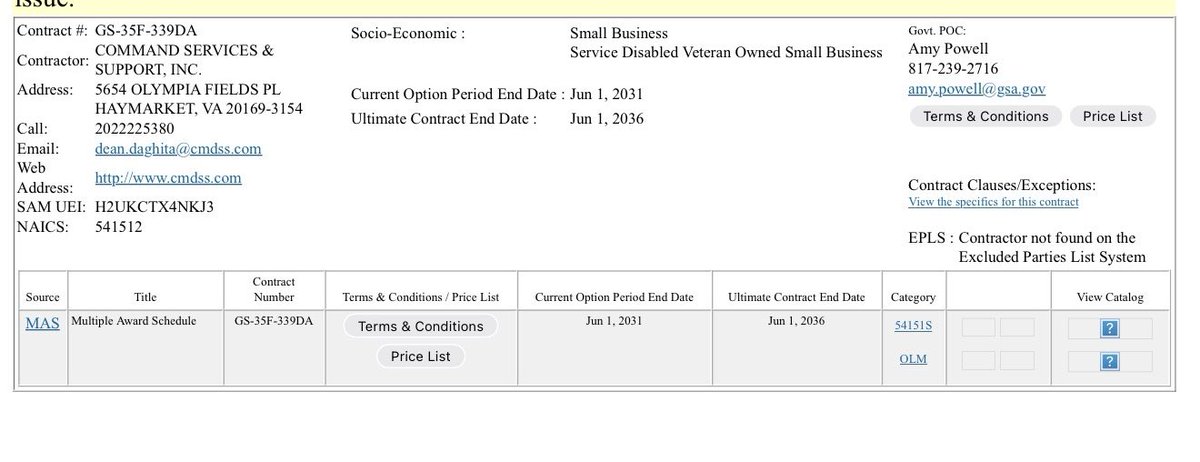
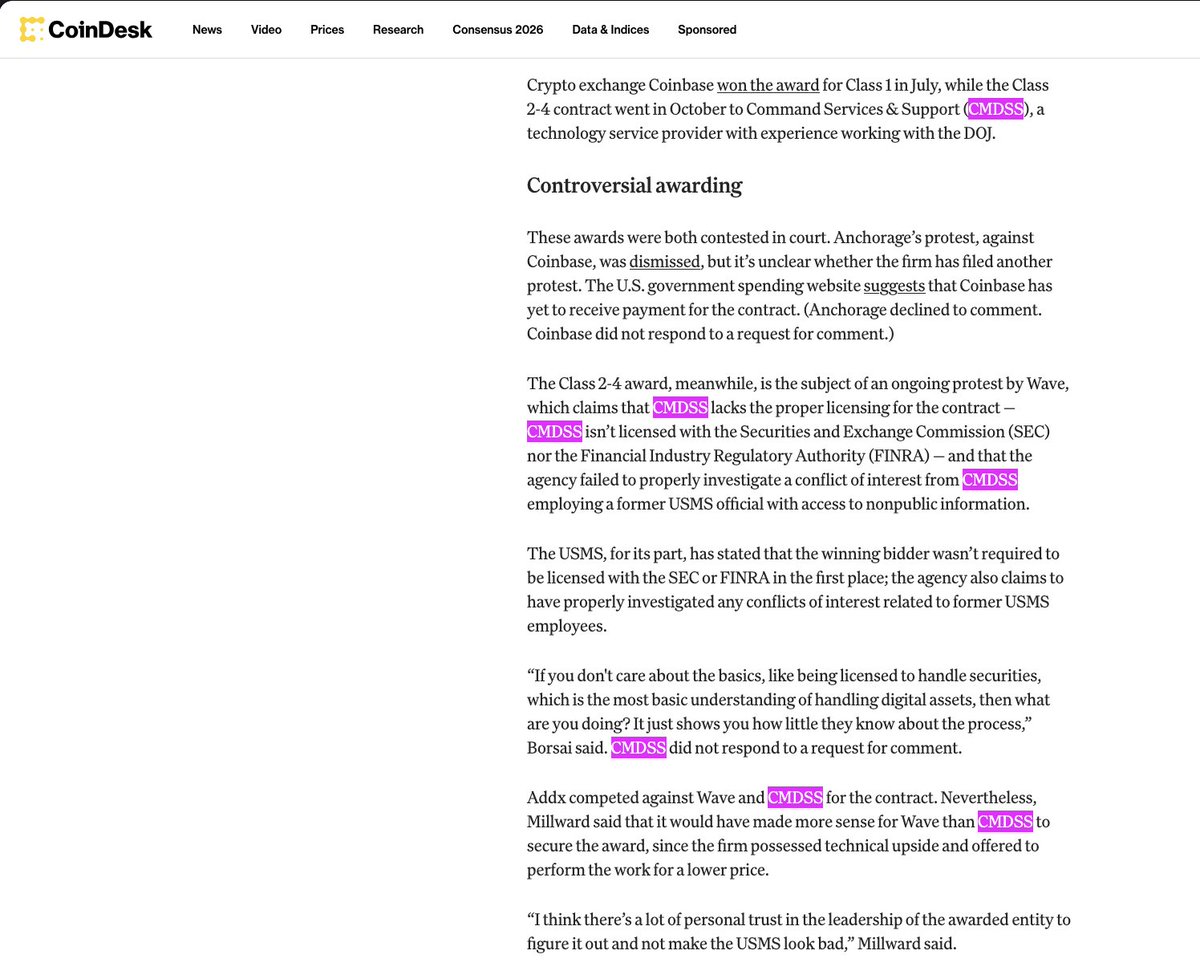
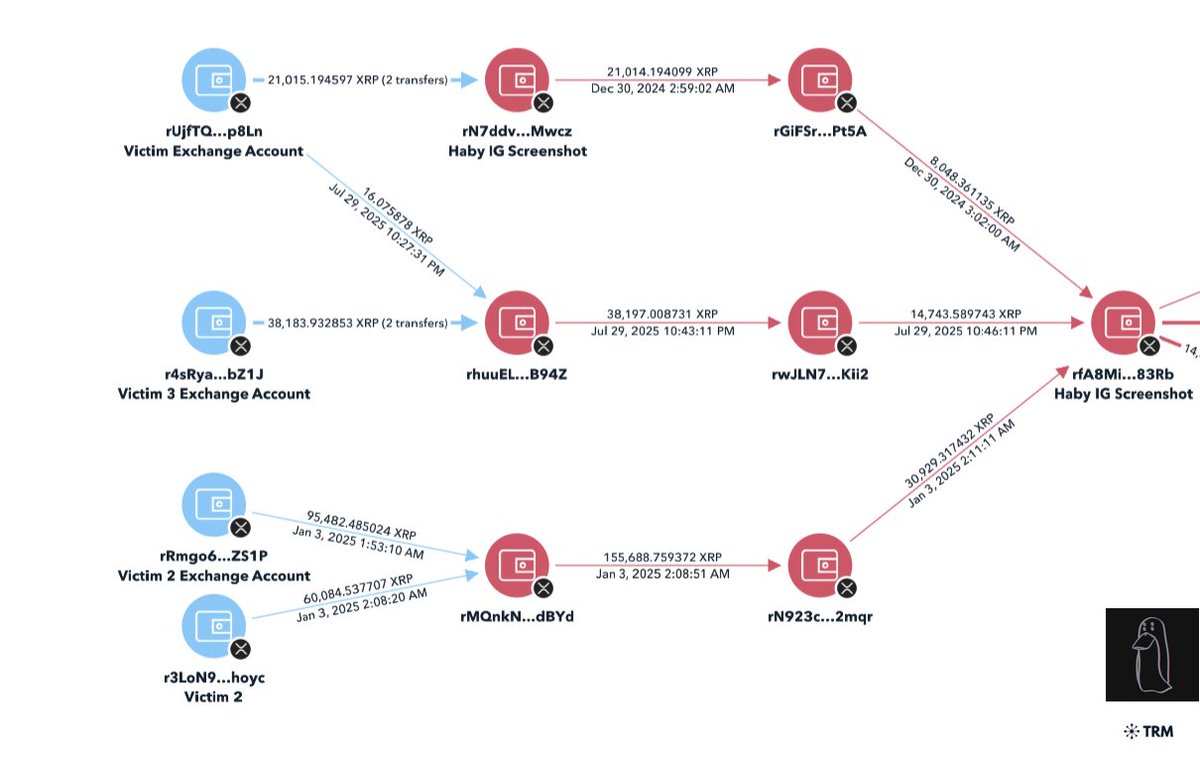
1/ One of the lesser known figures in the space is Darkpool Liquidity a market maker (MM)
After reviewing the pitch deck there were a number of services that are straight market manipulation and not standard at ALL by MMs in the space
They play a role in a lot of the cash grabs
After reviewing the pitch deck there were a number of services that are straight market manipulation and not standard at ALL by MMs in the space
They play a role in a lot of the cash grabs

2/ To summarize the pic above:
-offers washtrading to artifically boost volume
-frontrunning and selling assets w/o affecting the market price
-spoofing
Well the next question is who even uses this MM?
-offers washtrading to artifically boost volume
-frontrunning and selling assets w/o affecting the market price
-spoofing
Well the next question is who even uses this MM?
3/ Well mostly Polkastarter projects use this MM as well as a number of other launchpads on here
One thing a lot of these projects have in common is large unlocks at TGE, vesting for 6 months or less, & a huge % of token supply to the seed/private round & advisors (20-30%+)
One thing a lot of these projects have in common is large unlocks at TGE, vesting for 6 months or less, & a huge % of token supply to the seed/private round & advisors (20-30%+)

4/ After speaking with a few people well versed in the MM space they said it was very surprising this verbiage would be used so openly in a pitch deck
The rest seems to be almost copied from some where since it’s very generic
The rest seems to be almost copied from some where since it’s very generic
5/If you have done 50+ projects you more than likely should have $5m+ in AUM
Unless you’re not the main MM or just are a bad negotiator
Unless you’re not the main MM or just are a bad negotiator

6/ It is pretty clear what is being done here… please stay folks and do proper DD before putting your $$$ into projects
Website:
darkpool.ventures
Rest of deck (left out contact info slide for privacy):
Website:
darkpool.ventures
Rest of deck (left out contact info slide for privacy):

Our buddy from Moonrock sure seems satisfied… I wonder why that might that be?

https://twitter.com/zachxbt/status/1410356530956980226?s=21

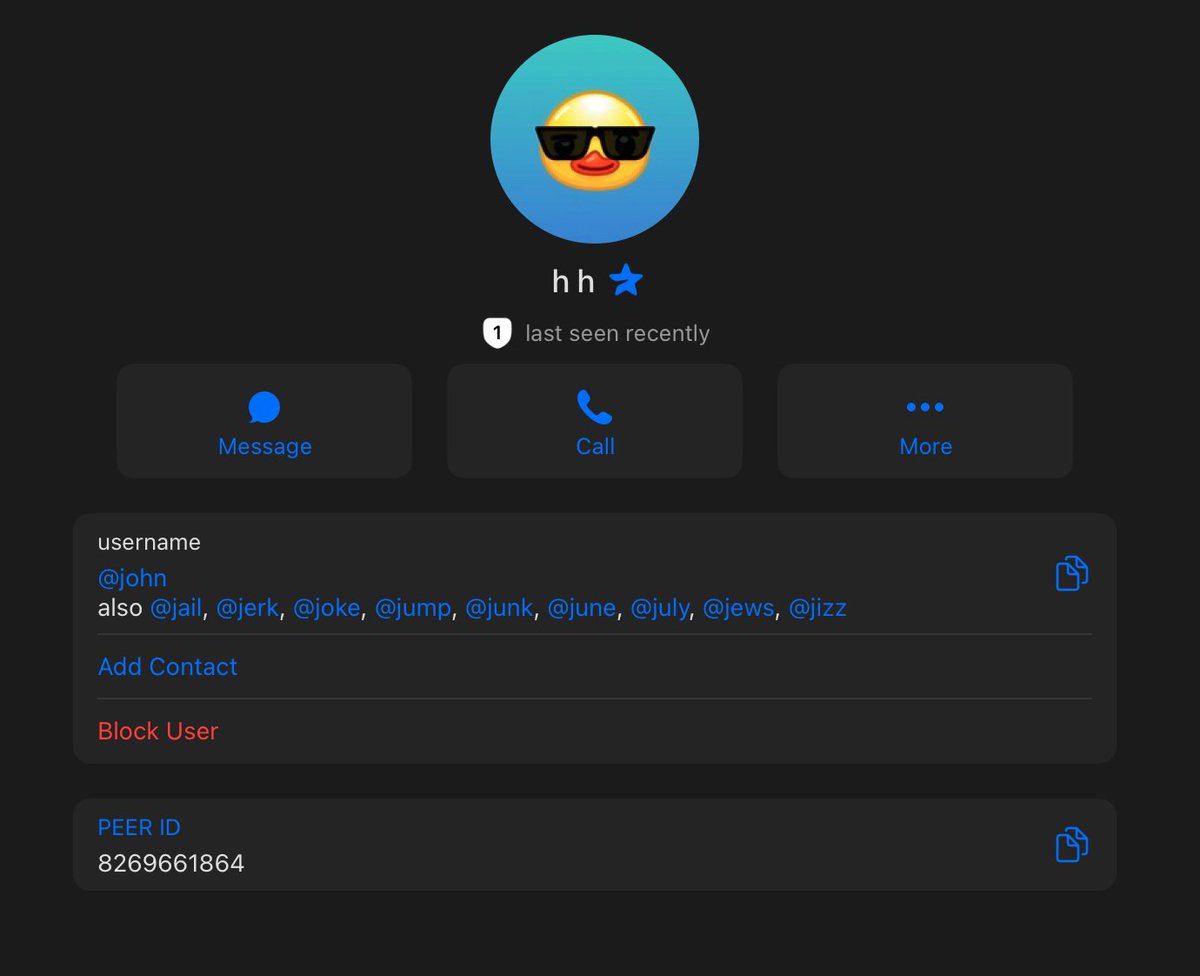
They deleted a bunch of slides and try to claim it’s old. When multiple slides talk about 2021 projects lmao
https://twitter.com/DarkpoolMM/status/1465366827354234880
• • •
Missing some Tweet in this thread? You can try to
force a refresh