
This article contains DFIR techniques I've used IRL, in investigations where the event logs can't be used.
The real hard work has been done by the articles' referenced tool creators and educators
@davisrichardg / @13CubedDFIR
@scudette / @velocidex
@EricRZimmerman
🧵
1/6
The real hard work has been done by the articles' referenced tool creators and educators
@davisrichardg / @13CubedDFIR
@scudette / @velocidex
@EricRZimmerman
🧵
1/6
https://twitter.com/JumpsecLabs/status/1462705713935958021
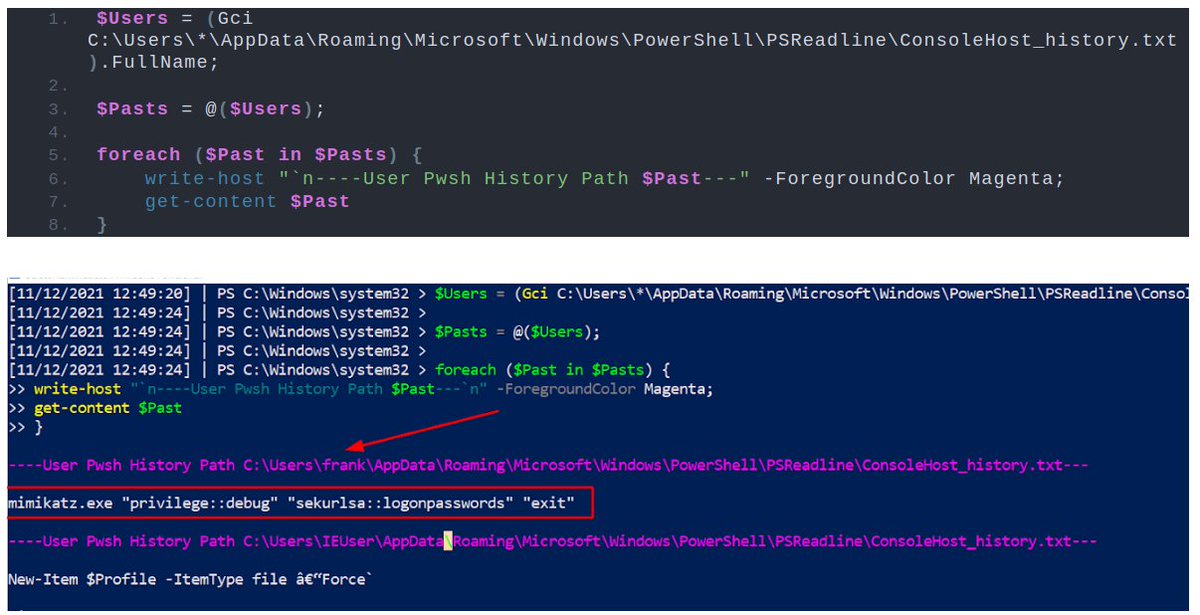
The first technique in the article discusses how to retrieve the PowerShell history for every user account via the 'ConsoleHost_History file' (typically enabled on Windows 10 endpoints)
2/6
2/6
The second leverages @EricRZimmerman's PECmd tool to examine Prefetch, an application caching system that we can use to evidence execution
3/6
3/6

The third technique levearges another @EricRZimmerman tool to parse Shimcache, originally designed to look for interoperability issues between Win versions and applications
4/6
4/6

The fourth technique leverages @velocidex / @scudette's Velociraptor tool to take an archeological dive into the USN Journal, which tracks changes to files and diretcories and more
5/6
5/6

@davisrichardg / @13CubedDFIR's videos were incredibly insightful when drafting this article, as they helped me concisely explain the mechanics behind these DFIR techniques.
youtube.com/c/13cubed/feat…
6/6
youtube.com/c/13cubed/feat…
6/6
• • •
Missing some Tweet in this thread? You can try to
force a refresh



