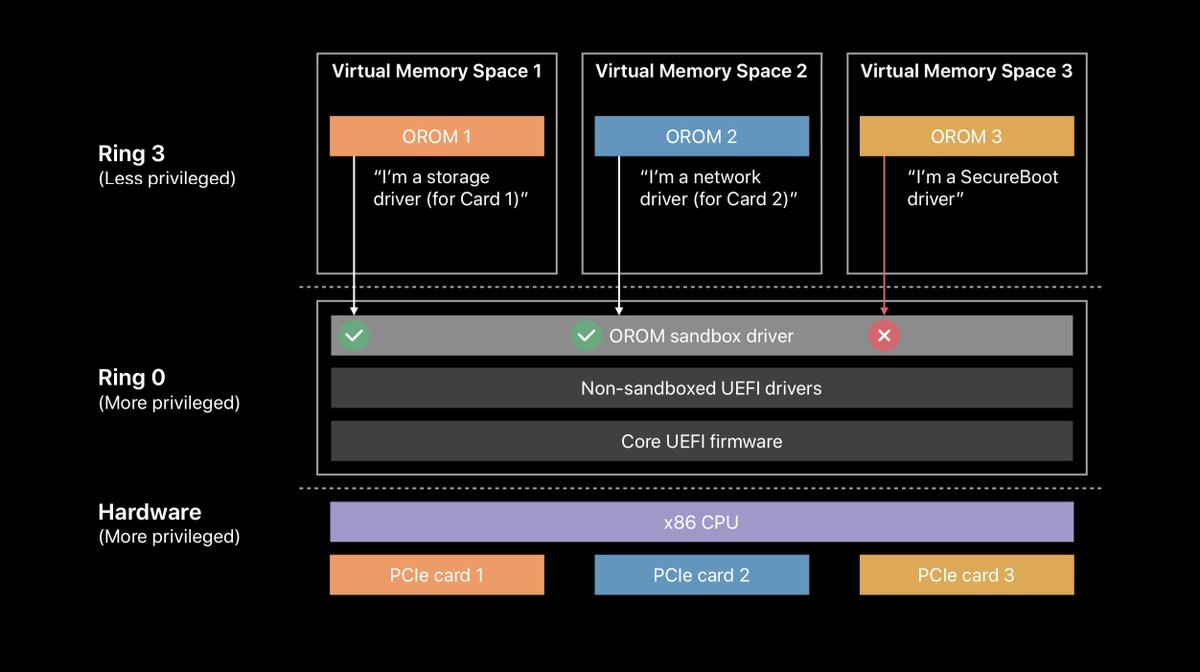
Check it out for more about the first-in-the-world work @coreykal & Rafal Wojtczuk have done for UEFI DMA protection and UEFI sandboxing of PCIe Option ROMs
https://twitter.com/radian/status/1197990878540775424
@coreykal Or for the work @NikolajSchlej and I did on bringing SecureBoot to the Mac
@coreykal @NikolajSchlej Enabling VT-d before there's even RAM available? It's what you gotta do ¯\_(ツ)_/¯ 

@coreykal @NikolajSchlej Moving from a monolithic ring 0, anyone-who-gets-in-wins memory space to the ring 0/ring 3 + virtual memory separation we depend on in all other contexts? Sure, why not 


• • •
Missing some Tweet in this thread? You can try to
force a refresh




