2/ Suppoman is a crypto YouTuber who has been in the space since 2017.
In that period he has promoted many projects undisclosed stemming everywhere from rugs to ponzi’s to cash grabs.
TMG did a YT series on him in 2018.

In that period he has promoted many projects undisclosed stemming everywhere from rugs to ponzi’s to cash grabs.
TMG did a YT series on him in 2018.

3/ TLDR on Bluezilla:
>”incubates” copy paste launchpads & Uni v2 forks on every chain.
>projects never list the team, tokenomics, and other basic docs
>tokenomics have very short vesting periods (hence why they don’t display it)
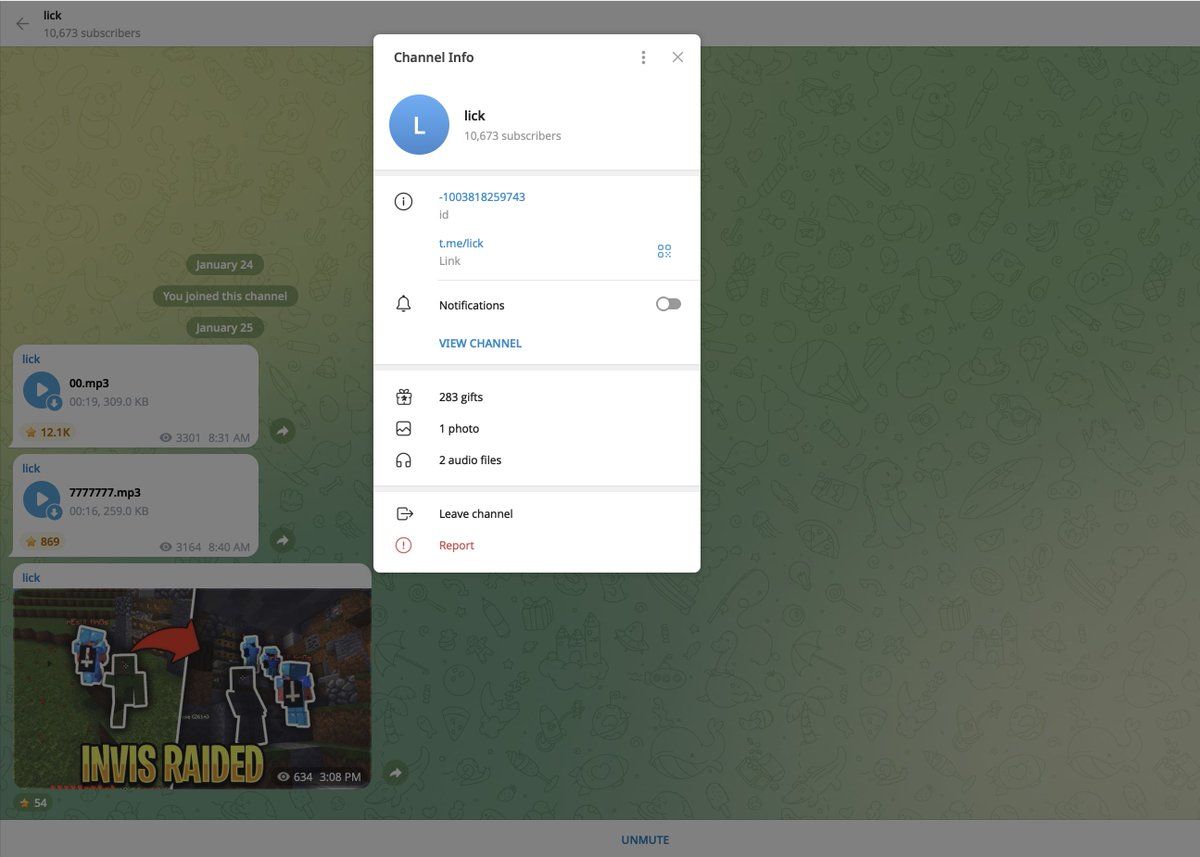
>always promoted heavily through Suppoman


>”incubates” copy paste launchpads & Uni v2 forks on every chain.
>projects never list the team, tokenomics, and other basic docs
>tokenomics have very short vesting periods (hence why they don’t display it)
>always promoted heavily through Suppoman



4/ $BSCPAD - Not displayed on their website but 4 months total of vesting for private rounds. Why even have vesting then? 





14/ I could keep going but I think my point has been made.
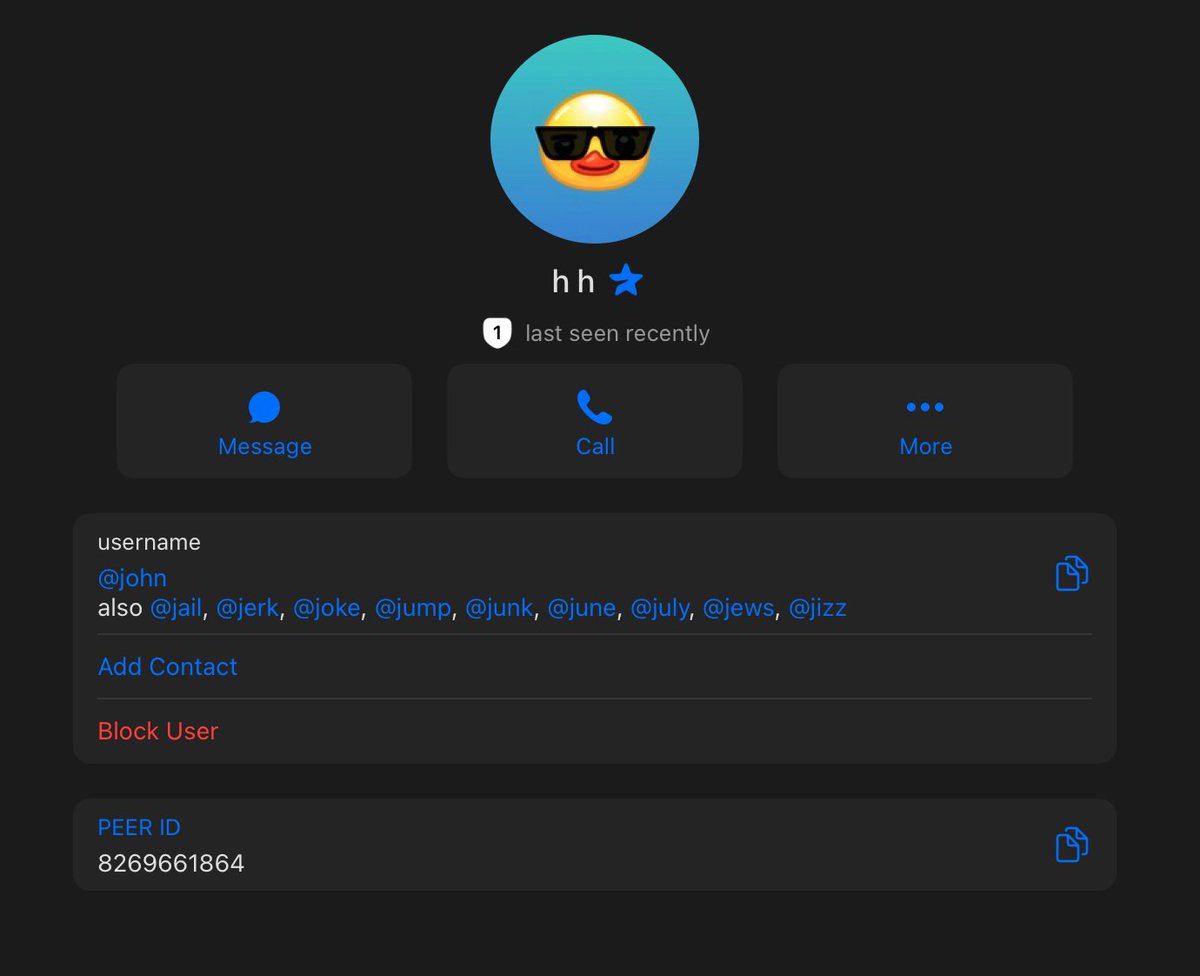
>Suppoman gets private sale allocations to shill undisclosed scams to his audience
>Bluezilla’s scheme is to keep copy and pasting launchpads to pump and dump on them for $$$
>Suppoman gets private sale allocations to shill undisclosed scams to his audience
>Bluezilla’s scheme is to keep copy and pasting launchpads to pump and dump on them for $$$
15/ I would advise you avoid anything with Bluezilla’s name on it.
Search “Bluezilla scam” on Twitter to see all the people who have been rekt.
Search “Bluezilla scam” on Twitter to see all the people who have been rekt.
• • •
Missing some Tweet in this thread? You can try to
force a refresh