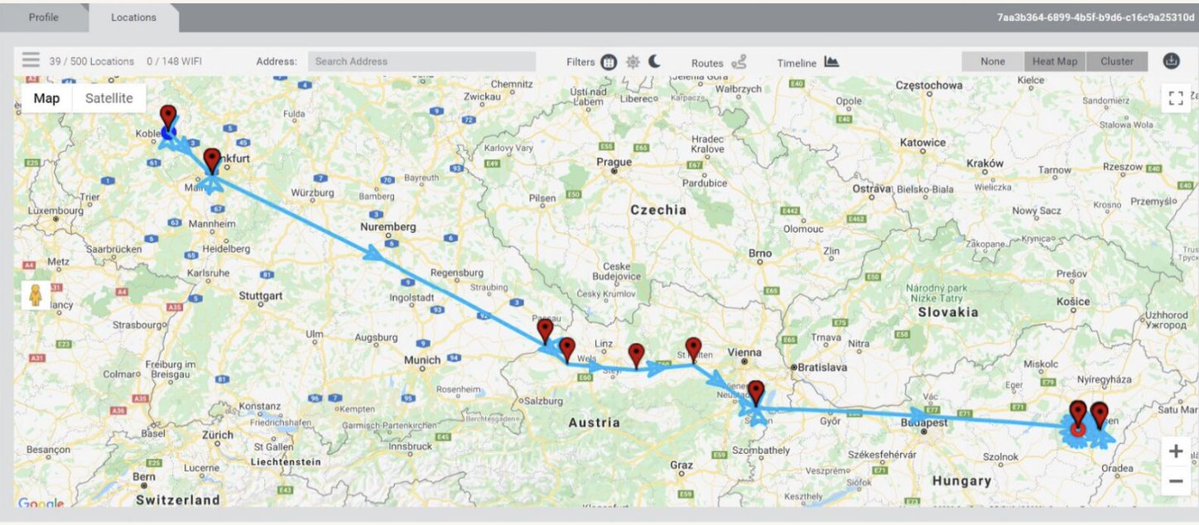
2/ Ahmed Eltantawy got in touch with us @citizenlab, worried his devices were targeted in #Egypt.
He was right. His iPhone on @VodafoneEgypt was targeted for network injection.
As he browsed the net, the attackers were trying to slip a #Predator infection onto his device.



He was right. His iPhone on @VodafoneEgypt was targeted for network injection.
As he browsed the net, the attackers were trying to slip a #Predator infection onto his device.



3/ It gets worse.
We attribute the spyware injection system to a @Sandvine Packet Logic product w/high confidence.
Sandvine has been accused in past of facilitating human rights abuses in the past.
Owned by NSO Group's former owner Francisco Partners.




We attribute the spyware injection system to a @Sandvine Packet Logic product w/high confidence.
Sandvine has been accused in past of facilitating human rights abuses in the past.
Owned by NSO Group's former owner Francisco Partners.
https://twitter.com/accessnow/status/1301950701178941446




4/ This kind of exploit delivery through injection DOES NOT require a target to click as our collaborator, the brilliant @maddiestone, points out in her post.
It's a seriously dangerous kind of attack & hard to protect against.
blog.google/threat-analysi…

It's a seriously dangerous kind of attack & hard to protect against.
blog.google/threat-analysi…

@maddiestone 5/ Apple moved quickly to fix the zero-day exploits @maddiestone & @billmarczak discovered.
We encourage everyone to immeidately update their apple products.
There is a piece of good security news buried in all this...
We encourage everyone to immeidately update their apple products.
There is a piece of good security news buried in all this...

@maddiestone @billmarczak 6/ We believe & Apple's Security Engineering & Architecture Team confirms, Lockdown Mode would have blocked this attack!
We *strongly* encourage all Apple users that may be at risk because of who they are or what they do to enable Lockdown Mode!
support.apple.com/en-us/HT212650

We *strongly* encourage all Apple users that may be at risk because of who they are or what they do to enable Lockdown Mode!
support.apple.com/en-us/HT212650

@maddiestone @billmarczak 7/ Ahmed ElTantawy wasn't just targeted with network injection!
He was also targeted with #Predator spyware links in decoy messages sent as texts & over @WhatsApp.
One of the attacks masqueraded as communications from the International Federation for Human Rights @fidh_en
He was also targeted with #Predator spyware links in decoy messages sent as texts & over @WhatsApp.
One of the attacks masqueraded as communications from the International Federation for Human Rights @fidh_en

@maddiestone @billmarczak @WhatsApp @fidh_en 8/ This summer the 🇺🇸US hit developer & distributor of #Predator spyware (Cytrox & Intellexa) with blacklisting.
This latest abuse revelation affirms the determination that the spyware continues to fuel human rights abuses.
By @ddimolfetta & @Post_AG
washingtonpost.com/national-secur…

This latest abuse revelation affirms the determination that the spyware continues to fuel human rights abuses.
By @ddimolfetta & @Post_AG
washingtonpost.com/national-secur…

9/ Pulling back the lens from the tech side of this #Predator attack:
Mercenary spyware is autocrat fuel.
When you hack a pro-democracy presidential hopeful in an autocracy... you are doing dictatorship.
And spyware companies know exactly who they are selling to.
Mercenary spyware is autocrat fuel.
When you hack a pro-democracy presidential hopeful in an autocracy... you are doing dictatorship.
And spyware companies know exactly who they are selling to.

10/ Without brave victims like Ahmed Tantawy getting checked & coming forwards, these recent exploits would not have been found.
Billions of apple devices would still be vulnerable.
Including yours.
Billions of apple devices would still be vulnerable.
Including yours.

• • •
Missing some Tweet in this thread? You can try to
force a refresh