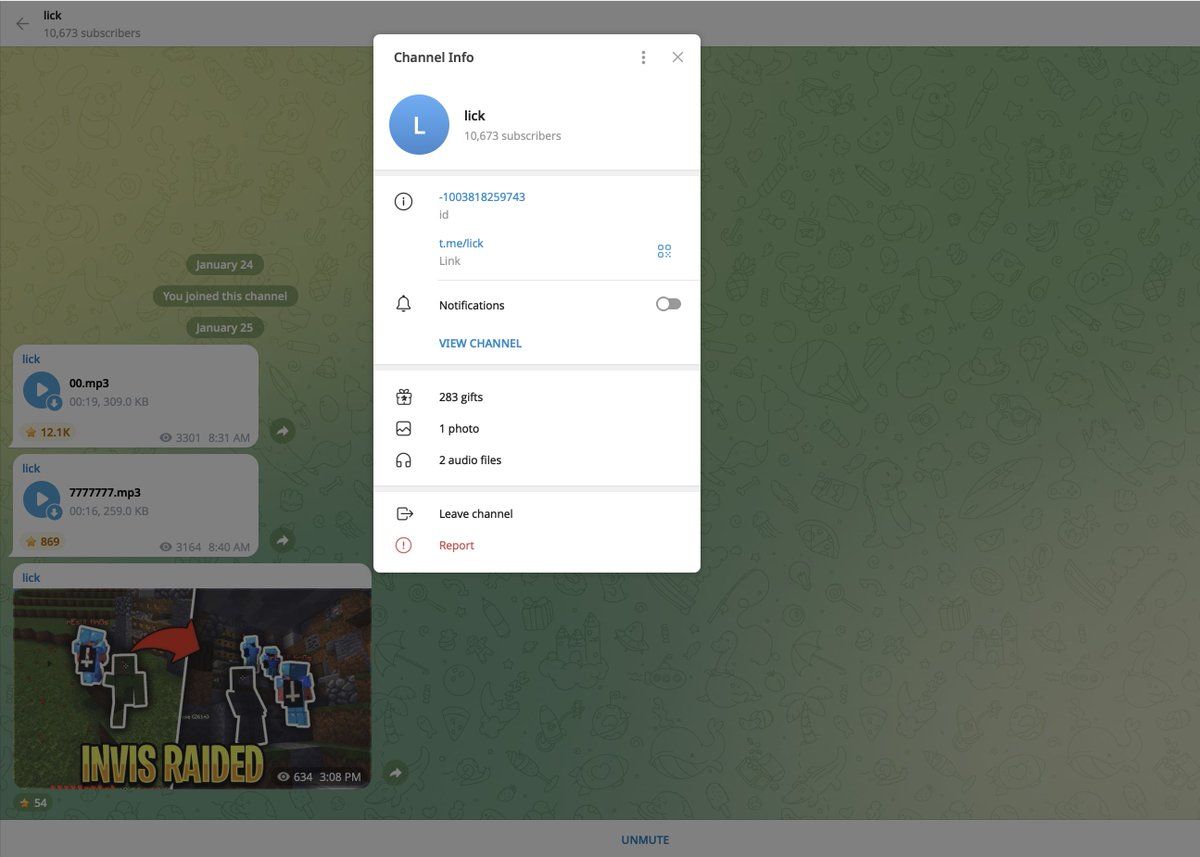
1/ Let’s expose a team of people in the MV Deal Flow telegram
who might actually take the crown for being Shill Team 6.
@spectregrp



who might actually take the crown for being Shill Team 6.
@spectregrp
https://twitter.com/zachxbt/status/1430250147422695426




2/ As per usual I search up the typical pump and dump Master Venture, AU21 Capital, Moonrock Capital portfolios to see what to look out for.
$aioz $pmon $dows $shopx $polk $room $super $cvr $kyl $bles & more shady IDOs.



$aioz $pmon $dows $shopx $polk $room $super $cvr $kyl $bles & more shady IDOs.




3/ First let’s breakdown @Adouble212. He DM’d me after my VC thread claiming he had “no idea” after months & months of IDO shilling.
From his tweets you’d say otherwise…



From his tweets you’d say otherwise…




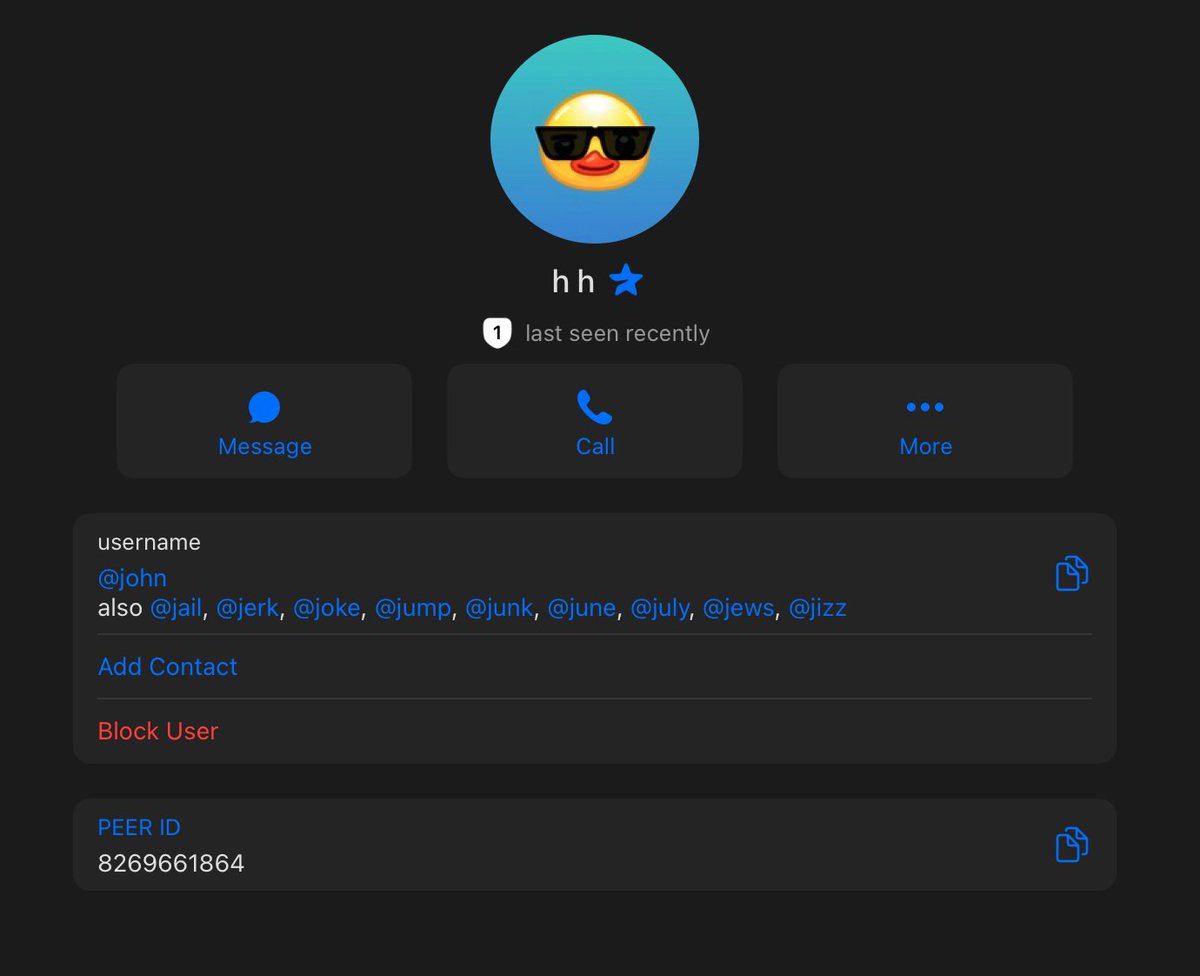
2/ Now let’s look @JohnnyZcash and see if he’s any different.
Nope. Shilling the same trash to newbies.



Nope. Shilling the same trash to newbies.




3/ Someone check on our friend @IAMLLUCIANA. He seems to have deleted all his tweets and forgotten about all of these projects.
Don’t worry bro I found the replies to your deleted tweets for you since you “forgot”.


Don’t worry bro I found the replies to your deleted tweets for you since you “forgot”.



4/ You might respond with “ZachXBT how does this prove he tweeted it”?
Don’t worry I used web.archive.org and here are the Tweets.
Regardless he’ll probably make a 4th account.


Don’t worry I used web.archive.org and here are the Tweets.
Regardless he’ll probably make a 4th account.



5/ It’s clear this is a group of larps that made their money from posing as a research group when in reality they made money from IDO shilling and wrecking anyone who followed them. 

6/ It’s frustrating to see all of them get such engagement and make so much money while the newbies blindly follow.
We see this reoccur time after time again. Adouble212 DM’d me saying they want to change but they’ve already caused so much damage at the expense of others.
We see this reoccur time after time again. Adouble212 DM’d me saying they want to change but they’ve already caused so much damage at the expense of others.

7/ Why would you trust them now? The least they could have tried to do is reimburse the victims if they’re “truly sorry”.
Case closed.
Case closed.
Correcting AU21 Capital. Apologies for including you with the other names. X21 Capital is who I should’ve put instead.
• • •
Missing some Tweet in this thread? You can try to
force a refresh