1/ Time for a thread on CryptoGodJohn & his paid group Walsh Wealth Group (WWG).
By the end you will see all the shady tactics they’ve employed and how they’re no different from the rest.
Many on CT turn a blind eye on CT since they’re “friends”

By the end you will see all the shady tactics they’ve employed and how they’re no different from the rest.
Many on CT turn a blind eye on CT since they’re “friends”


2/ First let’s start with John. At first he just appears like your typical influencer. Let’s examine his alleged BSC wallet:
SuperWaifu:
a) Bought at 6:31 PM UTC
b) Shilled on Twitter at 6:39 UTC
c) Sold entire stack a few hours after
bscscan.com/token/0x626dec…

SuperWaifu:
a) Bought at 6:31 PM UTC
b) Shilled on Twitter at 6:39 UTC
c) Sold entire stack a few hours after
bscscan.com/token/0x626dec…


3/ Perhaps you thought it was a one time off incident and I am making assumptions that it’s his wallet. Let’s examine some undisclosed $EULER shilling.
a) Received 78,610 EULER on 5/3
b) Shilled on Twitter on 5/4

a) Received 78,610 EULER on 5/3
b) Shilled on Twitter on 5/4


4/ Let’s look at $SAVE which which was a BSC coin advertised as a “charity coin”
From BSC scan you see he received coins for promoting which wasn’t disclosed.
He sold $350k worth all while tweeting about it.
Later he tried to pull the sympathy card.
bscscan.com/token/0x159802…



From BSC scan you see he received coins for promoting which wasn’t disclosed.
He sold $350k worth all while tweeting about it.
Later he tried to pull the sympathy card.
bscscan.com/token/0x159802…




5/ Let’s examine two more IDO shills if you’re not convinced $BOSON & $STAK.
These were shilled most frequent by him. He never disclosed his vested interest in either project.
Here’s stolen TA as well:




These were shilled most frequent by him. He never disclosed his vested interest in either project.
Here’s stolen TA as well:
https://twitter.com/charles02411212/status/1434610501120577542?s=21




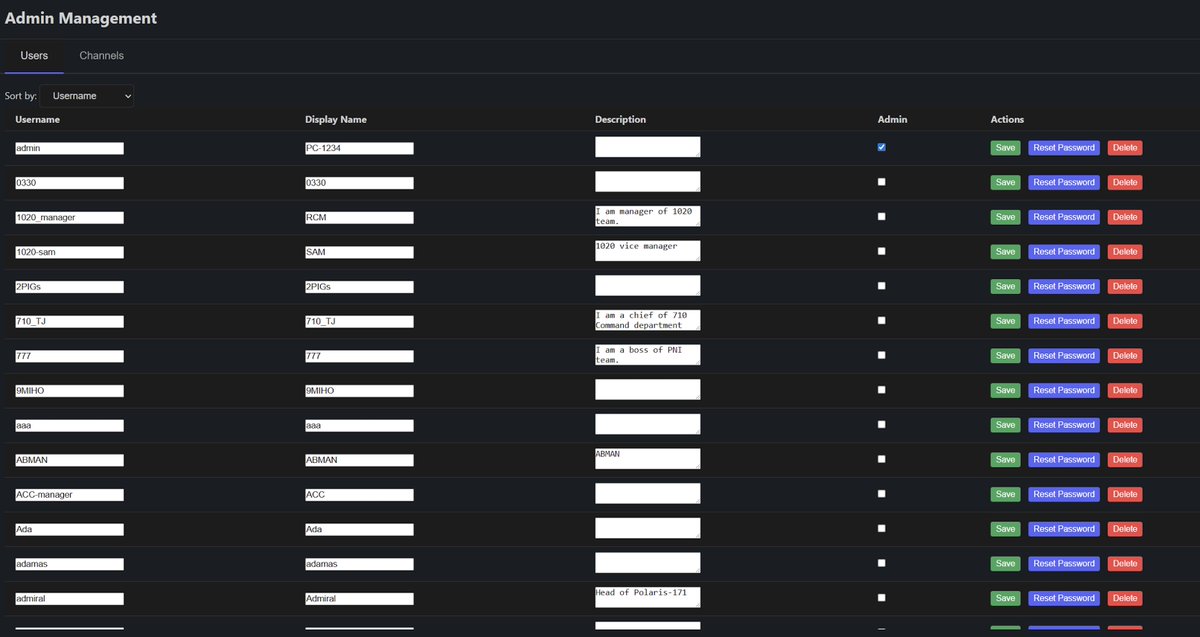
6/ Now let’s move over to his paid group WWG so we can examine if it’s any different.
They have thousands of paying members with a monthly membership fee of ~$175
I would hope you’re not taking advantage of people with your “signals”

They have thousands of paying members with a monthly membership fee of ~$175
I would hope you’re not taking advantage of people with your “signals”


7/ Let’s examine this TRB signal by CryptoEliz.
a) Call made at 11:28 pm
b) Exits 3 minutes later & posts screenshot
c) Significant volume & price surge immediately after the signal from 11:28 pm to 11:31 pm
Perhaps this was a one off incident!


a) Call made at 11:28 pm
b) Exits 3 minutes later & posts screenshot
c) Significant volume & price surge immediately after the signal from 11:28 pm to 11:31 pm
Perhaps this was a one off incident!



8/ Here’s another TRB call made by CryptoEliz
a) Entry signal made at 3:04 pm
b) Exits 5 minutes later and posts screenshot
c) Significant volume & price surge immediately after the signal from 3:04 pm to 3:09 pm
Not so much of a coincidence now anon?


a) Entry signal made at 3:04 pm
b) Exits 5 minutes later and posts screenshot
c) Significant volume & price surge immediately after the signal from 3:04 pm to 3:09 pm
Not so much of a coincidence now anon?



9/ Let’s look at one more for good measure. Here’s a LIT signal given.
a) Entry signal made at 11:32 am
b) Exits for a “scalp” 8 minutes later
c) See chart for evidence.
Imagine paying this much monthly just to get dumped on.


a) Entry signal made at 11:32 am
b) Exits for a “scalp” 8 minutes later
c) See chart for evidence.
Imagine paying this much monthly just to get dumped on.



10/ Lastly here’s the WWG analyst BullChain calling out anyone promoting the token $LEGS
Hours later CryptoEliZ tweets about $LEGS pretending to have genuine interest. Another shill not disclosed…
Another WWG fail

Hours later CryptoEliZ tweets about $LEGS pretending to have genuine interest. Another shill not disclosed…
Another WWG fail


11/ Another sketchy tactic used by the group is their marketing & branding.
By using wealth/warren buffet memes they look to attract as many newbies as possible.
Avoid anyone with “god” in their username.

By using wealth/warren buffet memes they look to attract as many newbies as possible.
Avoid anyone with “god” in their username.


12/ For a while during spring when it was up only I did follow him for a bit thinking he was legit but little did I know.
These people do not want to help you and are not your friend.
I’m sure his army will come attacking but they are naive and it’s hard to continue to watch

These people do not want to help you and are not your friend.
I’m sure his army will come attacking but they are naive and it’s hard to continue to watch


@SECGov @GaryGensler @FBI Instead of going after legit projects trying to innovate when can we go after bad actors like the ones displayed in this thread that investors keep getting wrecked by.
This is where protection should be given.
This is where protection should be given.
I’m not too well versed in this area but everyone involved is under US jurisdiction.
Would be happy to formally file a complaint or take legal action granted someone can help guide through the process.
Most of CT will forget within the next 24 hrs.
Would be happy to formally file a complaint or take legal action granted someone can help guide through the process.
Most of CT will forget within the next 24 hrs.
• • •
Missing some Tweet in this thread? You can try to
force a refresh