1/ Examining @1goonrich and how he pumped and dumped lowcap scams on his audience to profit millions.
Luckily tons of evidence exists on-chain so let’s dive in.
Luckily tons of evidence exists on-chain so let’s dive in.

2/ On 12/21/21 Messiah posted about the MAYC he owns.
a) purchased by 0x78 on 12/16/21 for 7.39 eth
b)wallet was funded by 0x8e earlier that day
c)0x78 routinely received inflows from 0x8e (confirming it’s his main wallet)
d)0x78 transaction history:
etherscan.io/txs?a=0x78587A…


a) purchased by 0x78 on 12/16/21 for 7.39 eth
b)wallet was funded by 0x8e earlier that day
c)0x78 routinely received inflows from 0x8e (confirming it’s his main wallet)
d)0x78 transaction history:
etherscan.io/txs?a=0x78587A…



3/ Now that we see 0x8e is Messiah’s address let’s check out the transactions on BSC.
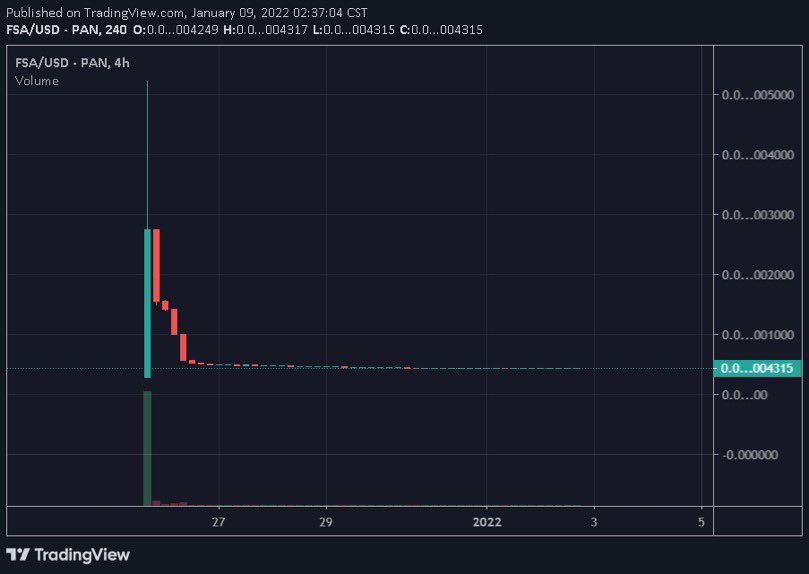
SCIN (sells into follower pump)
bscscan.com/token/0x74aaf1…


SCIN (sells into follower pump)
bscscan.com/token/0x74aaf1…



7/ I could keep going with examples but I think my point has been made. A quick look at his feed will show you all the meme coins.
What I wanted to determine next was how much personal risk he was taking on these coins.
What I wanted to determine next was how much personal risk he was taking on these coins.
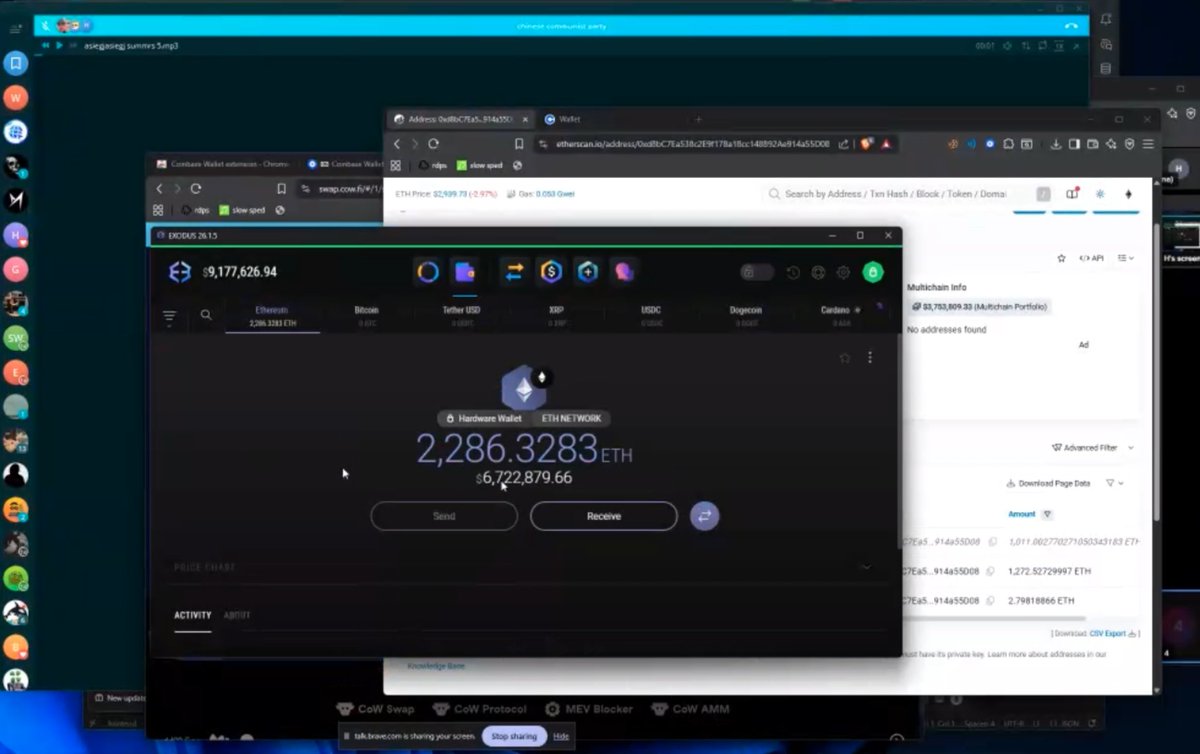
8/ From looking through the transaction history of 0x8c and 0x78 (he has more related wallets as well) there seems to be a mix of:
>Presale allocations
>DEX trades
Okay but how does he find these coins?
>Presale allocations
>DEX trades
Okay but how does he find these coins?
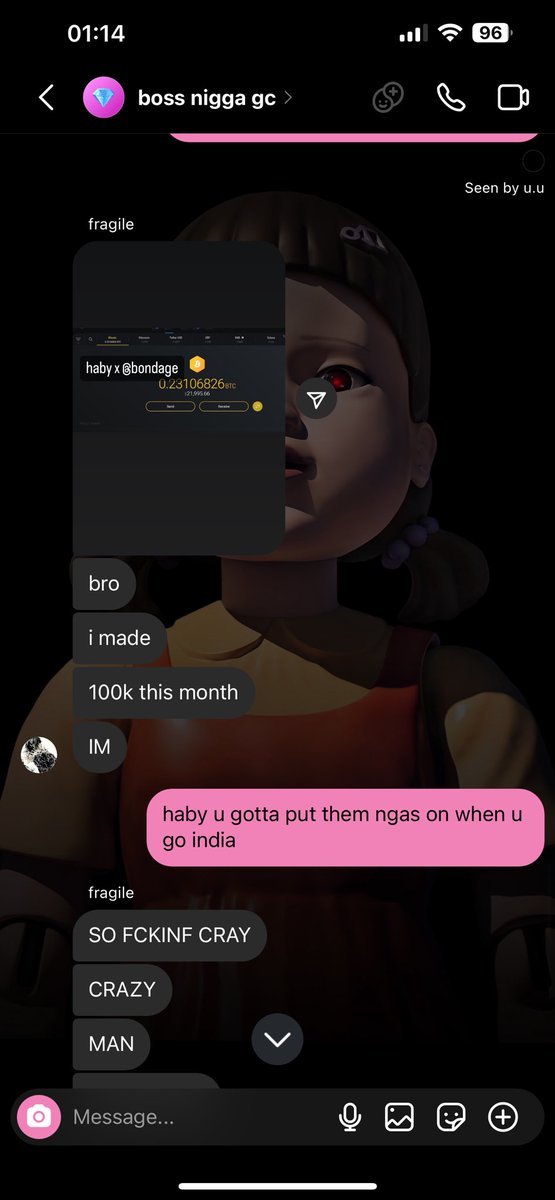
9/ I reached out to a few meme coin traders and they shared Messiah is indeed compensated to Tweet ($4k) about coins (Messiah never has disclosed once) 



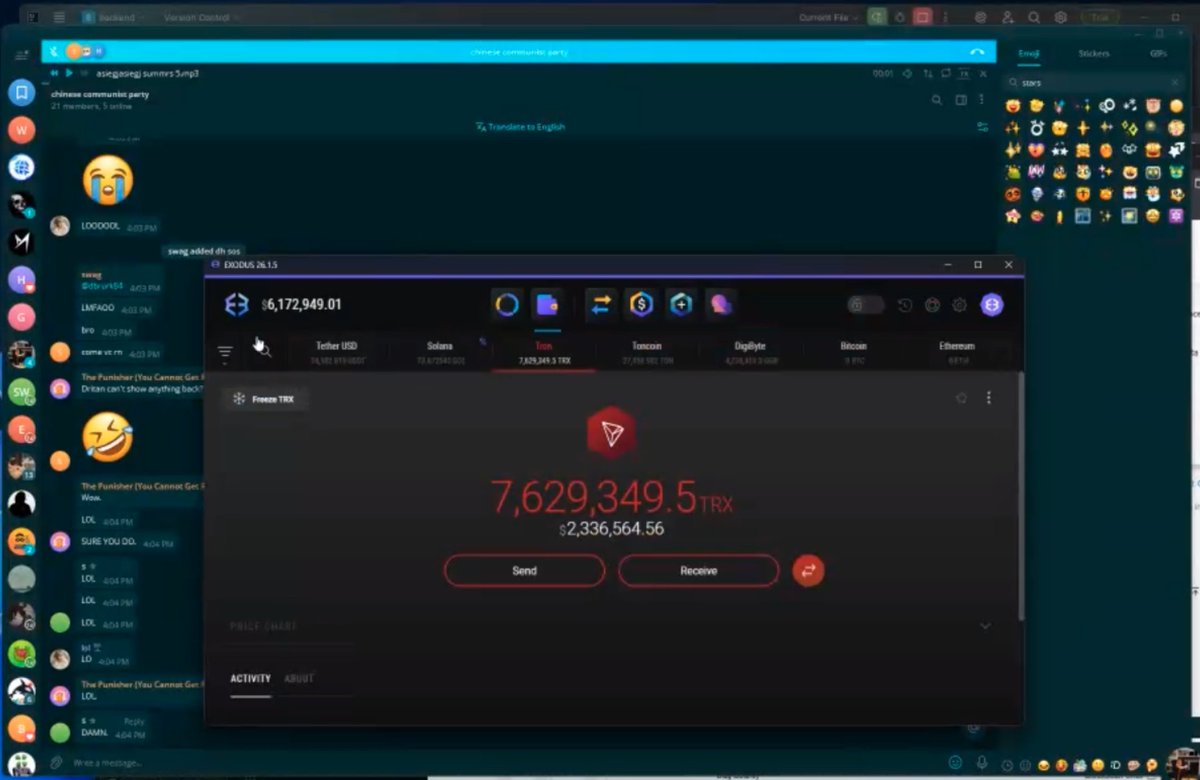
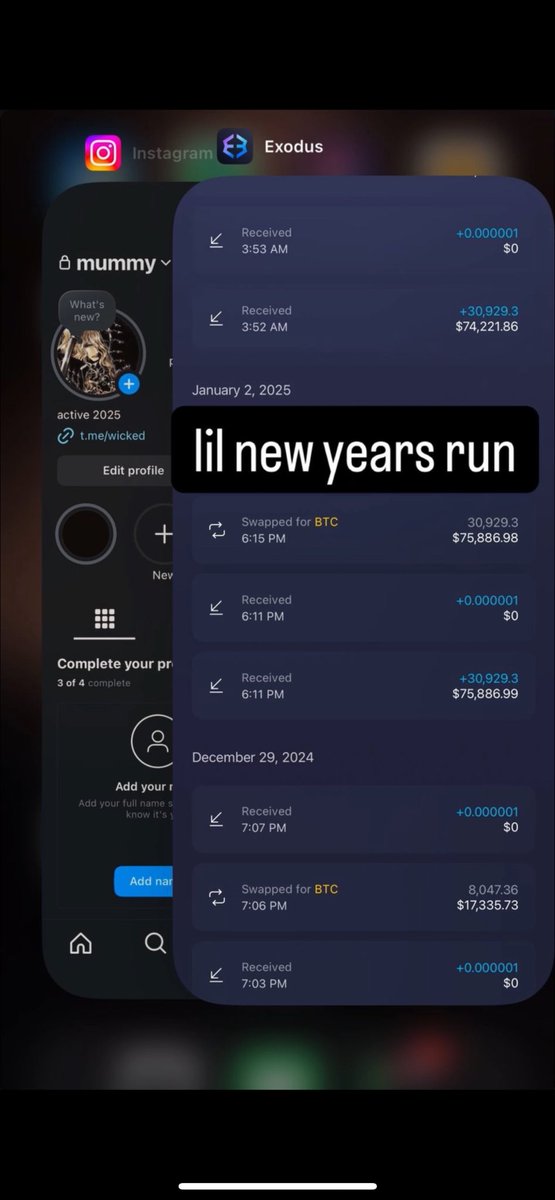
10/ Okay now that we know he’s paid to tweet about these meme coin tokens and there is almost ZERO risk taken on his side
>receives money to promote
>uses to buy early or in presale
>pockets rest
>receives money to promote
>uses to buy early or in presale
>pockets rest
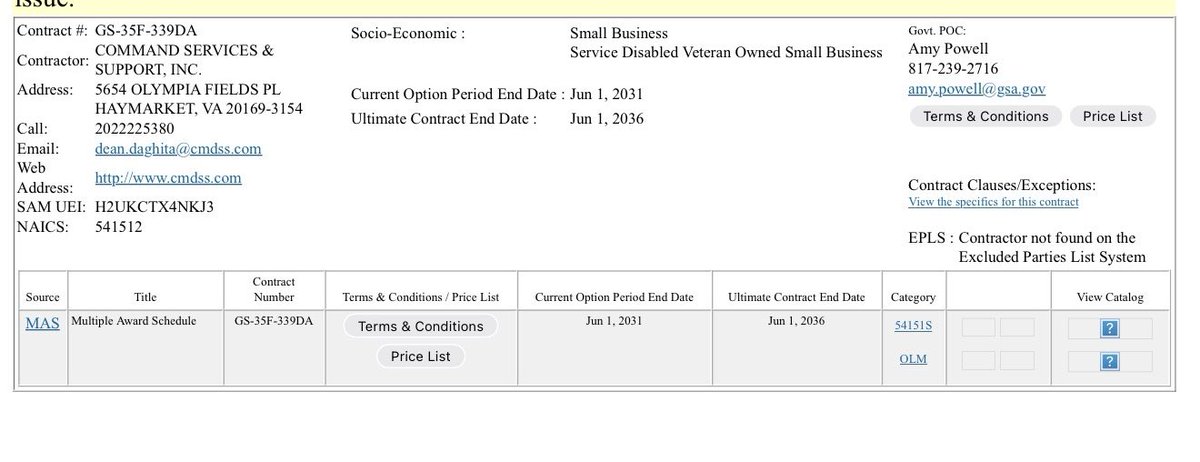
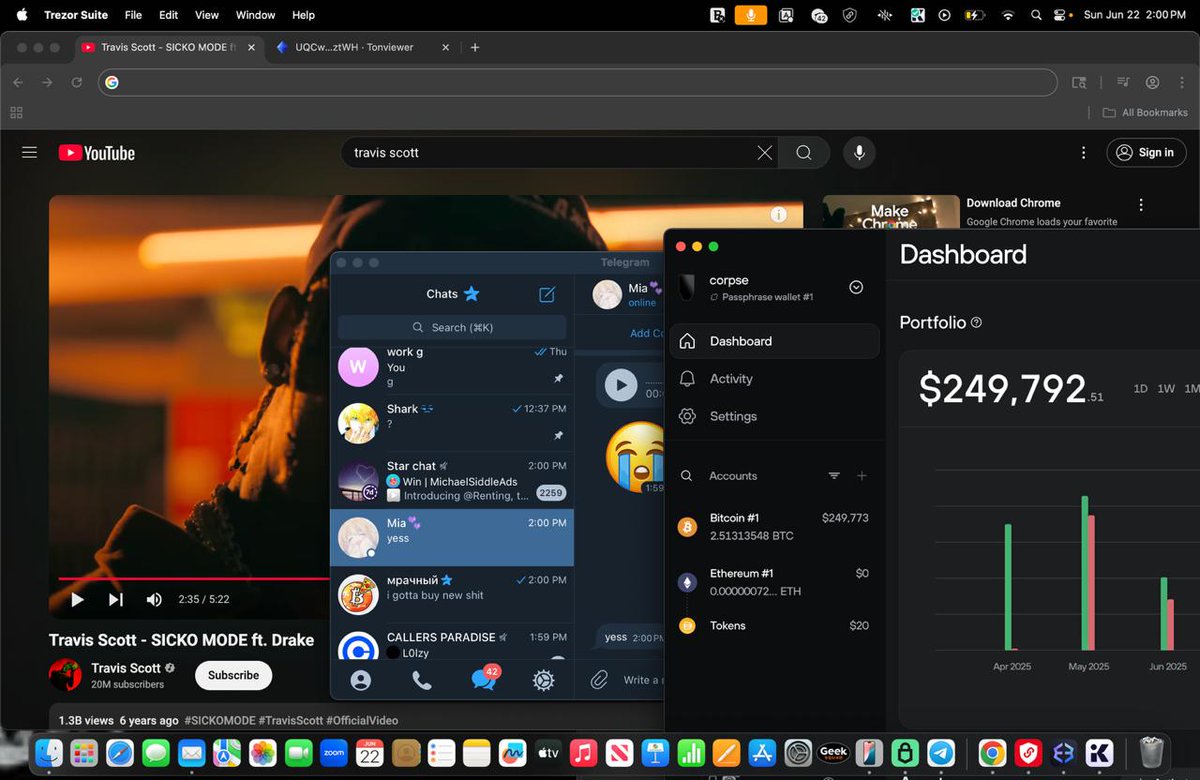
12/ It seems he has the constant need to flex as well. From a video posted it appears he’s located in the US. 







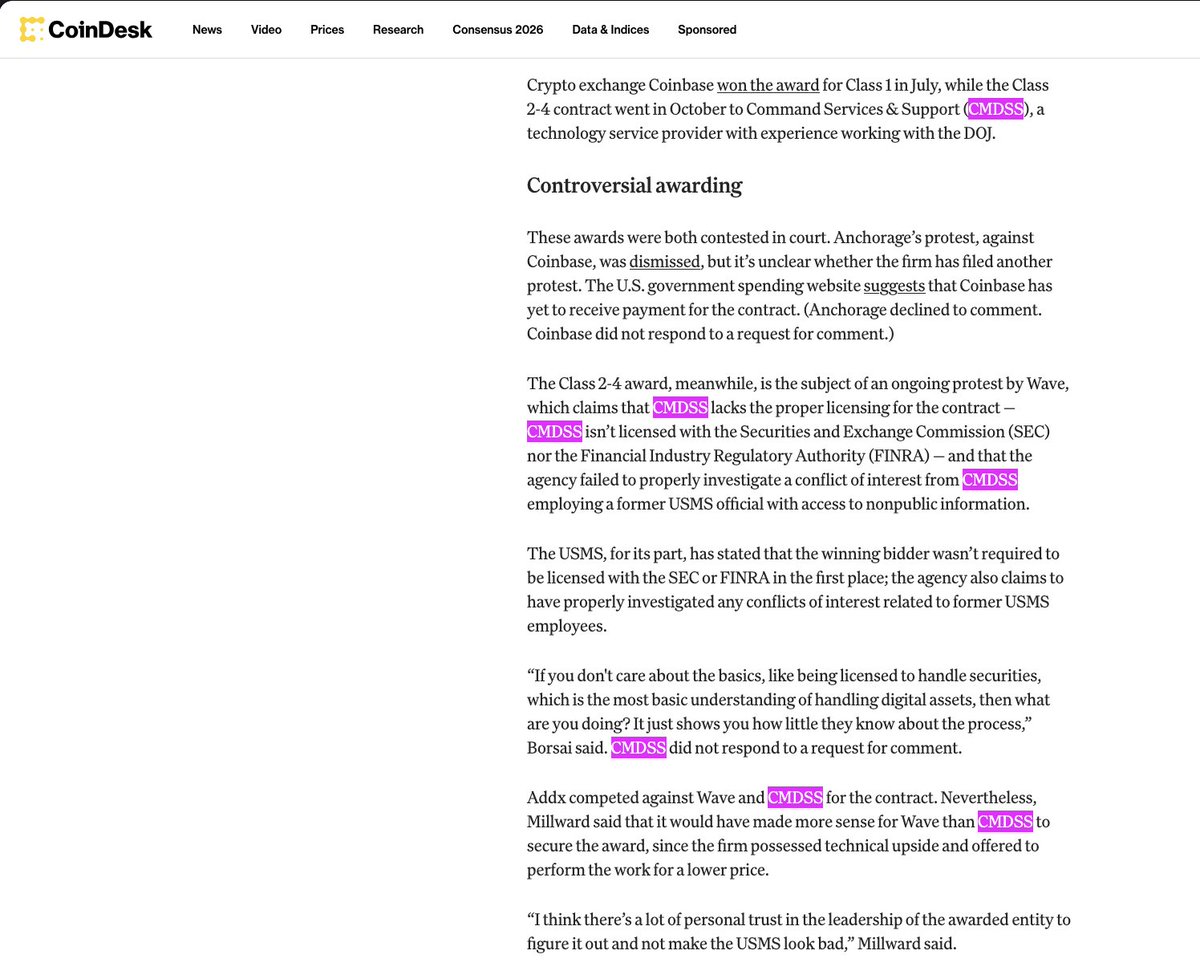
13/ It’s only a matter of time before the US gov’t starts cracking down on people like this for promoting constant scams. 
https://twitter.com/tier10k/status/1494342651495301120

14/ It’s crazy to think people like this don’t use better OpSec when everything you do is on the blockchain.
Maybe at some point newbies will stop blindly following people and getting exploited but I doubt it.
Maybe at some point newbies will stop blindly following people and getting exploited but I doubt it.
It’s clear he has no shame at all lol
https://twitter.com/1goonrich/status/1492528201532379140
• • •
Missing some Tweet in this thread? You can try to
force a refresh