
Some updates on this suspected #Lazarus #APT:(thread, 1/4)
1) The remote template is VBA stomped or at least it was able to hide itself from olevba and oledump
2) The remote template drops an obfuscated vbs file and registers it as a scheduled service



1) The remote template is VBA stomped or at least it was able to hide itself from olevba and oledump
2) The remote template drops an obfuscated vbs file and registers it as a scheduled service
https://twitter.com/h2jazi/status/1429830760677183492



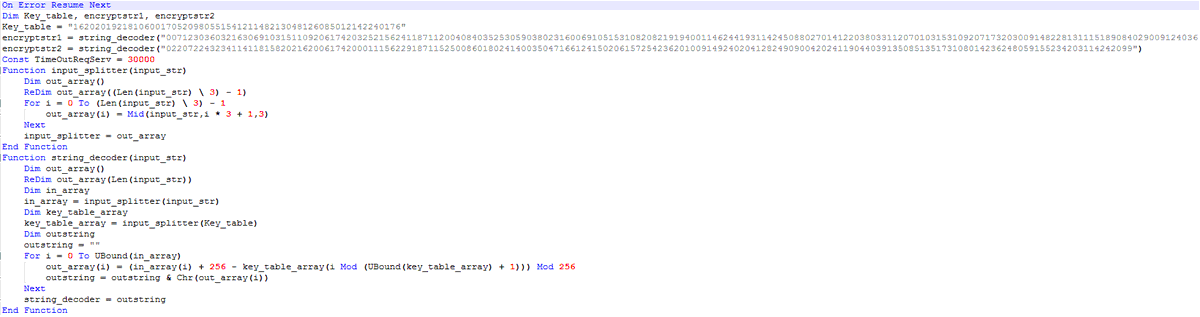
3) All the strings in "OneDriveUpdateNew.vbs" are obfuscated and are decoded using "string_decoder" function with a hardcoded key table.
You can see the decoder and list of the decoded strings used by this vbs file here:
github.com/HHJazi/APT
2/4

You can see the decoder and list of the decoded strings used by this vbs file here:
github.com/HHJazi/APT
2/4

4) The vbs file collects the victim info and builds an HTTP request:
"Username-ComputerName_UUID;OSName"
5) Then it encodes the request using hard coded key and sends the generated request to C2
6) Receives a payload from the C2 and writes it into "%APPDATA%/OD_update.exe"
3/4

"Username-ComputerName_UUID;OSName"
5) Then it encodes the request using hard coded key and sends the generated request to C2
6) Receives a payload from the C2 and writes it into "%APPDATA%/OD_update.exe"
3/4


7) Executes the payload using Wscript Shell
0129323e1551dfff659cf5932ddb19e0
rocksinger[.]xyz
4/4
0129323e1551dfff659cf5932ddb19e0
rocksinger[.]xyz
4/4
• • •
Missing some Tweet in this thread? You can try to
force a refresh



