PRC influence network: "[Posed] as locals in countries they targeted, post in Groups, amplify their own content, manage Pages, like and comment on other people’s posts particularly about naval activity in the South China Sea, including US Navy ships." about.fb.com/news/2020/09/r…
"In SE Asia where this network focused most of its activity, they posted in Chinese, Filipino & English about global news and current events including Beijing’s interests in the South China Sea; Hong Kong; content supportive of President Rodrigo Duterte & [Sarah's] potential run"
Chinese networks dabbling with IRA division tactics here: "In the US, where this network focused the least and gained almost no following, they posted content both in support of and against presidential candidates Pete Buttigieg, Joe Biden and Donald Trump."
Although Facebook's investigation finds links to Fujian for the first network disclosed, they don't publicly break out the exact origins. There are surely Chinese companies acting as guns-for-hire for other governments too, as we've seen a bit in prior commercial-like bot nets. 

As Graphika points out, Facebook used more direct language with the Hong Kong influence network: "individuals associated with the Chinese government." They don't here. But the focus of this network fits into the overall PRC pattern. 
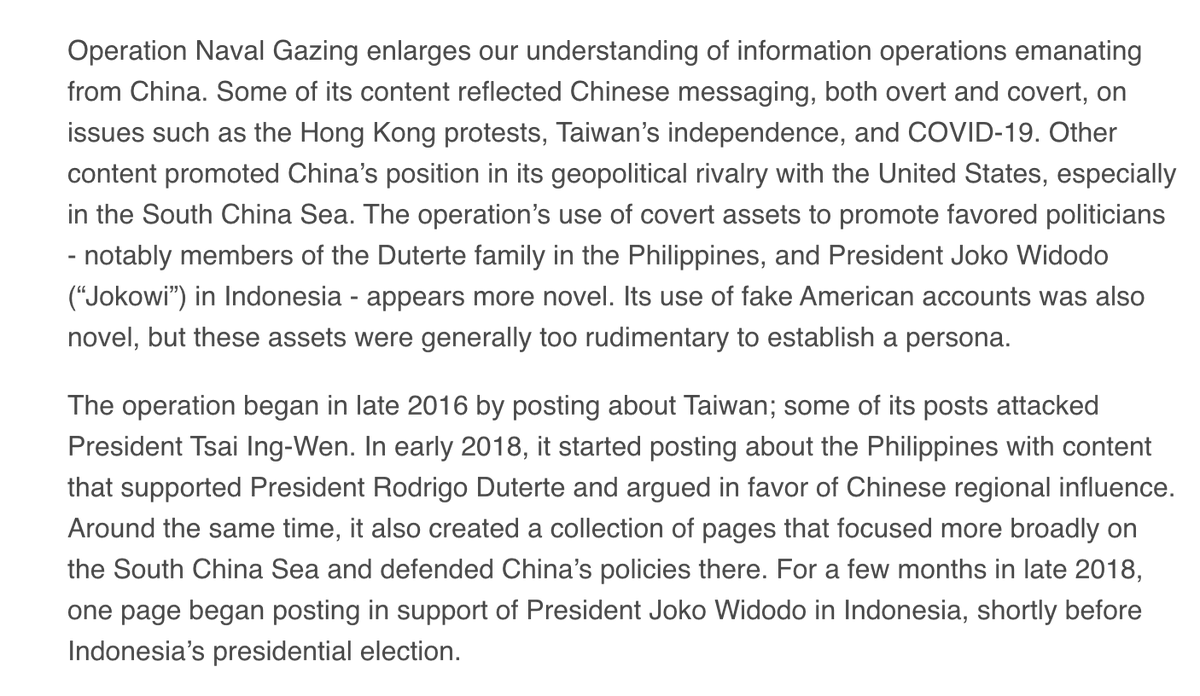
Graphika's report: graphika.com/reports/operat…
Facebook is more direct with regard to the second network: "Although the people behind this activity attempted to conceal their identities, our investigation found links to Philippine military and Philippine police." 

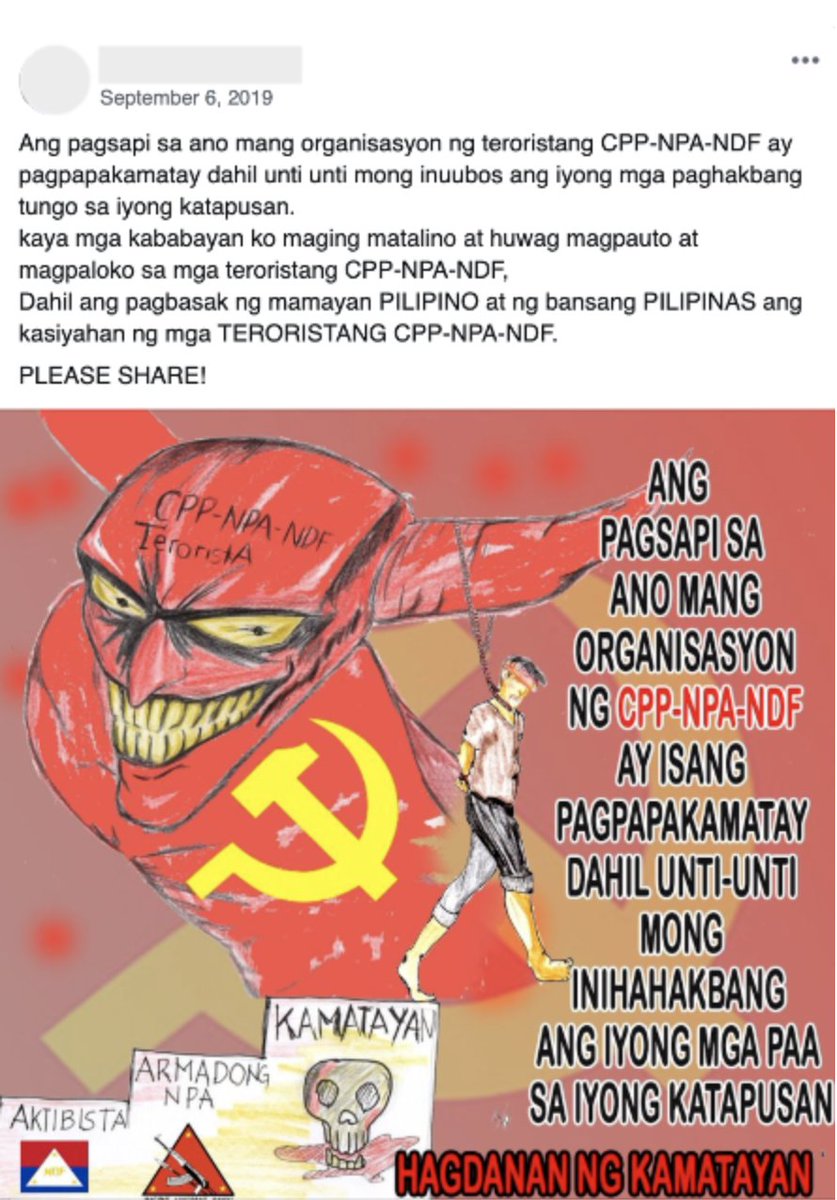
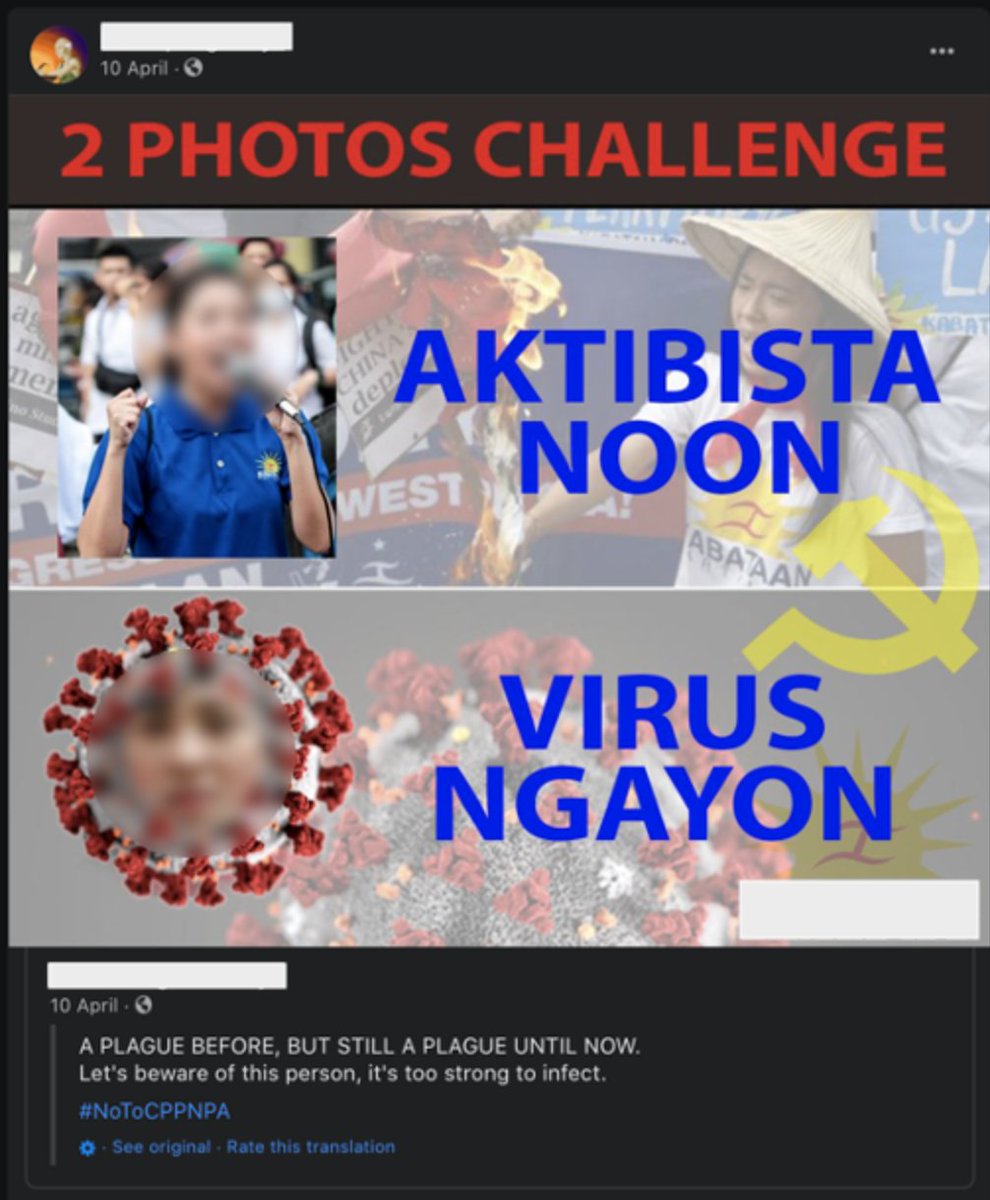
DFR's breakdown focuses on the second network, which is linked to the Philippine military:
https://twitter.com/DFRLab/status/1308496839981830149?s=20
GAN's once again. ML will continue to be a growing threat in this area:
https://twitter.com/benimmo/status/1308494803647320069?s=20
With OpenAI officially commercializing today with Microsoft gaining an exclusive GPT-3 license, we're off to the races. I have no doubt that these models are already being used by influence actors. openai.com/blog/openai-li…
Take for example @liamport9's impressive GPT-3 generated Substack that took HackerNews by storm. "Only ONE PERSON has noticed it was written by GPT-3." liamp.substack.com/p/my-gpt-3-blo…
“It was super easy, actually, which was the scary part.” technologyreview.com/2020/08/14/100…
This tactic is an important distinction. It shows that nefarious actors are willing to strategically invest in longer-term influence operations:
https://twitter.com/benimmo/status/1308498417484795904?s=20
At the same time influence actors are investing in more 'authentic' networks, with genuine audiences, they are also surely investing is obfuscation infrastructure. The adversarial nature means platforms can't as transparently disclose those findings. Not a singular arms race.
• • •
Missing some Tweet in this thread? You can try to
force a refresh