
I see the Quiz is not easy for many, so let's look at particular events together and learn a little bit.
Let's try to think like an analysts!
1. "Medim" IL powershell.exe spawns "Medium" IL Wusa.exe, UAC is enabled on machine, so this is an expected behaviour:
Let's try to think like an analysts!
1. "Medim" IL powershell.exe spawns "Medium" IL Wusa.exe, UAC is enabled on machine, so this is an expected behaviour:
https://twitter.com/BlackMatter23/status/1414969877656391687

1.1 As we know, Wusa.exe has "autoElevate" = TRUE in its manifest, that means it will be automatically elevated by UAC without consent prompt (except "AlwaysNotify" mode). So, svchost.exe spawns consent.exe: 

1.2 The next part is very interesting. You say - powershell.exe spawns "High" IL wusa.exe. Of course it's not! The real parent of wusa is "System" IL svchost.exe which then replaces the parent process with powershell.exe (as initiator). Look at the event below: 

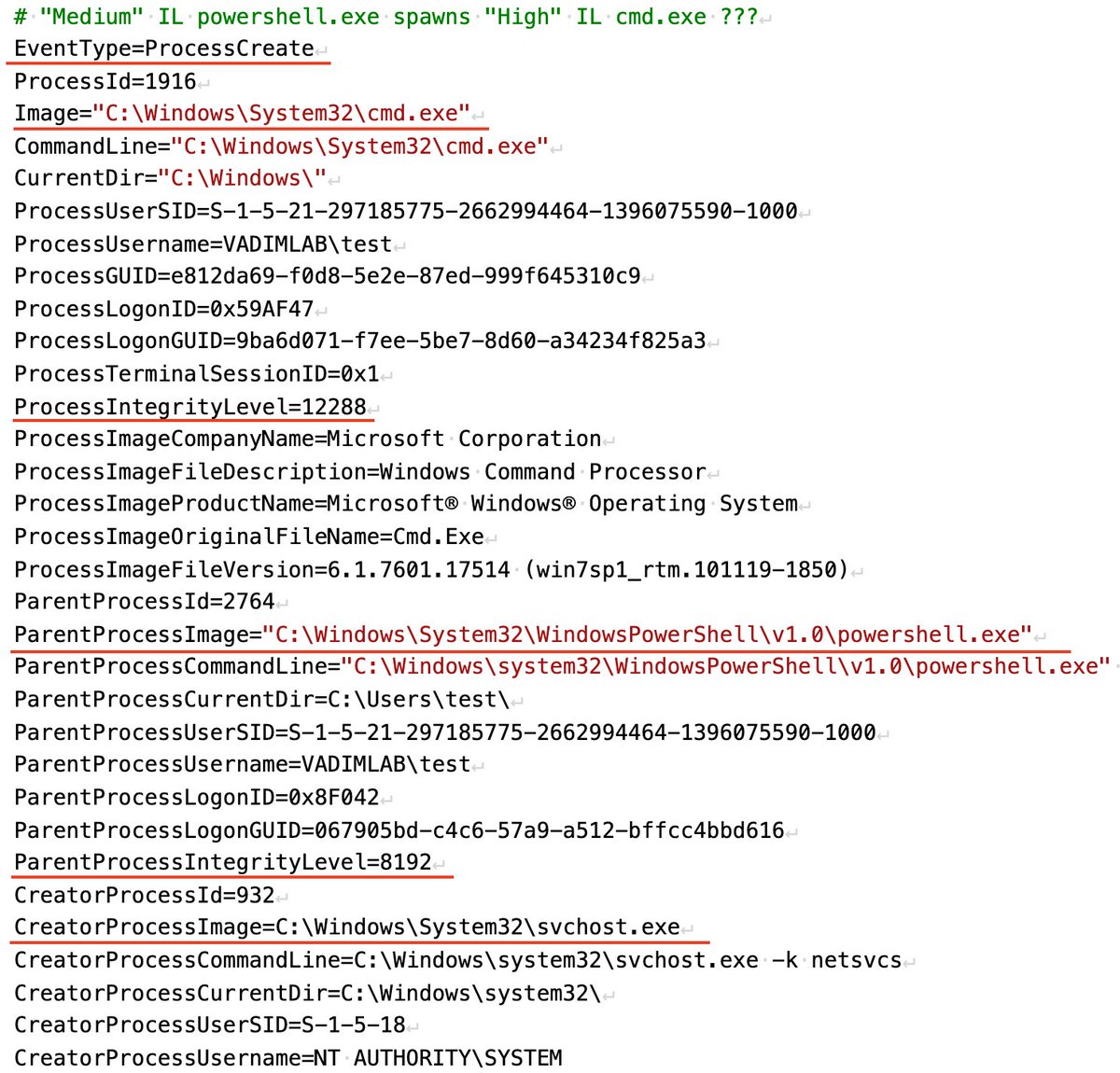
1.3 And the last event we have in this magic attack - "Medium" IL powershell.exe spawns "High" IL cmd.exe. Is cmd.exe "autoelevated" binary? No, it's not. But how it is possible at all, where is the normal UAC events - consent.exe etc? 
1.4 That's all events we have. There're no other events. And now, having all this information, think again and find the 1st answer, find the right technique used by an attacker. The rest should be easier😉
• • •
Missing some Tweet in this thread? You can try to
force a refresh



