Ha! This DNSSEC Internet Draft thanks me by name. datatracker.ietf.org/doc/html/draft…
This is the funniest fucking thing.
Back in the late 1990s when I was writing the OpenBSD security advisories, I used to include a line that said “The OpenBSD Project would like to thank Perry Metzger for his steadfast support of our work”, until he threatened to sue me.
I wonder if DNSSEC people think shout-outs like this are going to make me grumpy; what they really make is my whole day. 🥳
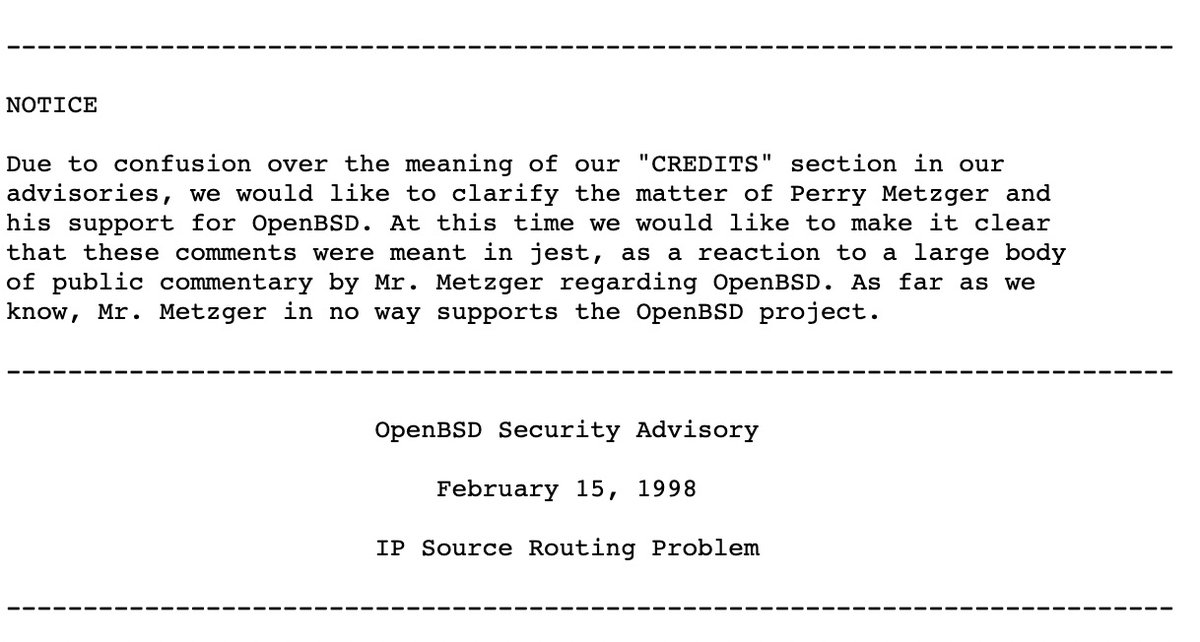
I think the legal threat came after the mmap vulnerability advisory; Metzger sent me an email about how I was poking some kind of bear by thanking him in our advisories, and so our next advisory included: 

• • •
Missing some Tweet in this thread? You can try to
force a refresh