
Interested in reverse engineering, firmware, bluetooth, trusted computing, and training. Founder of OpenSecurityTraining2 https://t.co/slK2fsMRwU
How to get URL link on X (Twitter) App

https://twitter.com/marcan42/status/1504097192323465216“The entire architecture is complicated and the details subtle”
https://twitter.com/xenokovah/status/1489622745772134403About half the time was understanding and then half writing it back up in pretty form. (There were no diagrams in the original writeup!) But also I suspect the actual videos will be about 50% longer too (since the number of slides is about 50% larger than some other examples).
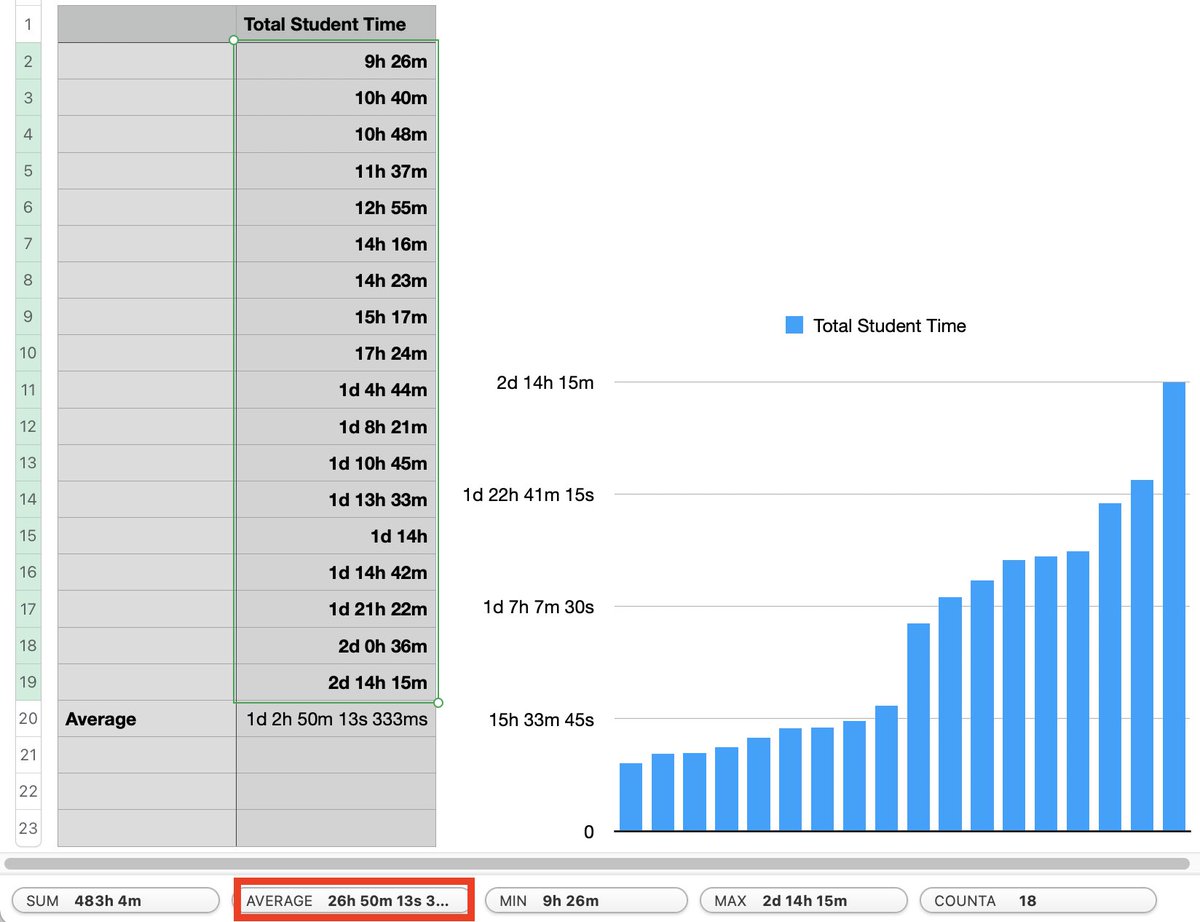
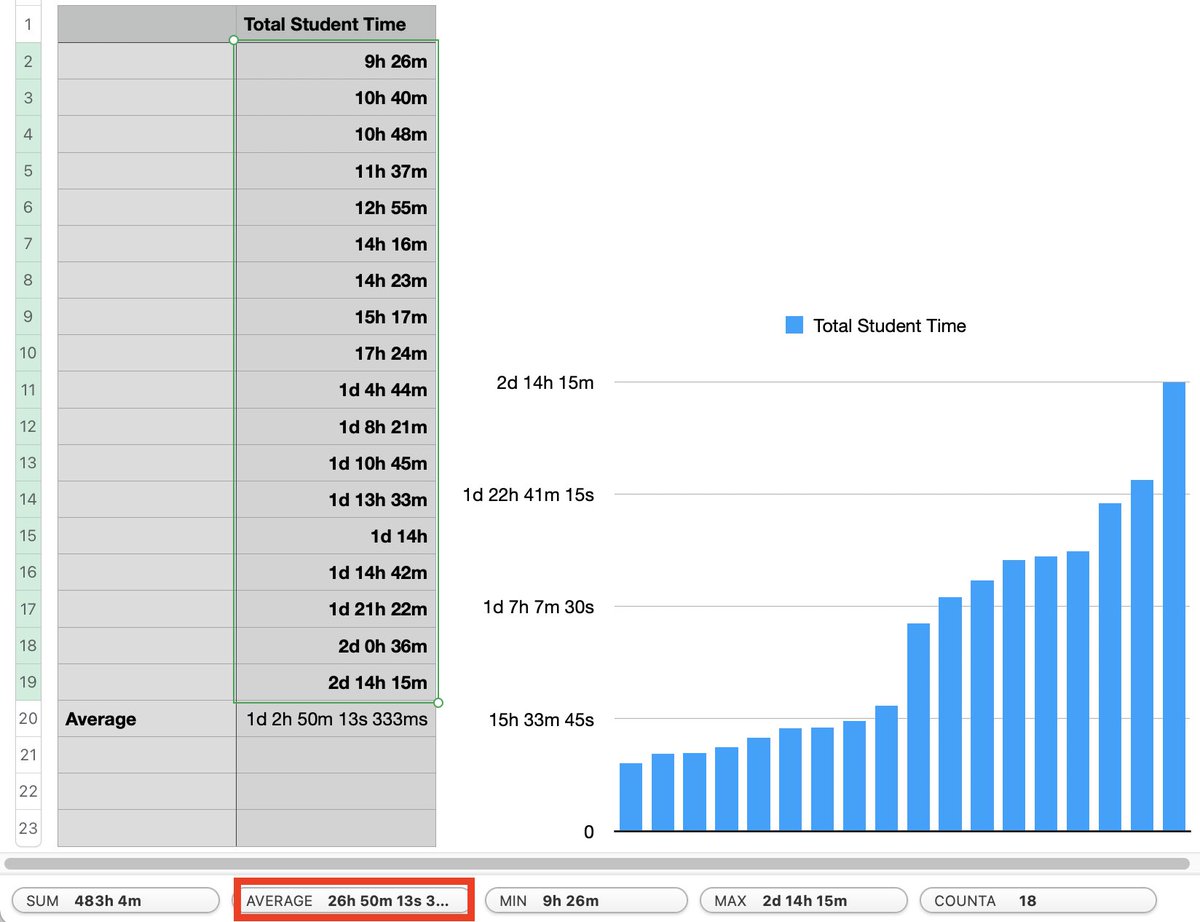 1) This was originally created targeting about 2 days (~14 hours after subtracting lunch ;)) of in-person delivery. You can see a *few* students could do it in that time, but most needed more time. This is why I really like that I can now let students learn at their own pace
1) This was originally created targeting about 2 days (~14 hours after subtracting lunch ;)) of in-person delivery. You can see a *few* students could do it in that time, but most needed more time. This is why I really like that I can now let students learn at their own pace
https://twitter.com/dwizzzleMSFT/status/1425495829511430145I termed the security goal “P != X” meaning mere physical possession *in and of itself* should not equal code execution. Rather, possession must be combined with knowledge of an administrator password before you could disable that critical security feature.

https://twitter.com/radian/status/1197990878540775424@coreykal Or for the work @NikolajSchlej and I did on bringing SecureBoot to the Mac