1/4 #PrivExchange by @_dirkjan perfectly illustrates how legacy permissions degrade an Active Directory environment's security posture. I want to share three free resources that will help you proactively protect your organization.
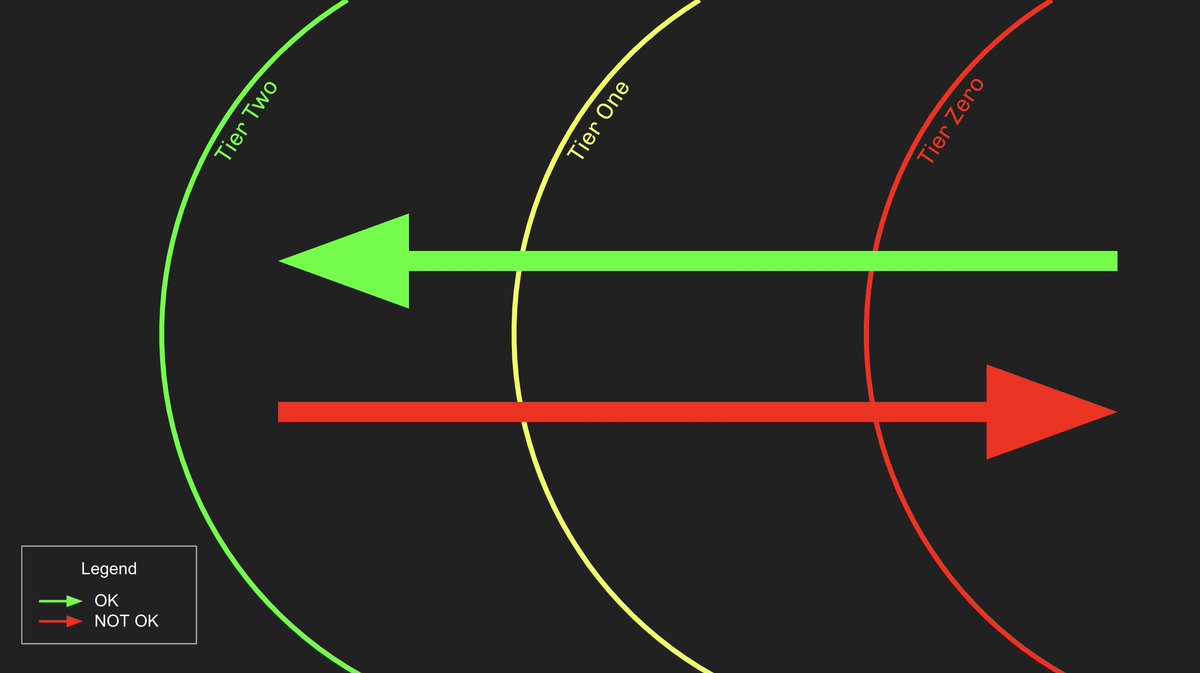
2/4 First is part one introducing our Adversary Resilience methodology. Part one covers the high level concepts of this new methodology:
posts.specterops.io/introducing-th…
posts.specterops.io/introducing-th…
3/4 Second is part two introducing our Adversary Resilience methodology, and shows the nuts and bolts involved. We've made big improvements to the methodology since its introduction and will be speaking about those publicly at @WEareTROOPERS in March:
posts.specterops.io/introducing-th…
posts.specterops.io/introducing-th…
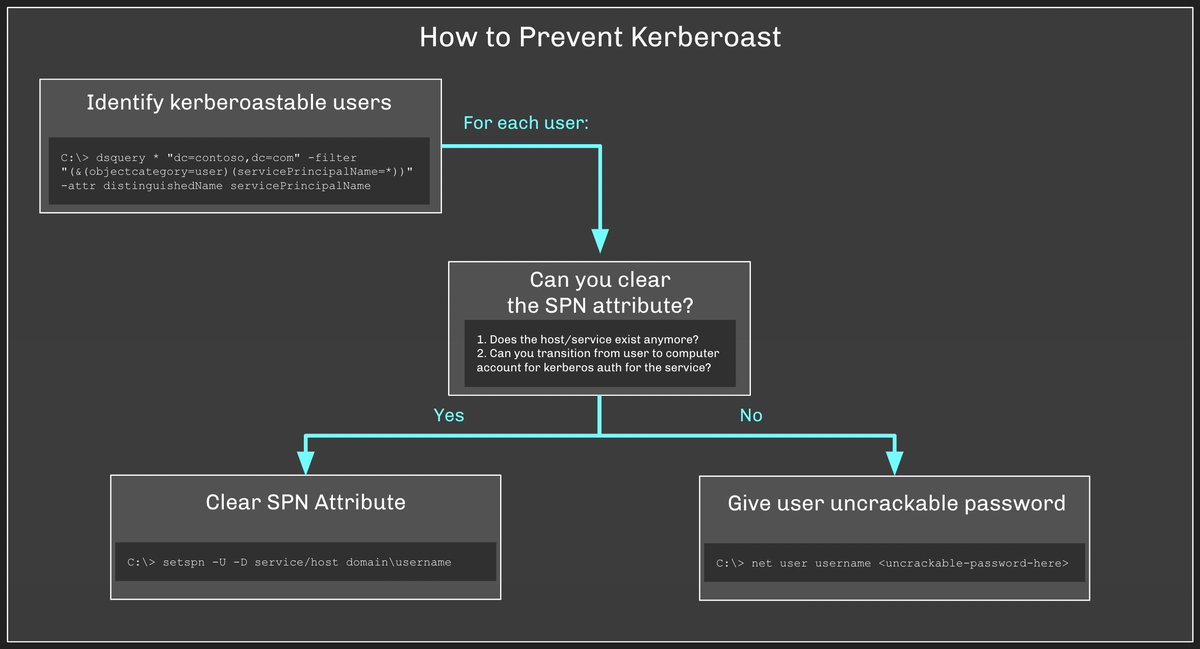
4/4 Finally, we did a @BlackHatEvents webcast last April showing you how to find and mitigate dangerous legacy permissions in AD and focused on Exchange:
register.gotowebinar.com/register/66616…
register.gotowebinar.com/register/66616…
• • •
Missing some Tweet in this thread? You can try to
force a refresh