New Cobalt Strike bugs allow takedown of attackers’ servers - @serghei
bleepingcomputer.com/news/security/…
bleepingcomputer.com/news/security/…
@serghei SentinelLabs found the DoS vulnerabilities tracked as CVE-2021-36798 and dubbed Hotcobalt in the latest versions of Cobalt Strike's server.
bleepingcomputer.com/news/security/…
bleepingcomputer.com/news/security/…
The Hotcobalt bugs can be exploited by registering fake beacons which help crash Cobalt Strike C2 servers, blocking C2 comms and new beacon deployments.
Law enforcement and researchers can also use Hotcobalt to take down malicious infrastructure.
bleepingcomputer.com/news/security/…
Law enforcement and researchers can also use Hotcobalt to take down malicious infrastructure.
bleepingcomputer.com/news/security/…
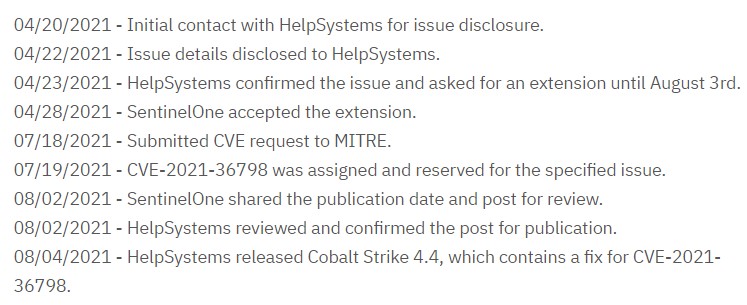
SentinelLabs has disclosed the Hotcobalt vulnerabilities to CobaltStrike's parent company HelpSystems on April 20, who addressed them in Cobalt Strike 4.4, released earlier today. 
• • •
Missing some Tweet in this thread? You can try to
force a refresh