🆕 🔥 Research on PDB Paths from @stvemillertime: fireeye.com/blog/threat-re…
#DFIR primer & exploration of these wonderful artifacts.
Followed by a survey of malware PDB conventions, PDB anomalies, attacker mistakes. All with attribution, including Western gov.
THREAD (1/n)



#DFIR primer & exploration of these wonderful artifacts.
Followed by a survey of malware PDB conventions, PDB anomalies, attacker mistakes. All with attribution, including Western gov.
THREAD (1/n)




Includes considerations for #threatintel shops, red teams/operators, and weaknesses in PDB paths.
Blog also has: the most malware code families and threat groups we've ever published, some spicy groups, and some light swearing (malware devs are potty mouths) #SwearEngine
2/n

Blog also has: the most malware code families and threat groups we've ever published, some spicy groups, and some light swearing (malware devs are potty mouths) #SwearEngine
2/n


I love that @stvemillertime surfaced a bunch of strange PDB path anomalies and dug in with @mikesiko's #FLARE team to get to ground truth & replicate the artifact.
fireeye.com/blog/threat-re…
Where my #DFIR followers at?
❓ Curious if you've found other anomalies not listed?
3/n

fireeye.com/blog/threat-re…
Where my #DFIR followers at?
❓ Curious if you've found other anomalies not listed?
3/n


"Our adversaries are human. They err. And when they do, we can catch them."
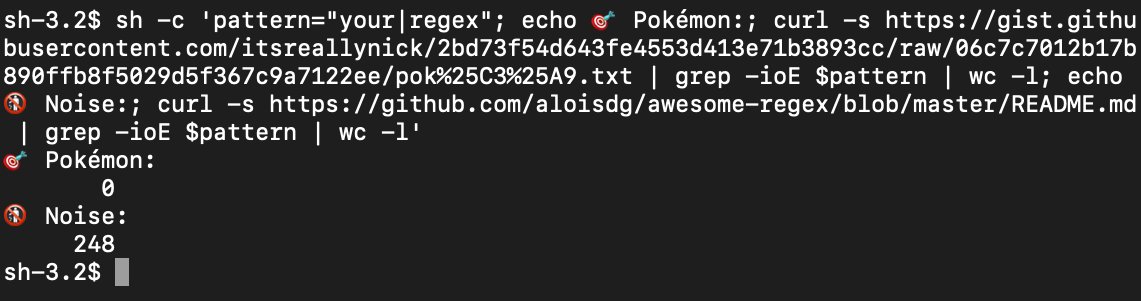
ConventionEngine yara rules covering 300 mal fams, 39 APT & FIN groups, and 200+ UNC (uncategorized) groups: fireeye.com/content/dam/fi…
I snuck some in too!
Usage:
4/n
ConventionEngine yara rules covering 300 mal fams, 39 APT & FIN groups, and 200+ UNC (uncategorized) groups: fireeye.com/content/dam/fi…
I snuck some in too!
Usage:
https://twitter.com/ItsReallyNick/status/1151093745976315905?s=19@cyb3rops 👀
4/n
There's so much to unpack here - and this was just part 1.
Thanks @stvemillertime for taking your original tweet thread that might be hard to find
And expanding it, turning it into something substantial & permanent.
Pumped for part 2.
(5/5)
Thanks @stvemillertime for taking your original tweet thread that might be hard to find
https://twitter.com/stvemillertime/status/1059650974166515712?s=19
And expanding it, turning it into something substantial & permanent.
Pumped for part 2.
(5/5)
• • •
Missing some Tweet in this thread? You can try to
force a refresh