Another day, another Solana fake account exploit. This time, @CashioApp lost around $50M (based on a quick skim). How did this happen? 

In order to mint new CASH, you need to deposit some collateral. This cross-program invocation (CPI) will transfer tokens from your account to the protocol's account, but only if the two accounts hold the same type of token. Otherwise, the token program will reject the transfer. 

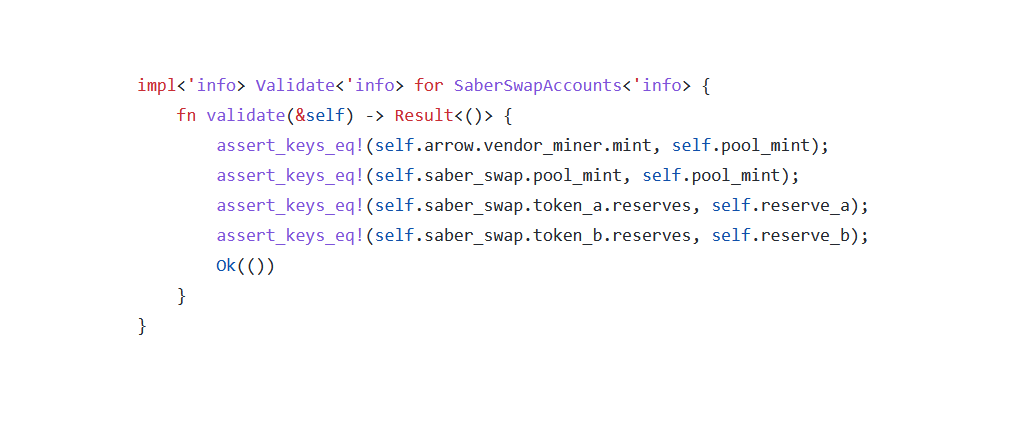
Here, the protocol validates that the crate_collateral_tokens account hold the right type of token by comparing it with the collateral account. It also verifies the collateral account shares the same token type as the saber_swap.arrow account. 

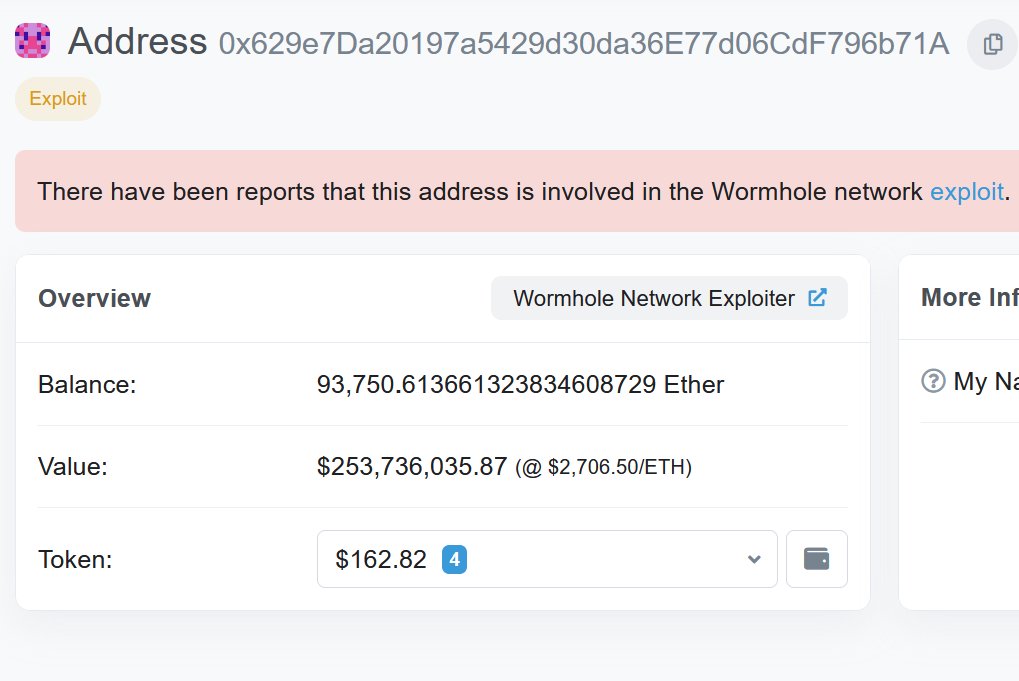
This means that ultimately, all of this validation is meaningless because there's no trusted root. The attacker just created fake accounts all the way down and then chained it all the way back up until they finally made a fake crate_collateral_tokens account. 
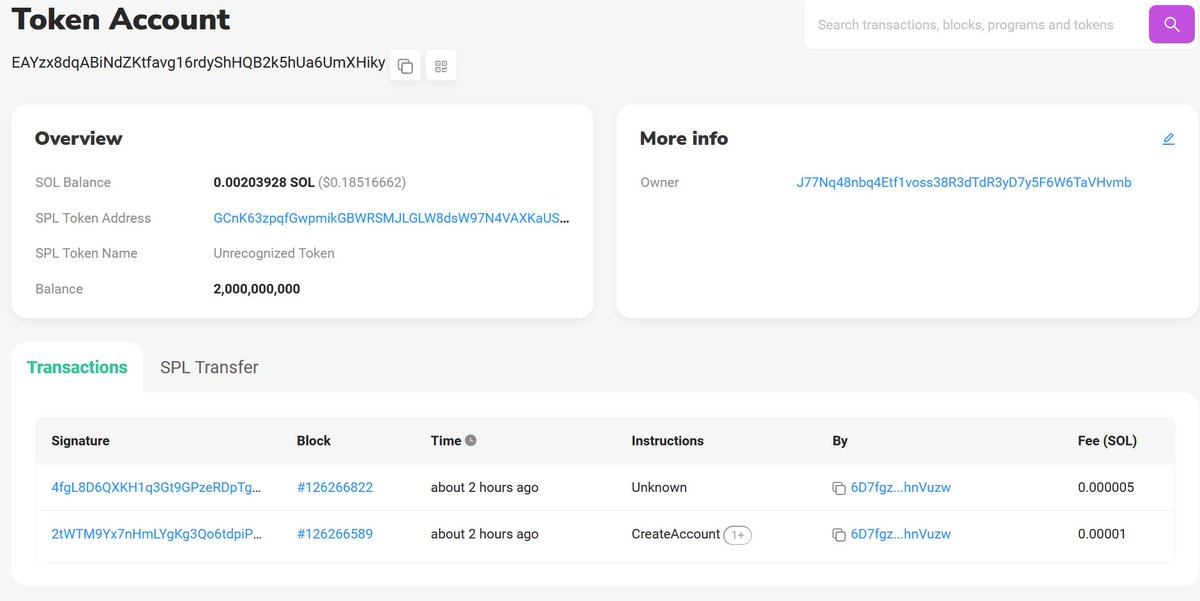
tl;dr because Cashio didn't establish a root of trust for all of the accounts it used, an attacker was able to steal approximately $50M by forging a chain of fake accounts
Turns out this thread is incomplete - here's part two!
https://twitter.com/samczsun/status/1507056110934511619
• • •
Missing some Tweet in this thread? You can try to
force a refresh