1/ Here is a thread on @Helloimmorgan a NFT influencer and how she has consistently deceived her audience. 

2/ Yesterday she caught some heat after promoting a scam undisclosed.

https://twitter.com/helloimmorgan/status/1493427443767693320

3/ I would accept the apology except she previously DENIED she was paid at all to @fauxcondor . This anon also tried to warn her with proof it was most likely going to end poorly yet she did not listen.
Was paid out 4.7 eth in total.



Was paid out 4.7 eth in total.




4/ Morgan claims this was the first time she was paid for a project. I will observe if that’s the case. 

5/ Here is an example with the project Women of crypto where Morgan received 10 free NFTs in exchange for hosting a giveaway.
She proceeded to dump 8 of these right away for ETH.



She proceeded to dump 8 of these right away for ETH.




6/ As she is a US based influencer here are the FTC influencer guidelines:
Seems pretty clear cut to me.
Seems pretty clear cut to me.

7/ Here’s her doing another giveaway for Squiggles. She claims the community asked for it yet if you use Twitter search there are zero requests for it
“(to:helloimmorgan) until:2022-02-03 squiggles”
Squiggles caught heat on Twitter before mint so she cut ties it seems



“(to:helloimmorgan) until:2022-02-03 squiggles”
Squiggles caught heat on Twitter before mint so she cut ties it seems




8/ Here’s some other giveaways that have been hosted.
Newsflash hosting a giveaway for a whitelist spot is still compensation.



Newsflash hosting a giveaway for a whitelist spot is still compensation.




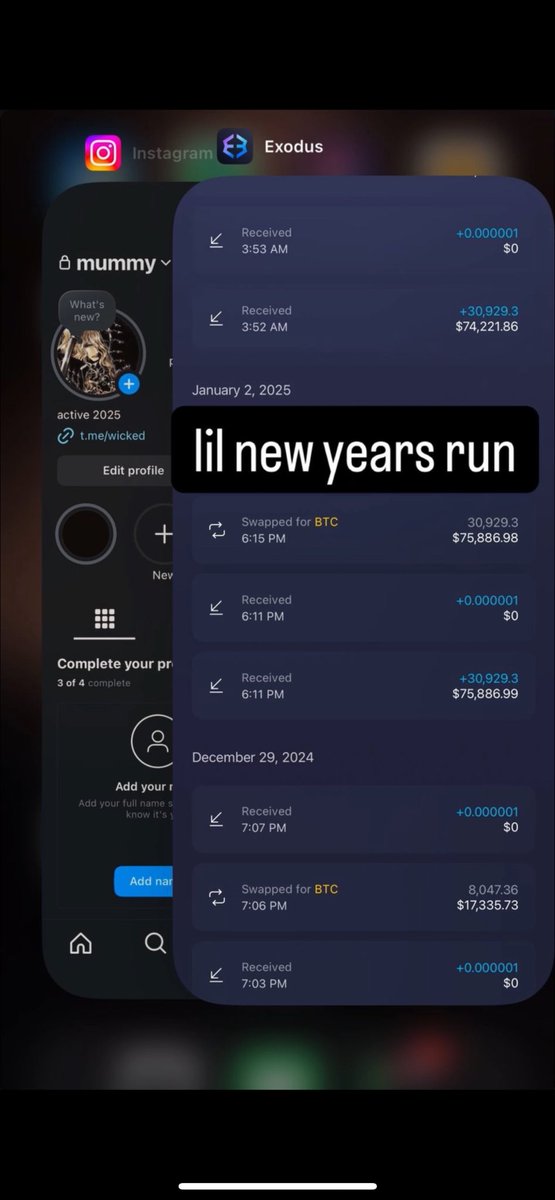
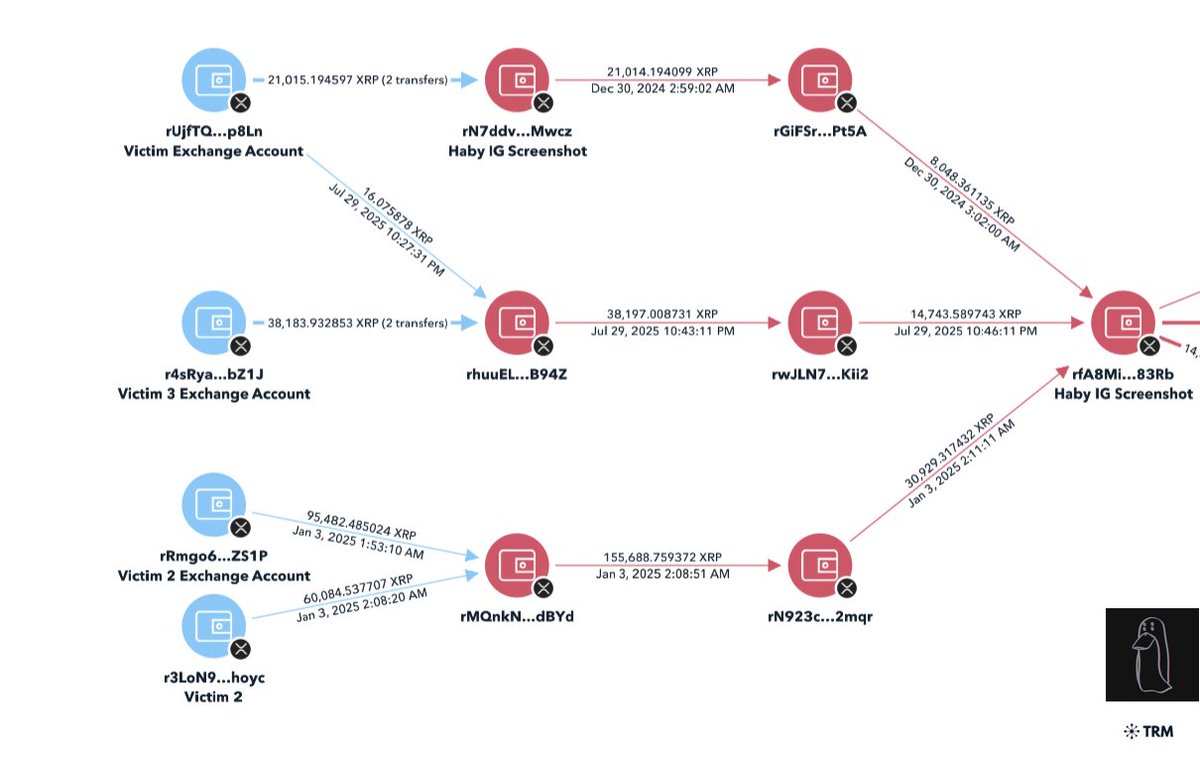
9/ Back in the fall of 2021 there were questionable wallet transactions conducted during a fundraiser for her Grandma.
https://twitter.com/Guruleaks1/status/1459618485277970434
10/ For a different charity project she suddenly decided to cut the % donated in half after it was live. 



11/ Here we have some clear engagement baiting. This combined with the giveaways seems to be the strategy of gaining a following. 



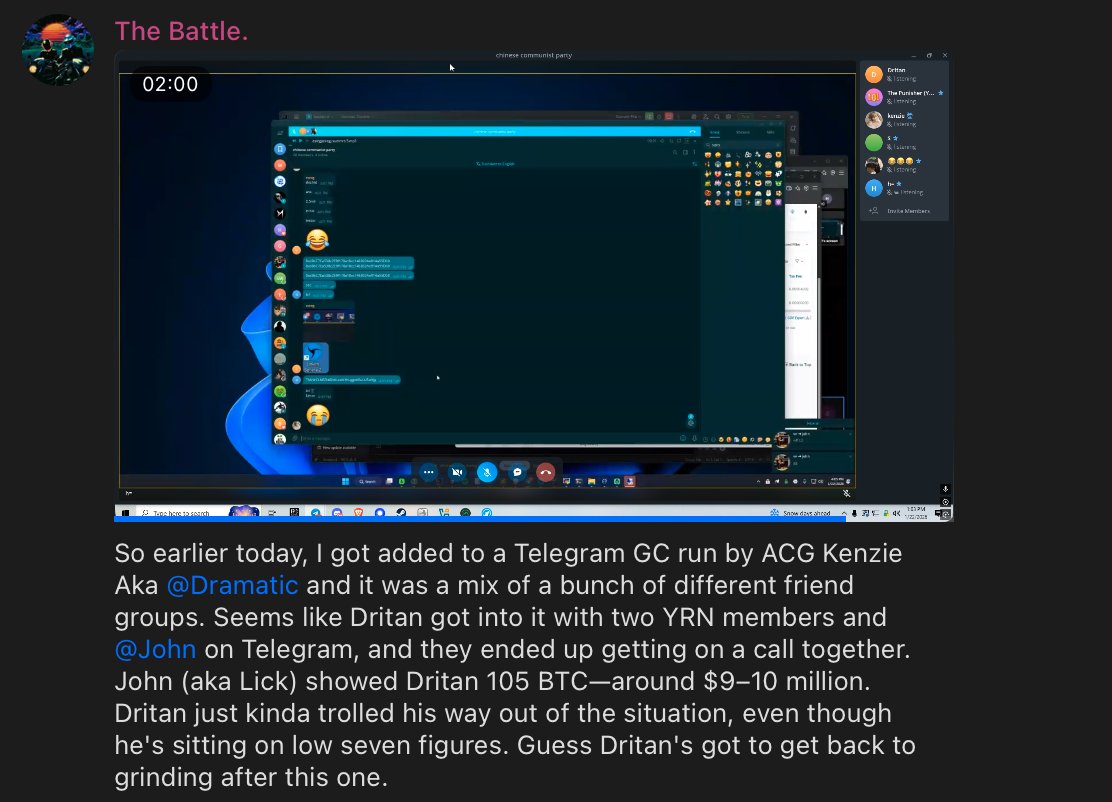
12/ I don’t like how she shifts the blame to others and is not holding any accountability for her actions. There is a clear lapse of judgement going on.
This is a reoccurring theme with influencers.
This is a reoccurring theme with influencers.

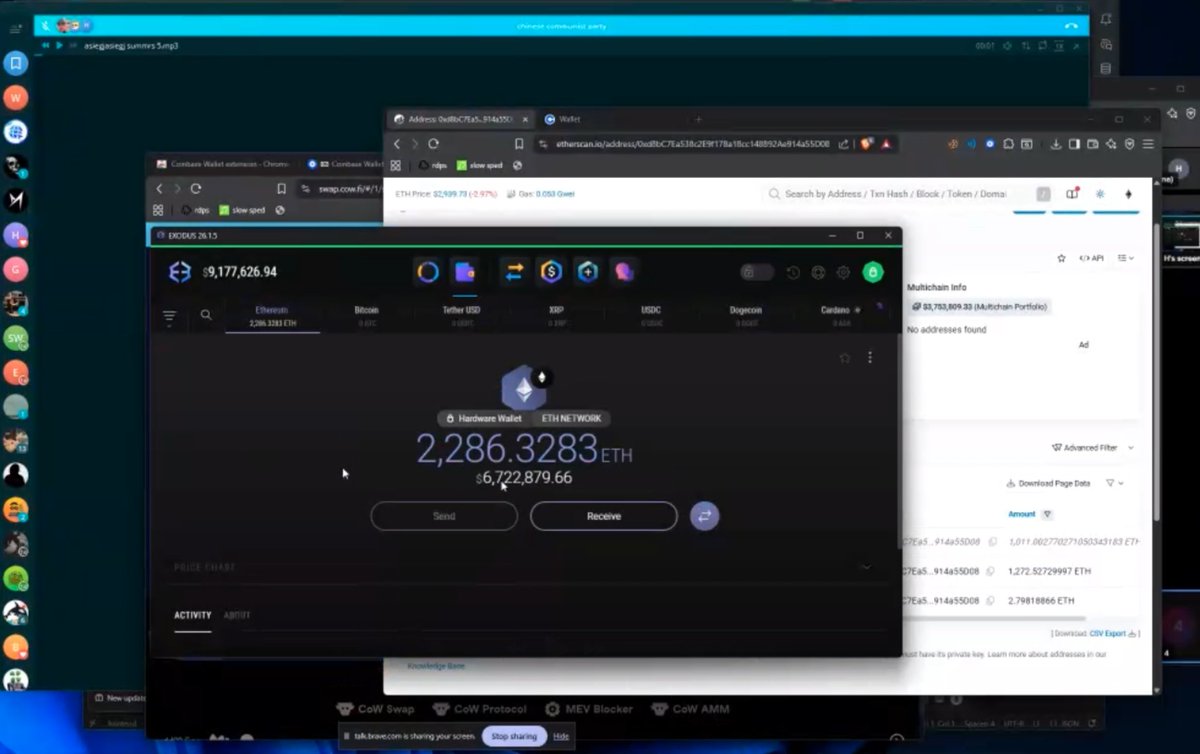
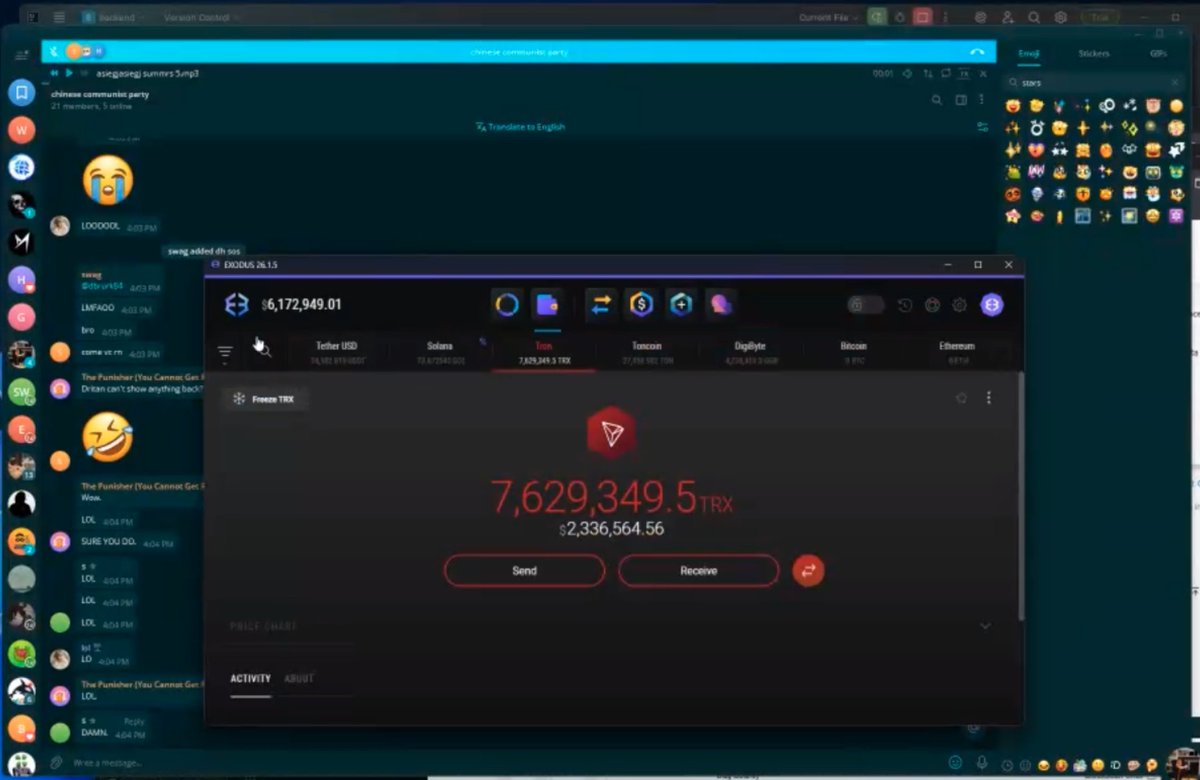
As per usual everything was gathered using Twitter search & her public ENS
etherscan.io/address/0x0ab6…
etherscan.io/address/0x0ab6…
Calls it “mob mentality” no it’s accountability for your actions. Otherwise it’s the FTC fining you. 

More details have emerged about the Grandma cash grab.
https://twitter.com/suchhodl/status/1493630128479428612
Lastly to close off this thread here is Morgan’s response.
https://twitter.com/helloimmorgan/status/1493722115580833801
• • •
Missing some Tweet in this thread? You can try to
force a refresh