@EdMartinDOJ @USAO_SDFL @TulsiGabbard @NCTCKent
https://twitter.com/Burevestnik2025/status/1993722118488596694
The backdoor enables an operator to access to perform system updates and testing via the Internet without detection. However, it can also be used to conduct illicit activities such as shifting votes, deleting votes, or adding votes in real-time...
...in real-time (Source: DVS Democracy Suite EMS Manual, version 5.11-CO::7, P.43). These events can take place through the Internet and without leaving a trace.
para. 7, The results showed that Scytl maintained its SOE Software servers in a Barcelona data center for disaster recovery and backup purposes. In 2020, the SOE Software data center was moved to Frankfurt Germany where I believe 2020 election data was transferred.
para. 8, pg.3, DVS reportedly had a strategic relationship with Venezuela’s Bitza Corporation, which was 28% owned by the former President Chavez. Intelligence reports indicate that the DVS/Bitza software was co-developed in Venezuela
para.8, pg.9, in Venezuela to alter vote counts to ensure President Chavez (and later, Pres. Maduro) were guaranteed to win an election. The combined DVS/Bitza software was used in numerous countries such as Bolivia and Philippines to forge election results to favor a candidate.
Subsequently, DVS and its international partners, including Diebold/ES&S (later acquired by DVS), Scytl, SOE Software/eClarity and Smartmatic to establish a global monopoly.
Similarly, Smartmatic is comprised of: 1) Smartmatic International Corporation, a Barbados corporation; 2) Smartmatic USA Corporation, a Delaware corporation; 3) Smartmatic International Holding B.V, a Netherlands corporation; and 4) Smartmatic TIM Corporation, a Philippines corp
Based on my counterintelligence experience in USIC, I conclude that corporate structures were partially designed to obfuscate their complex relationships, especially with Venezuela, China and Cuba; and impede discovery by investigators. para.9, pg. 3
Case 2:20-cv-13134-LVP-RSW ECF No. 1-19, PageID.825 Filed 11/25/20 Page 4 of 9 ...the company’s ImageCast Precinct optical scanner system was totally hacked in August 2019. This occurred during the largest and most notable hacker convention, called DEFCON...
...The DVS ImageCast Precinct is an integrated hybrid voting equipment by combining an optical paper ballot and ballot marking device to allow accessibility for the visually impaired. The system runs the Busybox Linux 1.7.4 operating system...
Busybox Linux 1.7.4 operating system, which has known medium to high level exploitable vulnerabilities to allow remote attackers to compromise the VDS. (J. Moss, H. Hurtsi, M. Blaze et al., Voting Village Report, DEFCON Village Report in association with and Georgetown University
In 2019, a computer laptop and several USB memory cards containing the cryptographic key to access DVS systems were stolen in Philadelphia.
...I believe that USB memory cards were used to facilitate administrative access to the backdoor to disrupt polling operations and impact ballot counting across MI, GA, PA, AZ and WI.
...there is ample indication that these problems were not resolved. Moreover, DVS maintains the position that its voting machines are fully secure. They continue to avoid transparency or make their software codes to be analyzed by independent security investigators.
In my expert opinion, the combination of DVS, Scytl/SOE Software/eClarity and Smartmatic are vulnerable to data manipulation by unauthorized means. My judgment is based on conducting more than a dozen experiments combined with analyzing the 2020 Election data sets @EagleEdMartin
@EagleEdMartin Additionally, a number of investigators have examined DVS and reported their security findings (J. Schwartz, Scientific American Journal, 2018; DEFCON 2019; L. Norden et. al, America’s Voting Machines at Risk, Brennan Center for Justice, NYU Law, 2014) @DrJohnEastman
@EagleEdMartin @DrJohnEastman On approximately 2:30 AM EST, TV broadcasts reported that PA, WI, AZ, NV and GA have decided to cease vote counting operations and will continue the following day. The unanimous decision to intentionally stop counting by all 5... @DrJohnEastman Case 2:20-cv-13134-LVP- Page 5 of 9
@EagleEdMartin @DrJohnEastman Case 2:20-cv-13134-LVP-RSW ECF No. 1-19, PageID.827 Filed 11/25/20 Page 6 of 9...demonstrates prior coordination by election officials in battleground state. There would be no legitimate reason battleground states need to pre-coordinate election activities and stop adjudication
@EagleEdMartin @DrJohnEastman the vote counting did not stop, as reported. In fact, it continued behind closed doors in early hours of November 4, 2020. This activity is highly unusually and demonstrates collusion to achieve desired results without being monitored by watchers.
@EagleEdMartin @DrJohnEastman I conclude that the software algorithm manipulated votes counts forging between 1-2% of the precinct results to favor Vice President Biden. The software performed data alteration in real-time in order to maintain close parity among the candidates and without raising red flags.
@EagleEdMartin @DrJohnEastman The specific software algorithm was developed by Smartmatic and implemented in DVS machines to facilitate backdoor access by a nefarious operator to manipulate live data, as desired.
The DVS Democracy Suite’s ImageCast Central optical scanner failed to correctly verify and ...
The DVS Democracy Suite’s ImageCast Central optical scanner failed to correctly verify and ...
@EagleEdMartin @DrJohnEastman ...and validate absentee ballots, as described in its own literature. There is reported evidence that the optical scanner accepted and adjudicated ballots that did not have signatures or other key features that is required for ballot validation and verification...
@EagleEdMartin @DrJohnEastman ...This indicates that the DVS system configuration was modified to accept invalid ballots when they should have been rejected.
After the DVS ImageCast scanner validates a ballot, by design, it is required to tabulate and store the results in a cast vote record...
After the DVS ImageCast scanner validates a ballot, by design, it is required to tabulate and store the results in a cast vote record...
@EagleEdMartin @DrJohnEastman in a cast vote record along with a human-readable image of the ballot that has been scanned. The image, called AuditMark provides the user with scanned results that is verifiable. However, media reports indicate that not only did the ImageCast fail to properly verify absentee...
@EagleEdMartin @DrJohnEastman .. absentee ballots; it also failed to maintain records of the AutitMark that would be necessary to conduct an audit. The only way to alter this protocol is to alter the system configuration and prevent the ImageCast scanner from rejecting illegal ballots; and reprogram AuditMark
@EagleEdMartin @DrJohnEastman AuditMark to store ballot image
6
Case 2:20-cv-13134-LVP-RSW ECF No. 1-19, PageID.828 Filed 11/25/20 Page 7 of 9
that could be verified. This is evidence of fraud perpetrated to prevent investigators to discover
the number of invalid votes that were cast.
6
Case 2:20-cv-13134-LVP-RSW ECF No. 1-19, PageID.828 Filed 11/25/20 Page 7 of 9
that could be verified. This is evidence of fraud perpetrated to prevent investigators to discover
the number of invalid votes that were cast.
@EagleEdMartin @DrJohnEastman The cryptographic key store on DVS thumb drive (reported stolen in Philadelphia) was used alter
vote counts prior to up chain reporting. Since DVS uses the same cryptographic key for all its voting systems in all battleground states, the key allowed a remote operator...
vote counts prior to up chain reporting. Since DVS uses the same cryptographic key for all its voting systems in all battleground states, the key allowed a remote operator...
@EagleEdMartin @DrJohnEastman remote operator to conduct massive attacks on all battleground state data set without being detected.
Beginning on approximately 4:30 AM EST on November 4, 2020, the vote counts favored Vice President Biden by nearly 80% in many jurisdictions.
Beginning on approximately 4:30 AM EST on November 4, 2020, the vote counts favored Vice President Biden by nearly 80% in many jurisdictions.
@EagleEdMartin @DrJohnEastman The data variance favoring Vice President continues to accelerate after 4:30 AM EST on November 4, 2020 and continues until it momentum through November 9, 2020. This abnormality in variance is evident by the unusually steep slope for Vice President Biden in all battleground
@EagleEdMartin @DrJohnEastman all battleground states on November 4, 2020. A sudden rise in slope is not normal and demonstrates data manipulation by artificial means. E.g. in PA, Pres. Trump’s lead of more than 700,000 count advantage was reduced to less than 300,000 in a few short hours, which does not occu
@EagleEdMartin @DrJohnEastman not occur in the real world without an external influence. I conclude that manually feeding more than 400,000 mostly absentee ballots cannot be accomplished in a short time frame (i.e., 2-3 hours) without illegal vote count alteration...
@EagleEdMartin @DrJohnEastman In another case for Edison County, MI, Vice President Biden received more than 100% of the votes at 5:59 PM EST on November 4, 2020 and again he received 99.61% of the votes at 2:23 PM EST on November 5, 2020. These distributions are cause for concern and indicate fraud.
@EagleEdMartin @DrJohnEastman DVS has acknowledged that Chinese made parts are used in its voting machines. However, the company is unwilling to share details on its supply chains, foreign ownership, or its relationship with China, Venezuela and Cuba...I conclude that FIS and other operators were involved to
@EagleEdMartin @DrJohnEastman I conclude that FIS and other operators were involved to influence the outcome of the 2020 election.
A Man-in-the-Middle (MITM) cyber attack was carried out by covert operators using sophisticated tools
A Man-in-the-Middle (MITM) cyber attack was carried out by covert operators using sophisticated tools
@EagleEdMartin @DrJohnEastman The MITM attack occurred in two ways. Initially, remote operatives used USB memory cards containing cryptographic keys and access system backdoors to alter votes in battleground states. Subsequently, the results were forwarded to Scytl/SOE Software servers located in Frankfurt,
@EagleEdMartin @DrJohnEastman The MITM attack was structured to ensure sufficient data alteration had occurred prior to forwarding the tallied results to the Scytl/eClarity Software Electronic Night Reporting (ENR) system. The reason election data are forwarded overseas is to avoid detection and...
@EagleEdMartin @DrJohnEastman ...detection and monitoring by the USIC to obfuscate the MITM.
In my expert opinion, the DVS Democracy Suite, Scytl/SOE Software/eClarity and Smartmatic have not produced auditable results in the 2020 election...
In my expert opinion, the DVS Democracy Suite, Scytl/SOE Software/eClarity and Smartmatic have not produced auditable results in the 2020 election...
@EagleEdMartin @DrJohnEastman It is evident that ballots were not properly validated, system records were not kept, and the system experience considerable instability even several days prior to November 4, 2020 that require DVS to implement software changes at the last minute...
@EagleEdMartin @DrJohnEastman In addition, the disparity in data distribution after 4:30 AM on November 4, 2020 indicates significant systemic anomalies that were widespread among all battleground states. The evidence is both extensive and persuasive and indicates large-scale fraud by remote operators.
@EagleEdMartin @DrJohnEastman I conclude that a combination of lost cryptographic key contained on stolen USB memory cards, serious exploitable system and software vulnerabilities and operating system backdoor in DVS, Scytl, SOE Software/eClarity and Smartmatic created the...
@EagleEdMartin @DrJohnEastman created the perfect environment to commit widespread fraud in all states where these systems are installed. My analysis of the 2020 Election from NY Times data shows statistical anomalies across the battleground state votes...
@EagleEdMartin @DrJohnEastman These failures are widespread and systemic – and sufficient to invalidate the vote counts.
I conclude with high confidence that the election 2020 data were altered in all battleground states resulting in a hundreds of thousands of votes ...
I conclude with high confidence that the election 2020 data were altered in all battleground states resulting in a hundreds of thousands of votes ...
@EagleEdMartin @DrJohnEastman ...hundreds of thousands of votes that were cast for President Trump to be transferred to Vice President Biden. These alterations were the result of systemic and widespread exploitable vulnerabilities in DVS, Scytl/SOE Software and Smartmatic systems...
@EagleEdMartin @DrJohnEastman that enabled operators to achieve the desired results. In my view, the evidence is overwhelming and incontrovertible.
Pursuant to 28 U.S.S. 1746, I declare under penalty of perjury ...
Pursuant to 28 U.S.S. 1746, I declare under penalty of perjury ...
@EagleEdMartin @DrJohnEastman ...penalty of perjury under the laws of the United States of America that the foregoing is true and correct to the best of my knowledge.
EXECUTED ON: November 25, 2020 By:
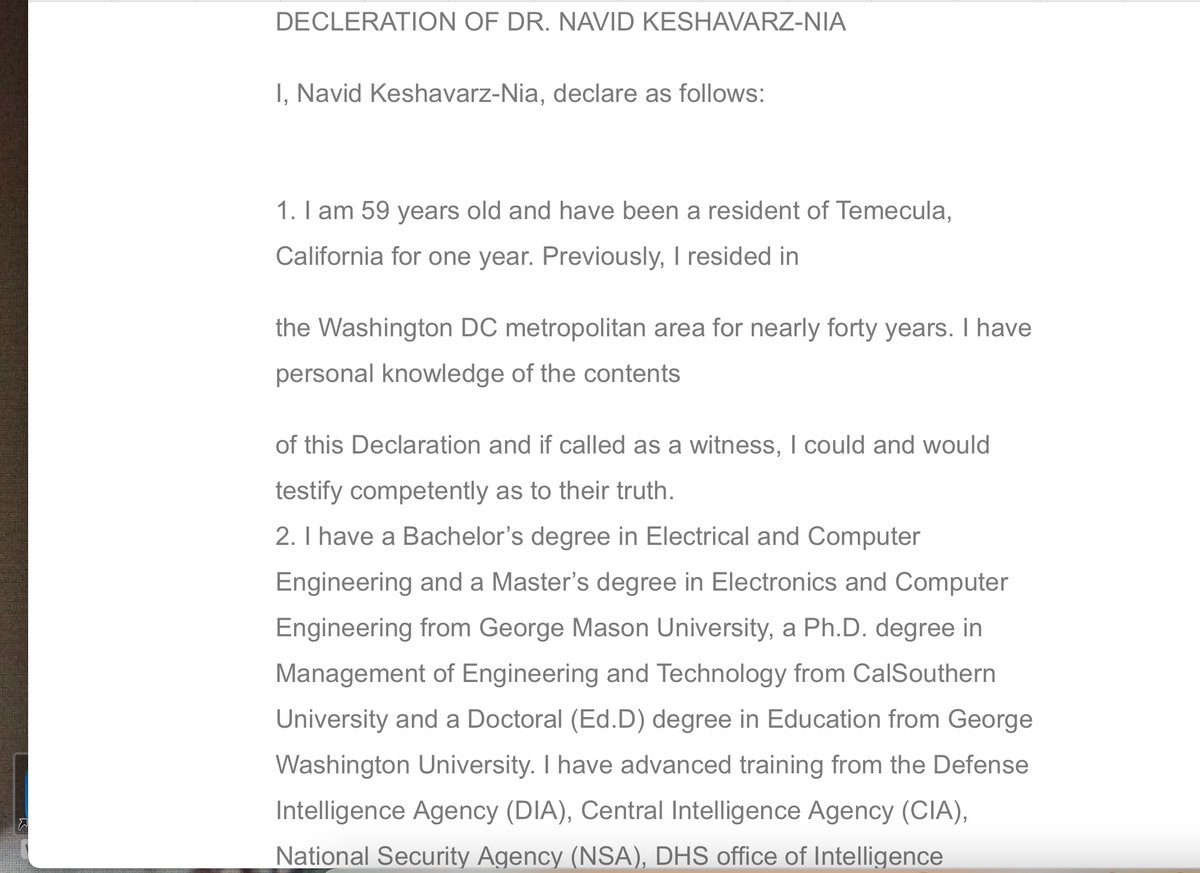
Navid Keshavarz-Nia, Ph.D., Ed.D.
EXECUTED ON: November 25, 2020 By:
Navid Keshavarz-Nia, Ph.D., Ed.D.
@EagleEdMartin @DrJohnEastman @threadreaderapp unroll
• • •
Missing some Tweet in this thread? You can try to
force a refresh