🔨A Tough Outlook for Home Page Attacks
🔗fireeye.com/blog/threat-re…
Blog has #APT33 🇮🇷, #APT34 🇮🇷, and #UNC1194 🏴😉 home page persistence & RCE.
🔒We talk CVE-2017-11774 patch tampering in-the-wild and made a hardening guide!
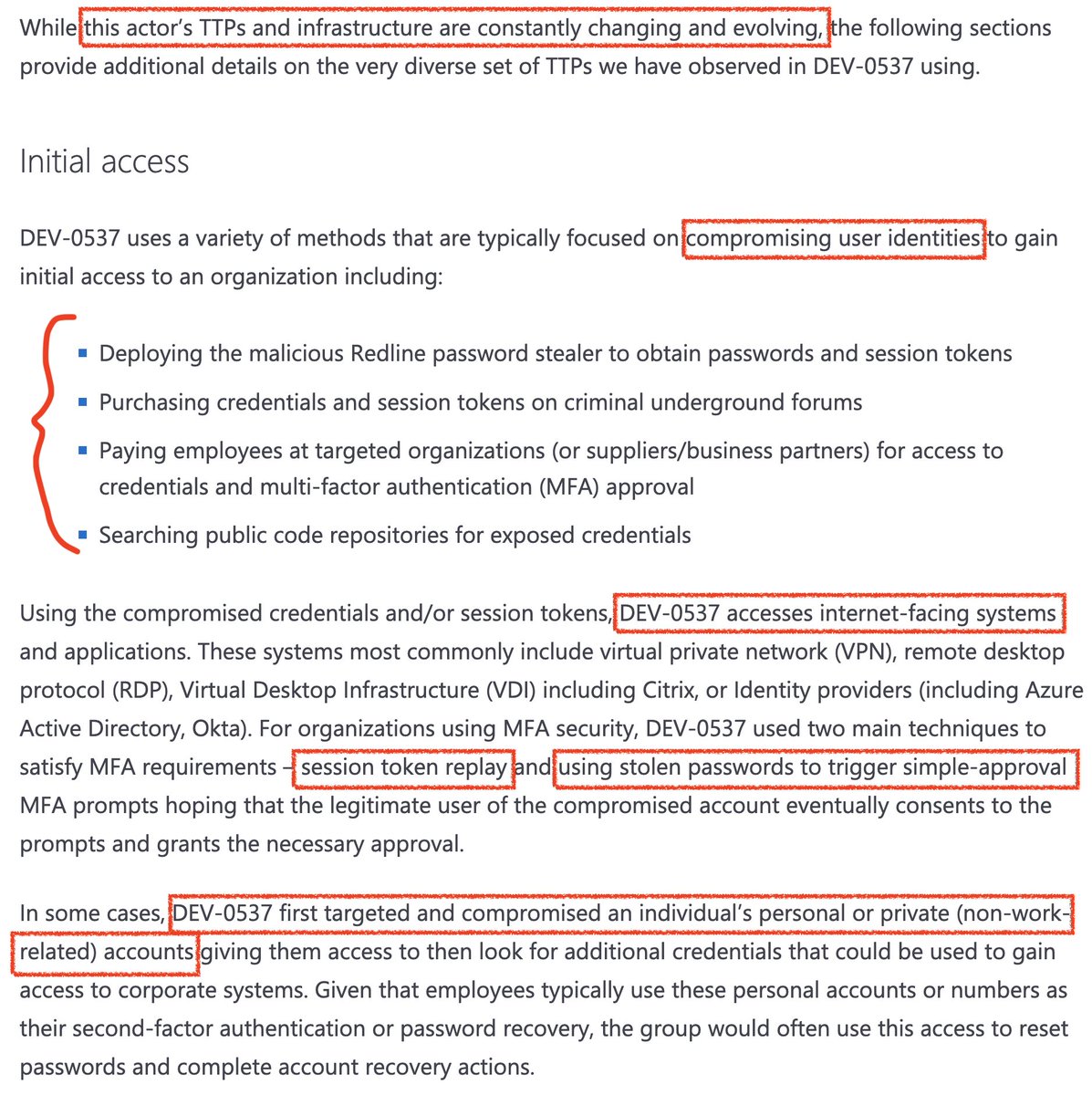
😱Cool TTPs (pictured) #GuardrailsOfTheGalaxy

🔗fireeye.com/blog/threat-re…
Blog has #APT33 🇮🇷, #APT34 🇮🇷, and #UNC1194 🏴😉 home page persistence & RCE.
🔒We talk CVE-2017-11774 patch tampering in-the-wild and made a hardening guide!
😱Cool TTPs (pictured) #GuardrailsOfTheGalaxy


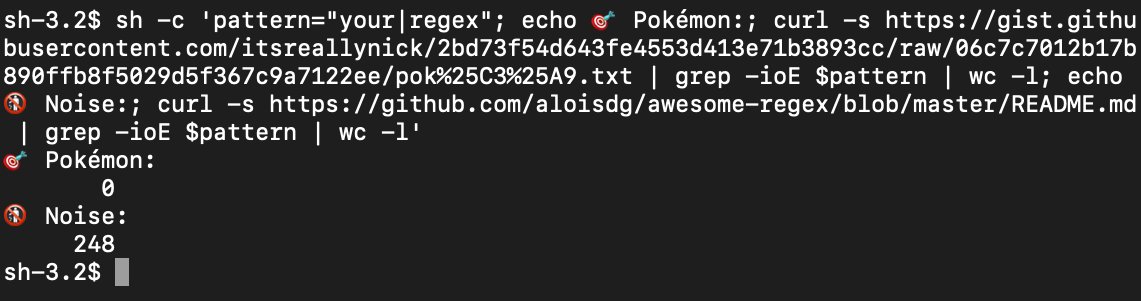
Here is the #UNC1194 first stage (recon) payload stored in an attacker-controlled @Azure storage blob:
Pretty neat that the attacker (@TrustedSec) can conduct a full intrusion by just swapping the storage blob content for the next stage!
https://twitter.com/itsreallynick/status/1199209513137688576
Pretty neat that the attacker (@TrustedSec) can conduct a full intrusion by just swapping the storage blob content for the next stage!
This was a fun one to write with McWhirt & @doughsec. We ended up with 3 registry settings to enforce with Group Policy for CVE-2017-11774 Outlook hardening:
fireeye.com/blog/threat-re…
Final step is to enforce GPO reprocessing.
fireeye.com/blog/threat-re…
Final step is to enforce GPO reprocessing.

We linked to a ton of great content from people we coordinated this blog with, including @msftsecresponse, @TrustedSec/@HackingDave, @sensepost/@_staaldraad, @S0utc4st, and Aristotle 🙃
We’d love to hear from #redteam if you’re able to somehow evade the Outlook lockdown guide.
We’d love to hear from #redteam if you’re able to somehow evade the Outlook lockdown guide.

@msftsecresponse @TrustedSec @HackingDave @sensepost @_staaldraad @S0utc4st I understand the #UNC1194 🏴¹ Excel phish from the blog has been removed from @virustotal. Here's the original upload notification [pictured]
¹@Twitter really needs to support US state flag emojis (blog.emojipedia.org/us-state-flag-…) to support my threat actor tweetribution needs
¹@Twitter really needs to support US state flag emojis (blog.emojipedia.org/us-state-flag-…) to support my threat actor tweetribution needs

@msftsecresponse @TrustedSec @HackingDave @sensepost @_staaldraad @S0utc4st @virustotal @Twitter Oh snap @HackingDave with the 🔥 in @WIRED: wired.com/story/microsof…
Or in tweet form 🤣:
Dave and team are fantastic intrusion operators educating defenders here - and they're a blast to chase around! More #UNC11994 cat & mouse please 🙏
Or in tweet form 🤣:
https://twitter.com/HackingDave/status/1199065677065314307?s=20
Dave and team are fantastic intrusion operators educating defenders here - and they're a blast to chase around! More #UNC11994 cat & mouse please 🙏

• • •
Missing some Tweet in this thread? You can try to
force a refresh