Today US DoJ announced seizure of two domains and the search of 968 accounts on X used in a "Russian-government backed campaign" to spread disinformation.
Affidavit includes all of the accounts requested from X 👇



Affidavit includes all of the accounts requested from X 👇



The DoJ announcement said the campaign used elements of AI to create fictitious social media profiles purporting to belong to individuals in the United States, which the operators then used to promote messages in support of Russian government objectives. justice.gov/opa/pr/justice…
The affidavit for the accounts on X shows that all of the accounts were registered to email addresses that were either using the domain 'otanmail' or 'mlrtr' justice.gov/d9/2024-07/aff…


According to the affidavit, the development of the 'bot farm' was organised by the leader of the directorate of digital journalism within the Russian Government backed news outlet Russia Today (RT).




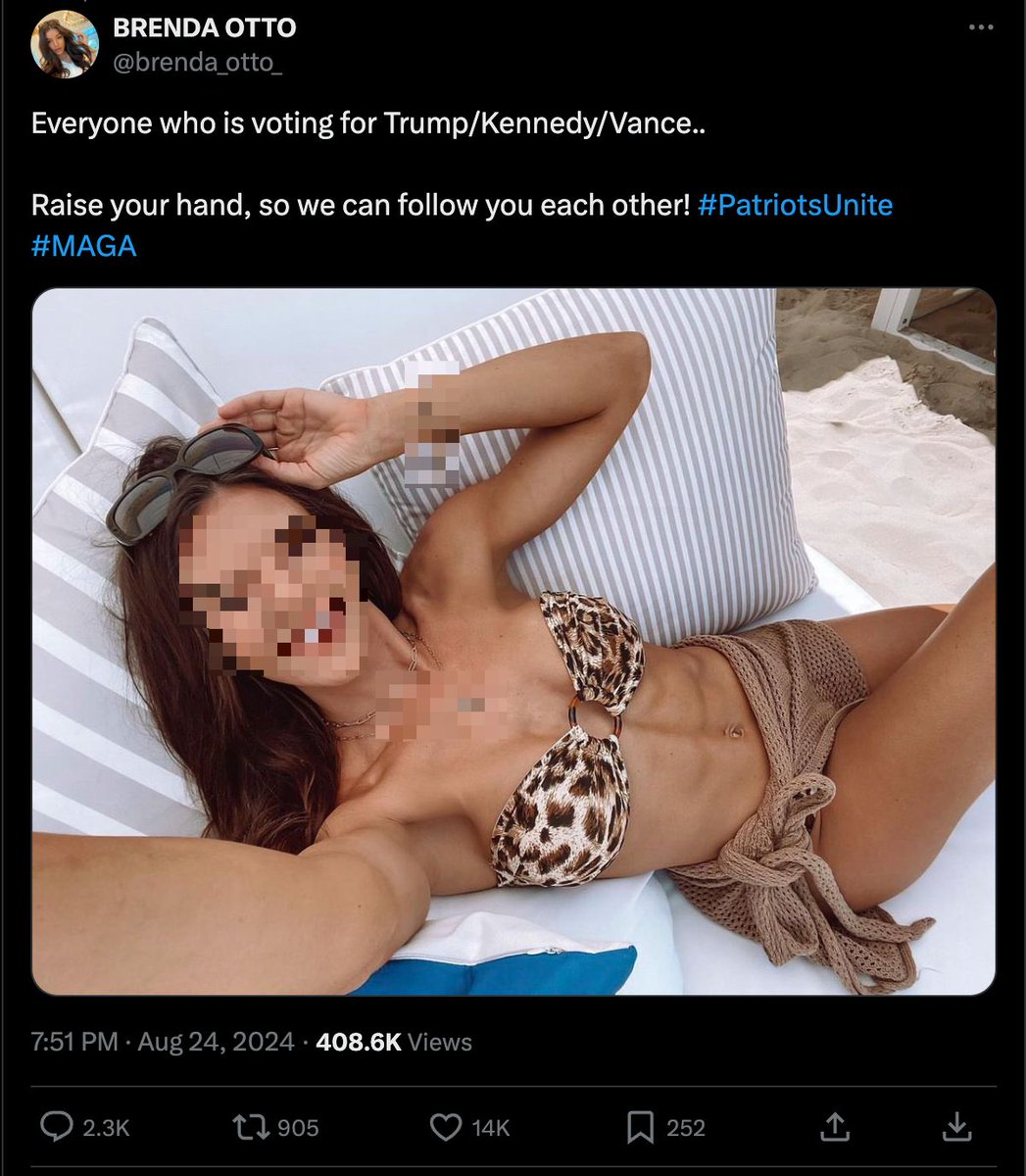
One of the accounts mentioned in the affidavit didn't use the two domains seized by DoJ, but rather an address provided by a disposable email service. The account @tblock1999xe is still available. Note the GAN-generated profile image.


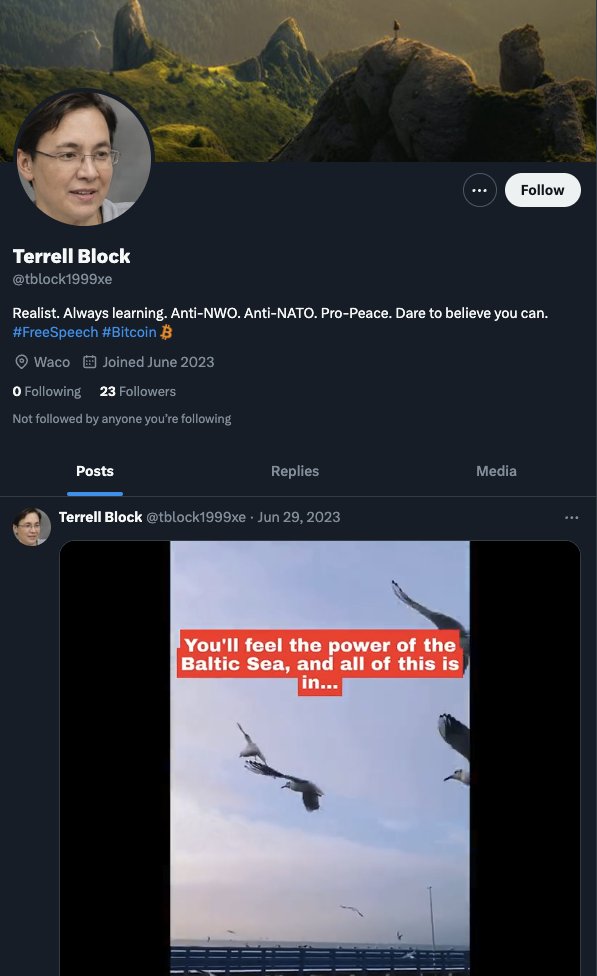

This account, included in the RT network, appeared to post videos of Putin as replies to posts on X, specifically posts about Ukraine, Palestine or US politics. Not very great influence content, barely any traction, and pretty much just there to promote Putin.






In a joint release today, the FBI, Dutch AIVD and Canada's CCCS also published technical details of the Russian network architecture. It used Meliorator to generate accounts en masse through a Brigadir UI, then Taras to control the personas on X. ic3.gov/Media/News/202…




The developer of the architecture behind the network putting out RT content on X inserted code to allow for the server to bypass X verification methods, the ones put in place to prevent bot capabilities.



Relevant to share this interview from Head of RT Margarita Simonyan, shared by @JuliaDavisNews, via @Prune602.
Simonyan talks about how they create 'many sources of information not tied to them' and 'some mornings you wake up and 600 channels are gone'.

Simonyan talks about how they create 'many sources of information not tied to them' and 'some mornings you wake up and 600 channels are gone'.

• • •
Missing some Tweet in this thread? You can try to
force a refresh