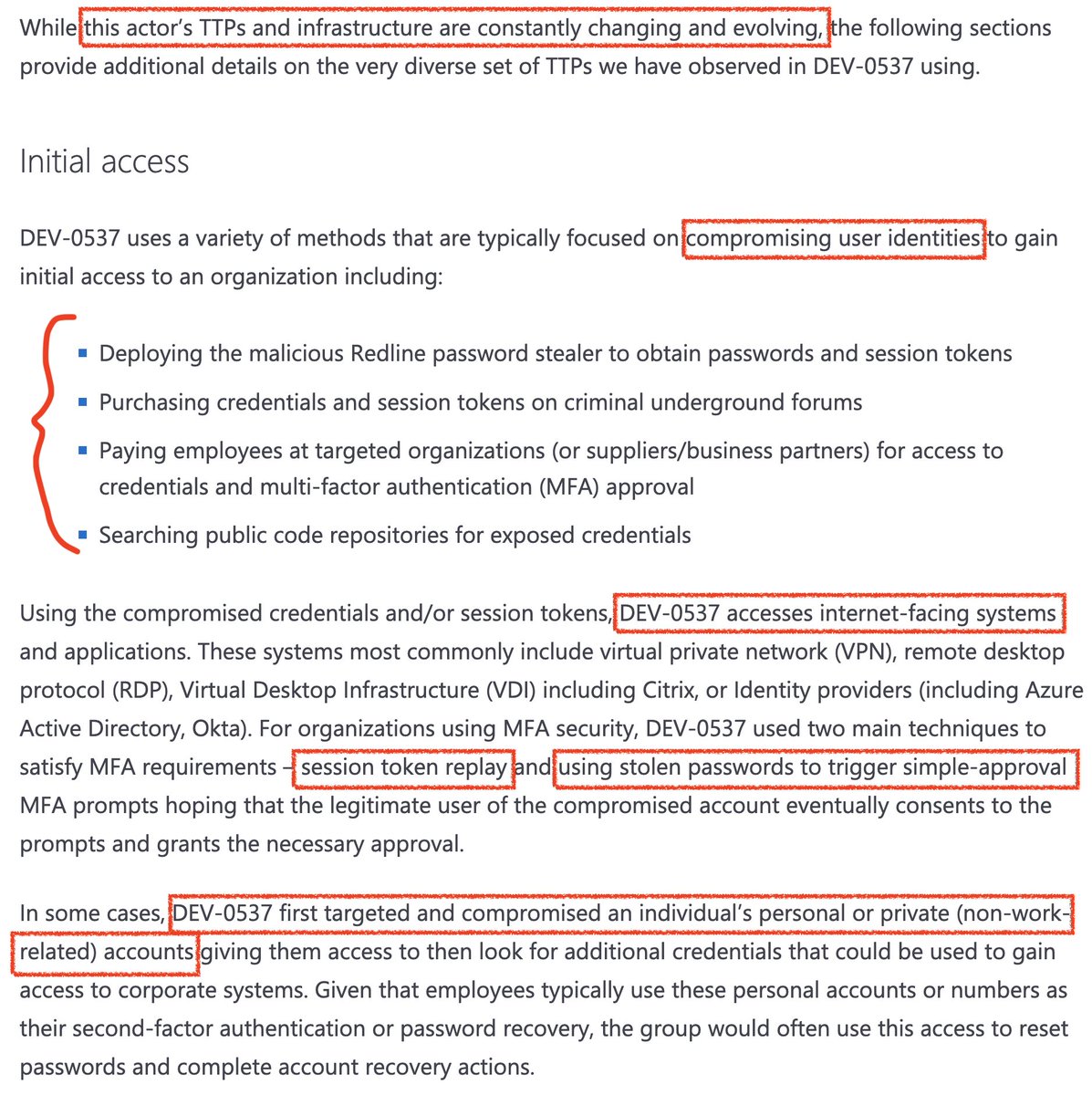
🆕 Microsoft.Workflow.Compiler sample with low VT detection!
1⃣C:\ProgramData\ccm_deploy.xml 🧐
MD5 fb98cddfa2e13334989d27d1b5b7cdda
VT (0/56): virustotal.com/gui/file/8b6d8…
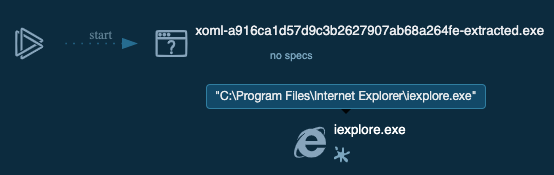
2⃣Loads C:\ProgramData\package.xml
MD5 a916ca1d57d9c3b2627907ab68a264fe
VT (1/58): virustotal.com/gui/file/9a8b5…
[1/4]
1⃣C:\ProgramData\ccm_deploy.xml 🧐
MD5 fb98cddfa2e13334989d27d1b5b7cdda
VT (0/56): virustotal.com/gui/file/8b6d8…
2⃣Loads C:\ProgramData\package.xml
MD5 a916ca1d57d9c3b2627907ab68a264fe
VT (1/58): virustotal.com/gui/file/9a8b5…
[1/4]

I uploaded both to @virusbay_io: beta.virusbay.io/sample/browse/…
and the extracted payload to @anyrun_app: app.any.run/tasks/35c09520…
STDOUT:
Injection Target Process = %ProgramFiles%\Internet Explorer\iexplore.exe
PPID Spoof Parent = True
PPID Spoof Process = explorer
Returned true
[2/4]
and the extracted payload to @anyrun_app: app.any.run/tasks/35c09520…
STDOUT:
Injection Target Process = %ProgramFiles%\Internet Explorer\iexplore.exe
PPID Spoof Parent = True
PPID Spoof Process = explorer
Returned true
[2/4]
@virusbay_io @anyrun_app More info on @mattifestation's method:
1⃣ My favorite implementation uploaded publicly is this Excel file (probably authored by @egyed_laszlo):
2⃣ The first workflow VT sample uploaded was ~1 year ago:
^plus background & links
[3/4]
1⃣ My favorite implementation uploaded publicly is this Excel file (probably authored by @egyed_laszlo):
https://twitter.com/ItsReallyNick/status/1062408913688166400?s=20
2⃣ The first workflow VT sample uploaded was ~1 year ago:
https://twitter.com/ItsReallyNick/status/1052591426851299330?s=20
^plus background & links
[3/4]
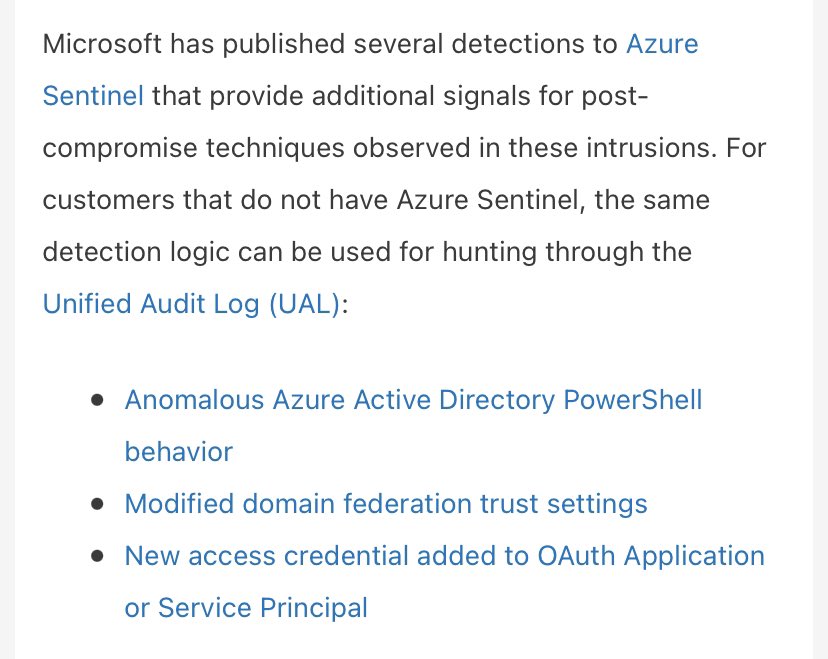
VT detections aren't representative of security vendors' full detection posture.
But, because this had poor coverage (and only @cyb3rops had helpful context on the XOML's mem process write), I'm sharing my Aug 2018 #DailyWorkflow rules if they help: gist.github.com/itsreallynick/…
[4/4]
But, because this had poor coverage (and only @cyb3rops had helpful context on the XOML's mem process write), I'm sharing my Aug 2018 #DailyWorkflow rules if they help: gist.github.com/itsreallynick/…
[4/4]

@cyb3rops 🆓 BONUS TWEET:
NOTE: @anyrun_app you might be interested in improving execution optics for #TIBERIUS, linked 👆🏽 in the 2nd tweet 😉
https://twitter.com/ItsReallyNick/status/1187383931278114816?s=20#threatintel care of #AdvancedPractices 🦅 teammate @a_tweeter_user
NOTE: @anyrun_app you might be interested in improving execution optics for #TIBERIUS, linked 👆🏽 in the 2nd tweet 😉
@cyb3rops @a_tweeter_user @anyrun_app 🆓🆓 DOUBLE BONUS: here are resume-themed phishing documents dating back to February that load shellcode the same way - plus links to the original tweet shares:
Good example of the #threatintel you can extract from Twitter, if you know how to use it.
https://twitter.com/ItsReallyNick/status/1187418041816104960?s=20
Good example of the #threatintel you can extract from Twitter, if you know how to use it.
#blueteam take note:
• package.xml, pushed via ccm_deploy.xml 🤔 #ConfigMgr is a Workflow.Compiler payload
• the EXE is padded with a single null byte so regular b64(EXE file magic) doesn't work
• the solution? ...
• package.xml, pushed via ccm_deploy.xml 🤔 #ConfigMgr is a Workflow.Compiler payload
https://twitter.com/ItsReallyNick/status/1187378435045429249?s=19containing a Base64-encoded executable
• the EXE is padded with a single null byte so regular b64(EXE file magic) doesn't work
• the solution? ...
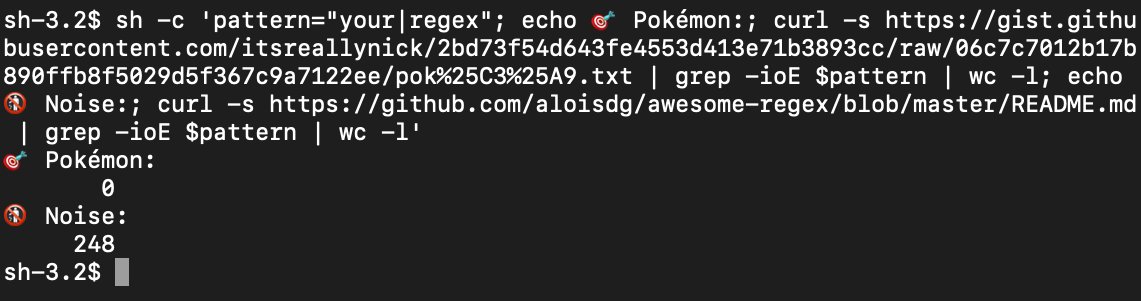
...is for #detection engineers to account for all three possible Base64 encodings (with 0-2 pad bytes)
Python & PowerShell tools from @DavidPany @JohnLaTwC @Lee_Holmes @DissectMalware:
Try with default MS-DOS stub
"This program cannot be run in DOS mode"
Python & PowerShell tools from @DavidPany @JohnLaTwC @Lee_Holmes @DissectMalware:
https://twitter.com/ItsReallyNick/status/1034472940723744768?s=19
Try with default MS-DOS stub
"This program cannot be run in DOS mode"
@DavidPany @JohnLaTwC @Lee_Holmes @DissectMalware Here's a fresh one from the same intrusion operator:
💾"0X1F588277.doc"
#⃣957e8d6aa08af8c5d82cc3f5f23d86a5
🔗virustotal.com/gui/file/750d1…
👿#EGGHUNT & #BEACON backdoors
🔃35.236.203.52/match
👨💻#UNC1739 (🟥 team)
^very worth your time to chase, they do cool stuff 🤩
I made a logo 😉🙃
💾"0X1F588277.doc"
#⃣957e8d6aa08af8c5d82cc3f5f23d86a5
🔗virustotal.com/gui/file/750d1…
👿#EGGHUNT & #BEACON backdoors
🔃35.236.203.52/match
👨💻#UNC1739 (🟥 team)
^very worth your time to chase, they do cool stuff 🤩
I made a logo 😉🙃

@DavidPany @JohnLaTwC @Lee_Holmes @DissectMalware Much newer #UNC1739 tradecraft: praetorian.com/blog/extending… 👀
Neat stuff - excited to see it in-the-wild!
Neat stuff - excited to see it in-the-wild!
I wonder how #FLOSS does against this new string obfuscation github.com/fireeye/flare-…
Putting this on my fridge
https://twitter.com/itsreallynick/status/1232868850175266817?s=21https://t.co/UTRCfZzQia
• • •
Missing some Tweet in this thread? You can try to
force a refresh