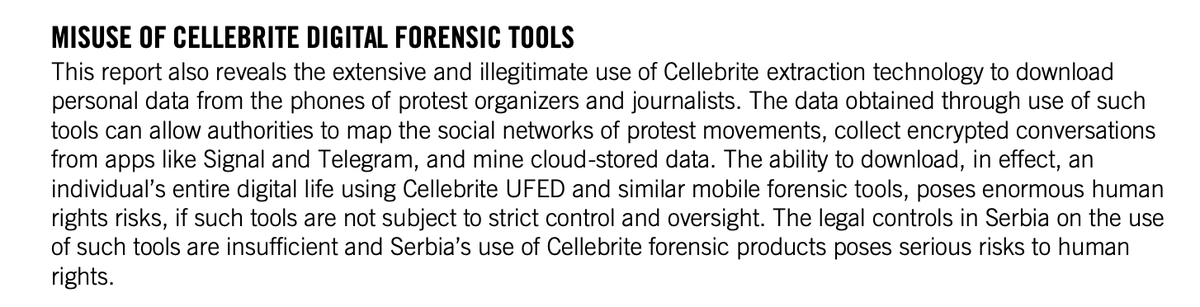
🚨 UPDATE YOUR DEVICES 🚨: Amnesty International uncovers sophisticated zero-day exploit affecting billions of Android devices.
Cellebrite's Linux USB exploit was used to unlock the phone of a Serbian youth activist, targeted in December 2024 **after** previous reports abuses
Cellebrite's Linux USB exploit was used to unlock the phone of a Serbian youth activist, targeted in December 2024 **after** previous reports abuses

Our team at the Security Lab saw this Linux kernel USB exploit chain used against multiple people since mid-2024.
We shared traces of exploit with Google's Threat Analysis Group allowing for the identification of at least three zero-day vulnerabilities
securitylab.amnesty.org/latest/2025/02…
We shared traces of exploit with Google's Threat Analysis Group allowing for the identification of at least three zero-day vulnerabilities
securitylab.amnesty.org/latest/2025/02…
The USB exploit chain targets mainline Linux kernel drivers, potentially affecting devices across all Android vendors.
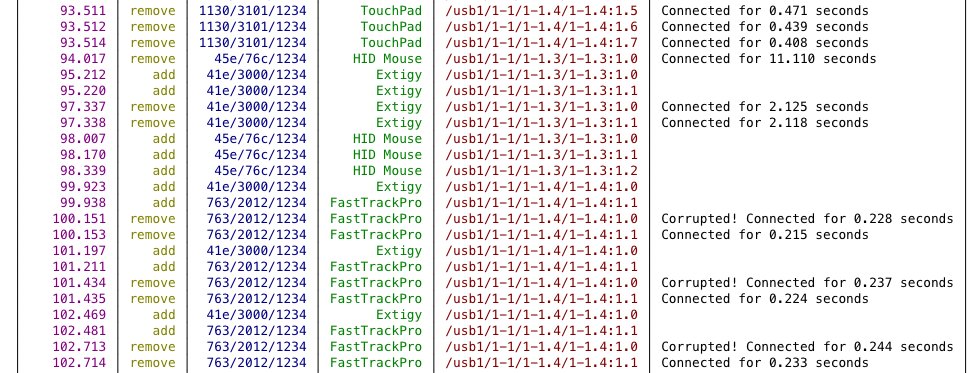
At least five different USB device type types were used as part of the exploitation process. More exploit details are shared in our blog post
At least five different USB device type types were used as part of the exploitation process. More exploit details are shared in our blog post
Cases like this show how real-world attackers are exploiting the latest mobile devices.
Android vendors should urgently implement security mitigations to limit the large attack exposed to malicious USB devices connected to a locked Android phone.
grapheneos.org/features#usb-c…
Android vendors should urgently implement security mitigations to limit the large attack exposed to malicious USB devices connected to a locked Android phone.
grapheneos.org/features#usb-c…
This work would not be possible without the trust of the targeted student activist, and close collaboration with Google TAG m partners across Serbian civil society and many @Amnesty colleagues
@benoitsevens @BIRNSrbija @ShareConference @Jelena_Sesar @ruairin
@benoitsevens @BIRNSrbija @ShareConference @Jelena_Sesar @ruairin
Earlier this week @Cellebrite announced that they were suspending Serbian customers following these repeated reports of misuse. This action is an important first-step to limit ongoing harm from their products
https://x.com/AmnestyTech/status/1894756849271931332
Our partners at @BIRNSrbija have an excellent piece today featuring the student activist targeted in this case. See the human impact that these invasive tools can have alongside other oppressive tactics and intimidation
Highly recommend reading
Highly recommend reading
https://x.com/BIRNSrbija/status/1895387790181077491
• • •
Missing some Tweet in this thread? You can try to
force a refresh