First up - are you ready to become a full fledged cyber professional?
Maybe even a Security Analyst or Security Operations Center Analyst?
Good - I have just the thing for you - sign up now for the bootcamp waitlist at:
maikroservice.com/waitlist

Maybe even a Security Analyst or Security Operations Center Analyst?
Good - I have just the thing for you - sign up now for the bootcamp waitlist at:
maikroservice.com/waitlist

*nix systems store logs in a variety of locations but most of them are aggregated in one central folder:
/var/log
/var/log
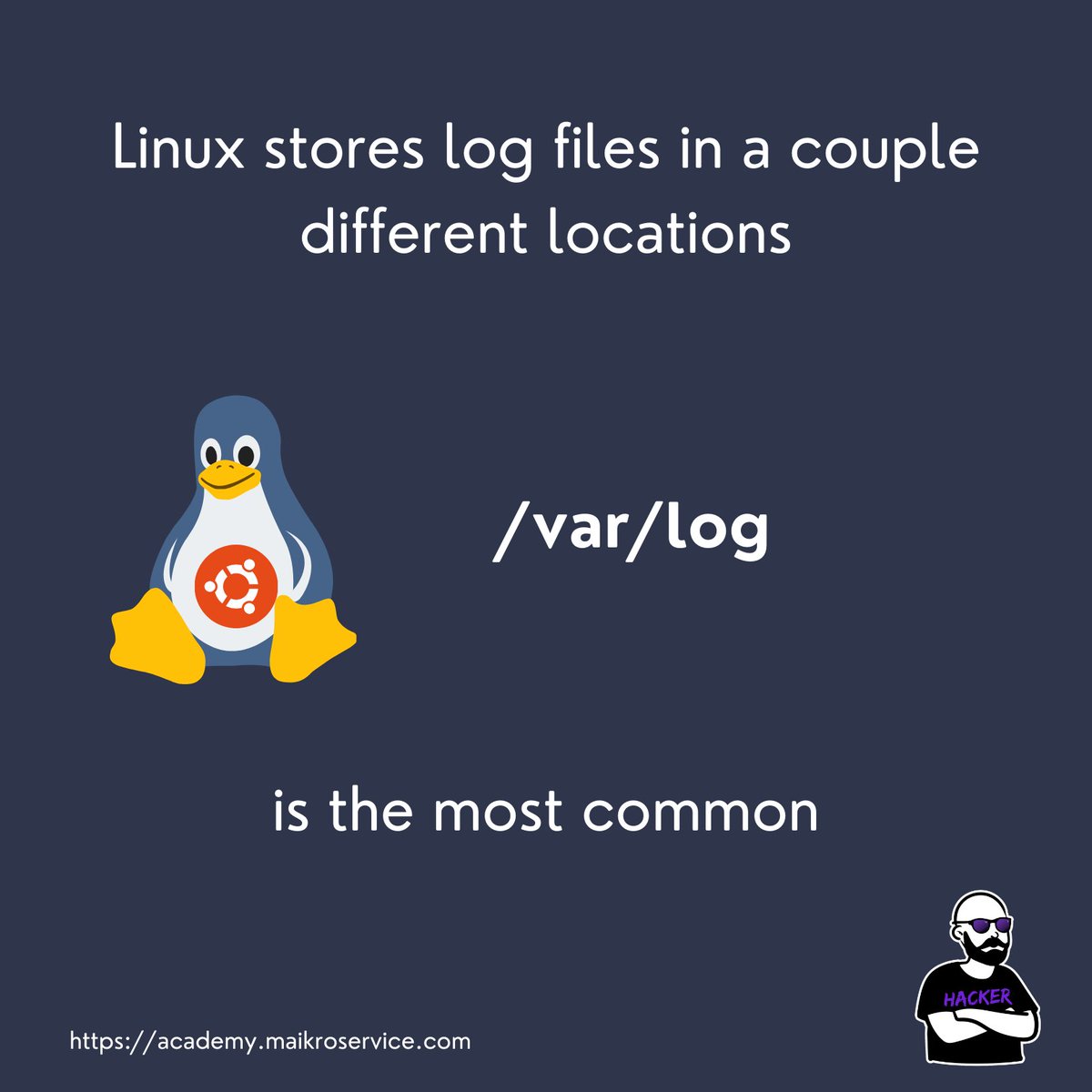
GREAT! but umm… is this universal?
Do all unix systems store the same log files?
Is the content always the same across distributions?
NO.
Do all unix systems store the same log files?
Is the content always the same across distributions?
NO.

WHAT THE FUDGE?!
Exactly - Apparently ubuntu 23.04 added a new file called apport.log (it holds information about program crashes) which ubuntu 22.04 does not have
Exactly - Apparently ubuntu 23.04 added a new file called apport.log (it holds information about program crashes) which ubuntu 22.04 does not have
Huh, interesting.
Well but it also makes sense - software evolves and changes - just like Operating Systems ;) (they are software)
Well but it also makes sense - software evolves and changes - just like Operating Systems ;) (they are software)
Ok cool, but which files do I need to know when I want to become a Security/SOC Analyst?
There are at least 5 you should have heard of (probably more)
There are at least 5 you should have heard of (probably more)

Wanna look at them?
OK HERE WE GO!
OK HERE WE GO!
First candidate is auth.log, located in /var/log/auth.log and it is one of the important logs that every SOC Analyst needs to know 

auth.log holds
logins
user changes
group changes
system reboot timestamps
sudo command history
… more
logins
user changes
group changes
system reboot timestamps
sudo command history
… more

Next up in our list is syslog
The ultimate log, cut directly from Yggdrasil and forged in the hell fire protected by Kerberos (or something like that 🤣) - the holy grail of logs
The ultimate log, cut directly from Yggdrasil and forged in the hell fire protected by Kerberos (or something like that 🤣) - the holy grail of logs

The systemlog or syslog is a combination of multiple different log information - e.g. authentication events, kernel events and something called “locales” 

a local is basically a configurable channel that you can fill with almost any log of your choice
Have a webserver that you want to monitor closely? Put it on a local
Need to know when your Database throws up? Put it on a local
You get the idea 💡
Have a webserver that you want to monitor closely? Put it on a local
Need to know when your Database throws up? Put it on a local
You get the idea 💡
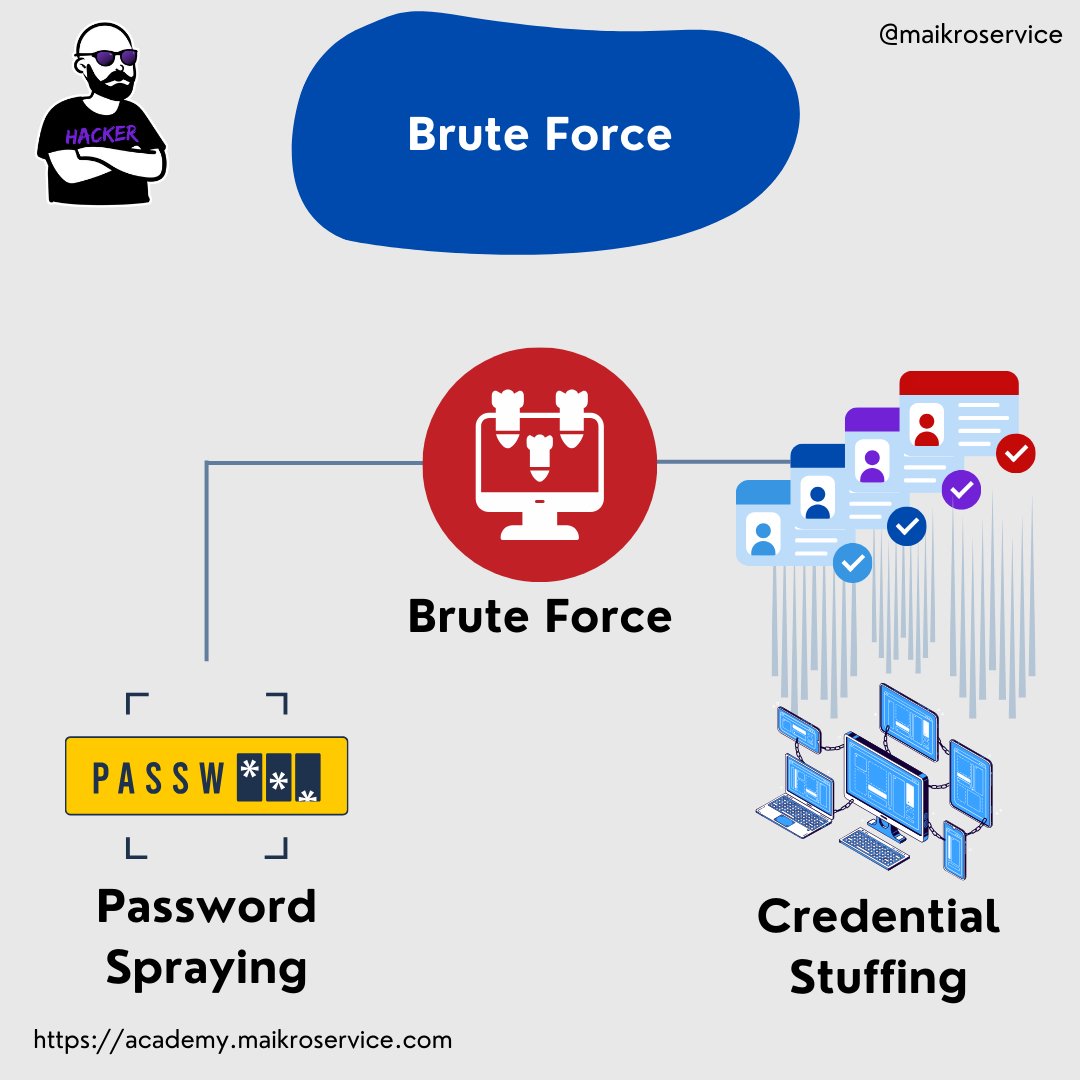
Wonderful, but I want to know where I can look for brute-force attacks.
Smart!
You could find those in two specialized logs - wtmp and btmp
Smart!
You could find those in two specialized logs - wtmp and btmp

These two are a little special though, they are binary logs.
Binary what?
They hold 0s and 1s ? almost. They are in a format that is not plain text but needs a special command to be readable
PFFF I dont believe you.
Binary what?
They hold 0s and 1s ? almost. They are in a format that is not plain text but needs a special command to be readable
PFFF I dont believe you.
You dont?
Well.. that makes me sad. but luckily I can prove it!
try opening wtmp with a text editor:
Well.. that makes me sad. but luckily I can prove it!
try opening wtmp with a text editor:

MAKE IT STOP - ahh ok much better.
How would I open those to be readable in dark mode though?!
use the last and lastb commands:
How would I open those to be readable in dark mode though?!
use the last and lastb commands:

last reads the wtmp file which holds all the current logon sessions (who is using the computer)
while lastb needs sudo rights to execute and it holds failed logon attempts
check it out:
sudo lastb
oh. Its empty.
while lastb needs sudo rights to execute and it holds failed logon attempts
check it out:
sudo lastb
oh. Its empty.

ok ok ok - we can easily generate some failed logons - either use hydra for brute force or just type your password wrong at least 2x
Just like I do every time… … 😅🫠
Just like I do every time… … 😅🫠

Can we also see when users logged in the last time?
SURE! That is where lastlog comes in - its a command that allows you to see who logged into the computer at which time.
SURE! That is where lastlog comes in - its a command that allows you to see who logged into the computer at which time.

if e.g. a hacker would login as root because they escalated their privileges and then uploaded a ssh key into the root .ssh folder - you can see that
and start the investigation 🔬👀 🕵️
and start the investigation 🔬👀 🕵️

The last one for today is called journalctl - it is a good starting point to check if services/software had errors during their installation / runtime 

typically you would use
journalctl -xe
to see the end of the file (-e), the most recent part, and more metadata (-x)
journalctl -xe
to see the end of the file (-e), the most recent part, and more metadata (-x)

Just like MAGIC! 🪄✨
I hope you learned something today - if you did please follow me @maikroservice for more content like this
I hope you learned something today - if you did please follow me @maikroservice for more content like this

@threadreaderapp unroll
• • •
Missing some Tweet in this thread? You can try to
force a refresh