𝗦𝗼𝗳𝘁-𝗞𝗶𝗹𝗹 𝗧𝗲𝗰𝗵𝗻𝗶𝗾𝘂𝗲𝘀 𝐚𝐠𝐚𝐢𝐧𝐬𝐭 𝗨𝗔𝗩𝘀🧵
Soft-kill countermeasures involve neutralizing UAVs without physical destruction, minimizing collateral damage and reducing escalation risks.
These methods utilize advanced technologies such as electronic warfare, jamming, spoofing, and directed energy weapons to disrupt drone operations and neutralize them effectively.


Soft-kill countermeasures involve neutralizing UAVs without physical destruction, minimizing collateral damage and reducing escalation risks.
These methods utilize advanced technologies such as electronic warfare, jamming, spoofing, and directed energy weapons to disrupt drone operations and neutralize them effectively.



Detection and tracking of UAVs
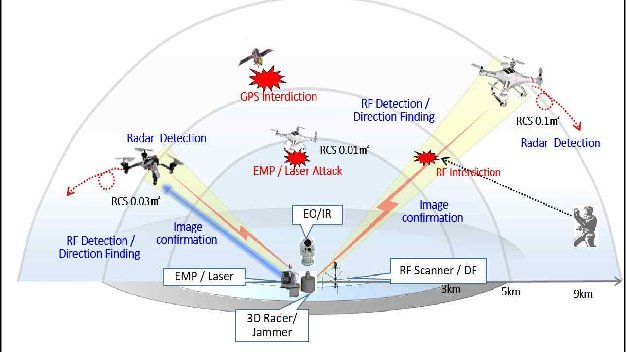
🔸Effective detection and tracking are essential before implementing any countermeasures. Multiple technologies are employed to identify UAVs in real-time and assess their threat level.
Radar Systems:
🔸Specialized ground-based or airborne radars monitor the airspace and detect UAVs, even those with minimal radar signatures, in complex environments.


🔸Effective detection and tracking are essential before implementing any countermeasures. Multiple technologies are employed to identify UAVs in real-time and assess their threat level.
Radar Systems:
🔸Specialized ground-based or airborne radars monitor the airspace and detect UAVs, even those with minimal radar signatures, in complex environments.



Electro-Optical (EO) and Infrared (IR) Sensors: 🔸These sensors provide real-time tracking of UAVs by detecting their heat signatures or visual characteristics aiding in the assessment of their potential threat level.
RF Spectrum sensors:
🔸RF sensors scan the frequency spectrum to identify GPS & communication links between the UAV and its operator or Control Station.
RF Spectrum sensors:
🔸RF sensors scan the frequency spectrum to identify GPS & communication links between the UAV and its operator or Control Station.

Once data is collected from radar, RF sensors, and EO/IR systems, a decision is made on whether to neutralize the drone.
This decision is based on a comprehensive assessment of the UAV’s behavior, its threat level and the potential consequences of engagement.

This decision is based on a comprehensive assessment of the UAV’s behavior, its threat level and the potential consequences of engagement.


Jamming Communication Links
🔸Jamming is one of the most widely used soft-kill methods. By disrupting the UAV’s communication link with its operator, it forces the UAV to enter a fail-safe mode:
RF Jamming:
🔸A high-power RF jammer tuned to the specific frequency bands, disrupt frequencies used by the drone including satellite communications and control links, causing the drone to lose its connection.


🔸Jamming is one of the most widely used soft-kill methods. By disrupting the UAV’s communication link with its operator, it forces the UAV to enter a fail-safe mode:
RF Jamming:
🔸A high-power RF jammer tuned to the specific frequency bands, disrupt frequencies used by the drone including satellite communications and control links, causing the drone to lose its connection.


If successful, the drone loses communication with its ground control or satellite and enters a fail-safe mode such as:
Hover Mode:
🔸The drone stays in position, making it an easy target for capture or destruction.
RTB (Return to Base):
🔸The drone automatically returns to its launch point.
Hover Mode:
🔸The drone stays in position, making it an easy target for capture or destruction.
RTB (Return to Base):
🔸The drone automatically returns to its launch point.
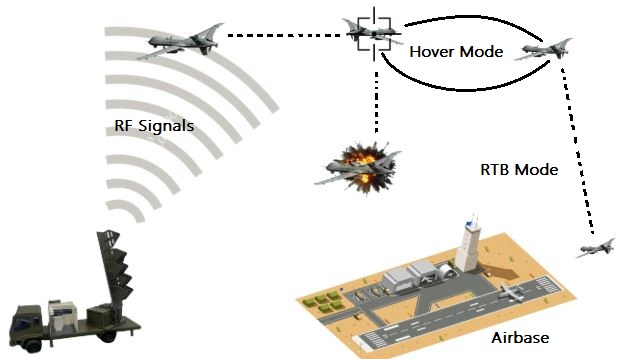
GPS Jamming:
🔸GPS jammers disrupt a UAV's navigation system by emitting radio frequency signals on the same frequencies as GPS satellites. These signals interfere with or block the UAV's navigation, overwhelming its receiver with noise or false data.
This often leads to a 'lost link' scenario, causing the UAV to either enter return-to-home mode or hover in place.
🔸GPS jammers disrupt a UAV's navigation system by emitting radio frequency signals on the same frequencies as GPS satellites. These signals interfere with or block the UAV's navigation, overwhelming its receiver with noise or false data.
This often leads to a 'lost link' scenario, causing the UAV to either enter return-to-home mode or hover in place.
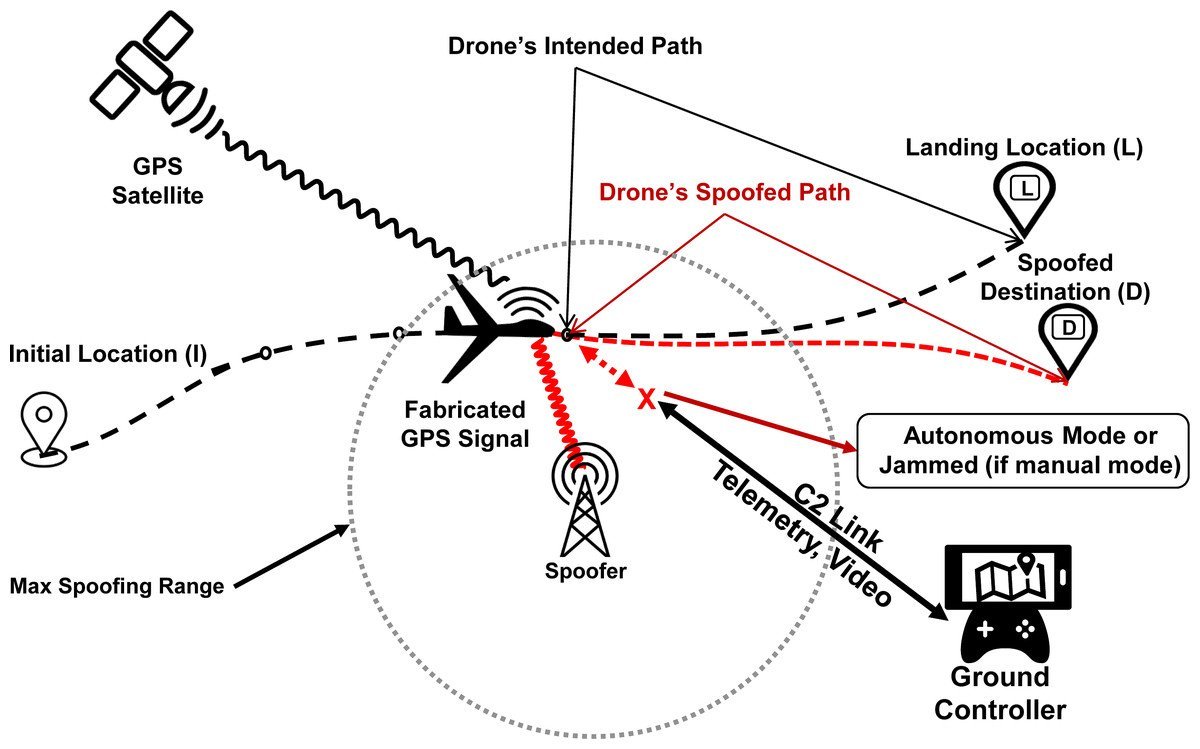
GPS Spoofing:
🔸GPS spoofing involves transmitting false GPS signals stronger than those from satellites to manipulate the drone’s navigation system redirecting the UAV to a specific location, where it can either safely land or made to crash by providing invalid coordinates.
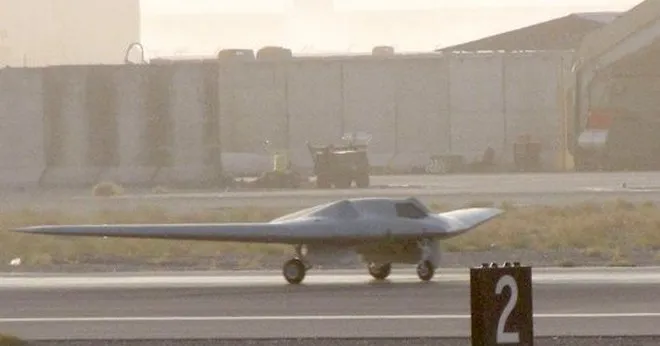
On December 5, 2011, Iran's cyberwarfare unit executed a GPS spoofing attack on an American RQ-170 Sentinel drone. By jamming its communication signals and feeding it false GPS coordinates, they manipulated the drone's navigation system, successfully forcing it to land in #Iran.


🔸GPS spoofing involves transmitting false GPS signals stronger than those from satellites to manipulate the drone’s navigation system redirecting the UAV to a specific location, where it can either safely land or made to crash by providing invalid coordinates.
On December 5, 2011, Iran's cyberwarfare unit executed a GPS spoofing attack on an American RQ-170 Sentinel drone. By jamming its communication signals and feeding it false GPS coordinates, they manipulated the drone's navigation system, successfully forcing it to land in #Iran.

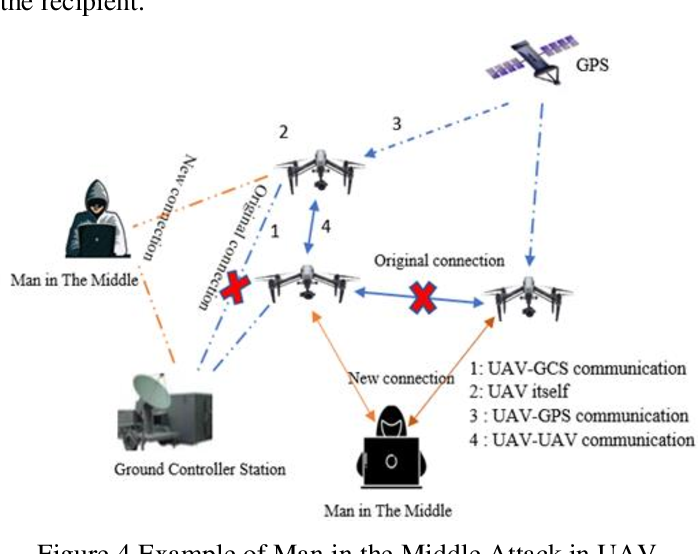
Cyber Intrusion:
🔸Advanced drones use encrypted communication, but cyber intrusion can exploit software vulnerabilities by breaching the UAV’s software and communication protocols. this approach requires highly advanced Electronic Warfare (EW) capabilities.
Exploiting Vulnerabilities:
🔸By targeting the drone’s firmware, unauthorized control can be gained to issue commands such as landing or shutting down.
Cyber tools can also provide real-time control of the drone, taking it over and landing it securely if successful in breaching software protocols.

🔸Advanced drones use encrypted communication, but cyber intrusion can exploit software vulnerabilities by breaching the UAV’s software and communication protocols. this approach requires highly advanced Electronic Warfare (EW) capabilities.
Exploiting Vulnerabilities:
🔸By targeting the drone’s firmware, unauthorized control can be gained to issue commands such as landing or shutting down.
Cyber tools can also provide real-time control of the drone, taking it over and landing it securely if successful in breaching software protocols.

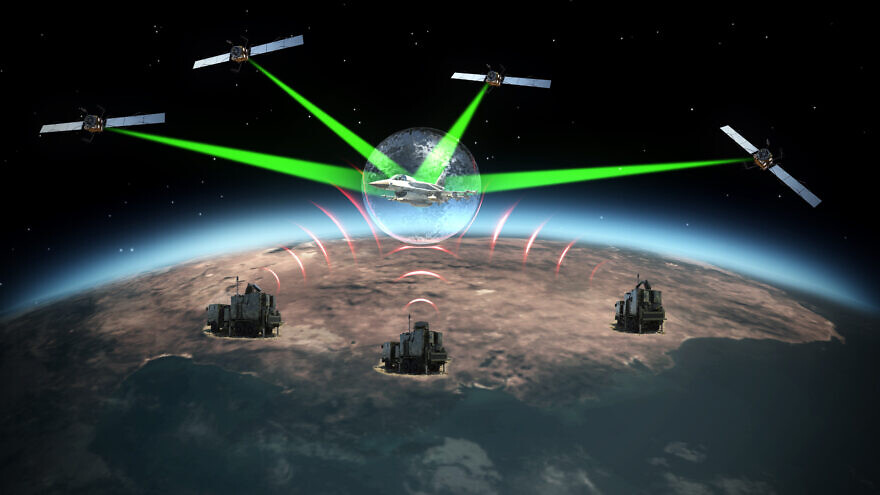
Directed Energy Weapons (DEWs)
🔸Directed Energy Weapons (DEWs), such as high-powered microwaves and lasers use to damage, destroy or disable ecteronic, weapons, or other systems using electromagnetic energy.
High-Power Microwave (HPM) Systems:
🔸These systems use electromagnetic pulses to interfere with or destroy the UAV's electronic circuits, rendering it inoperable..
🔸Directed Energy Weapons (DEWs), such as high-powered microwaves and lasers use to damage, destroy or disable ecteronic, weapons, or other systems using electromagnetic energy.
High-Power Microwave (HPM) Systems:
🔸These systems use electromagnetic pulses to interfere with or destroy the UAV's electronic circuits, rendering it inoperable..

High Energy Laser Systems:
🔸HEL systems generate a highly concentrated beam of light of specific wavelengths using advanced optics and energy sources to disable the drone's navigation, damage its rotors or engines, and burn through its structure, causing it to crash.
Lasers dazzlers:
🔸They are used to temporarily or permanently blind a UAV's sensors or cameras, neutralizing its operational capabilities particularly.
These methods are particularly effective at short ranges due to several factors affecting the laser's performance, including atmospheric conditions beam divergence etc.


🔸HEL systems generate a highly concentrated beam of light of specific wavelengths using advanced optics and energy sources to disable the drone's navigation, damage its rotors or engines, and burn through its structure, causing it to crash.
Lasers dazzlers:
🔸They are used to temporarily or permanently blind a UAV's sensors or cameras, neutralizing its operational capabilities particularly.
These methods are particularly effective at short ranges due to several factors affecting the laser's performance, including atmospheric conditions beam divergence etc.



• • •
Missing some Tweet in this thread? You can try to
force a refresh







