Announcing Flashbots Protect Fast Mode 🔥🏎
Fast mode is a way of using the Flashbots relay with a different set of tradeoffs, giving you more choice when transacting on Ethereum.
Fast mode is a way of using the Flashbots relay with a different set of tradeoffs, giving you more choice when transacting on Ethereum.

Regular bundles enjoy protection from frontrunning and reverts but can be slower than regular transactions (txns) sent through the public mempool.
"Fast mode" is a new txn type that inherits full frontrunning protection but can revert. In return, your txn is included faster.
"Fast mode" is a new txn type that inherits full frontrunning protection but can revert. In return, your txn is included faster.
When should you use bundles & when should you use fast mode?
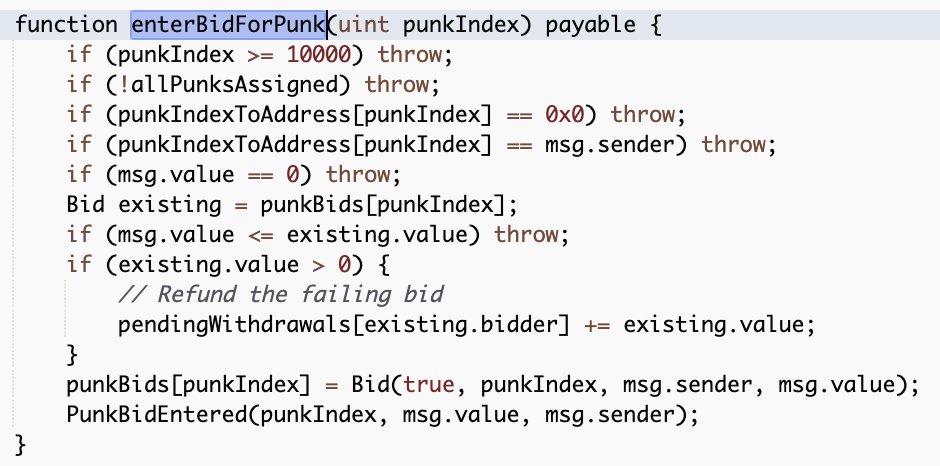
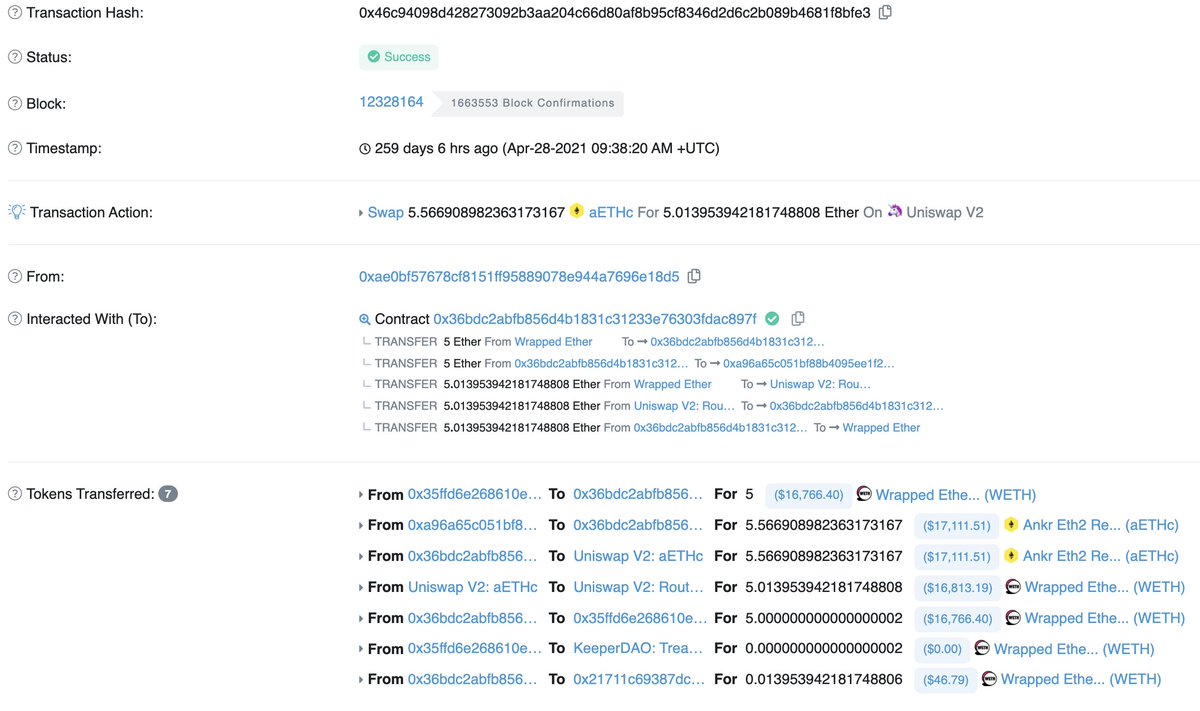
Txns that frequently revert (e.g. swaps on popular pairs) or that should be at the top of the block ➡️ bundles
Txns that likely won't revert (e.g. swaps on long tail pairs) ➡️ fast mode
Txns that frequently revert (e.g. swaps on popular pairs) or that should be at the top of the block ➡️ bundles
Txns that likely won't revert (e.g. swaps on long tail pairs) ➡️ fast mode
How do you add Flashbots Protect with fast mode?
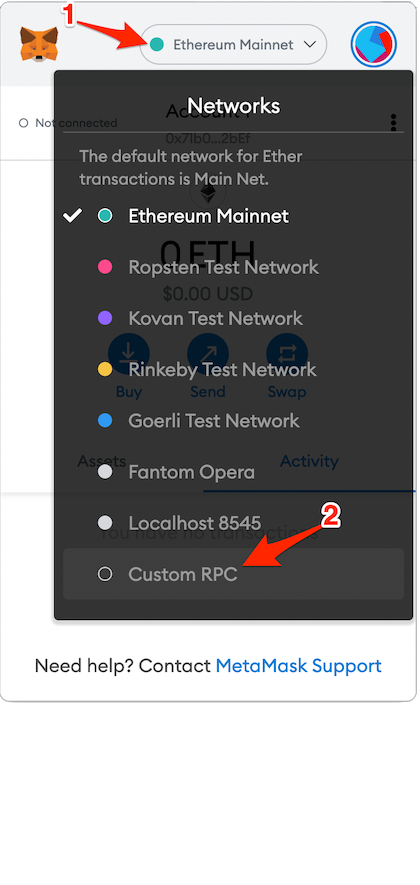
1. Enter your MetaMask & click on your RPC endpoint at the top of your MetaMask. By default it says “Ethereum mainnet.”
2. Click “Custom RPC”
1. Enter your MetaMask & click on your RPC endpoint at the top of your MetaMask. By default it says “Ethereum mainnet.”
2. Click “Custom RPC”
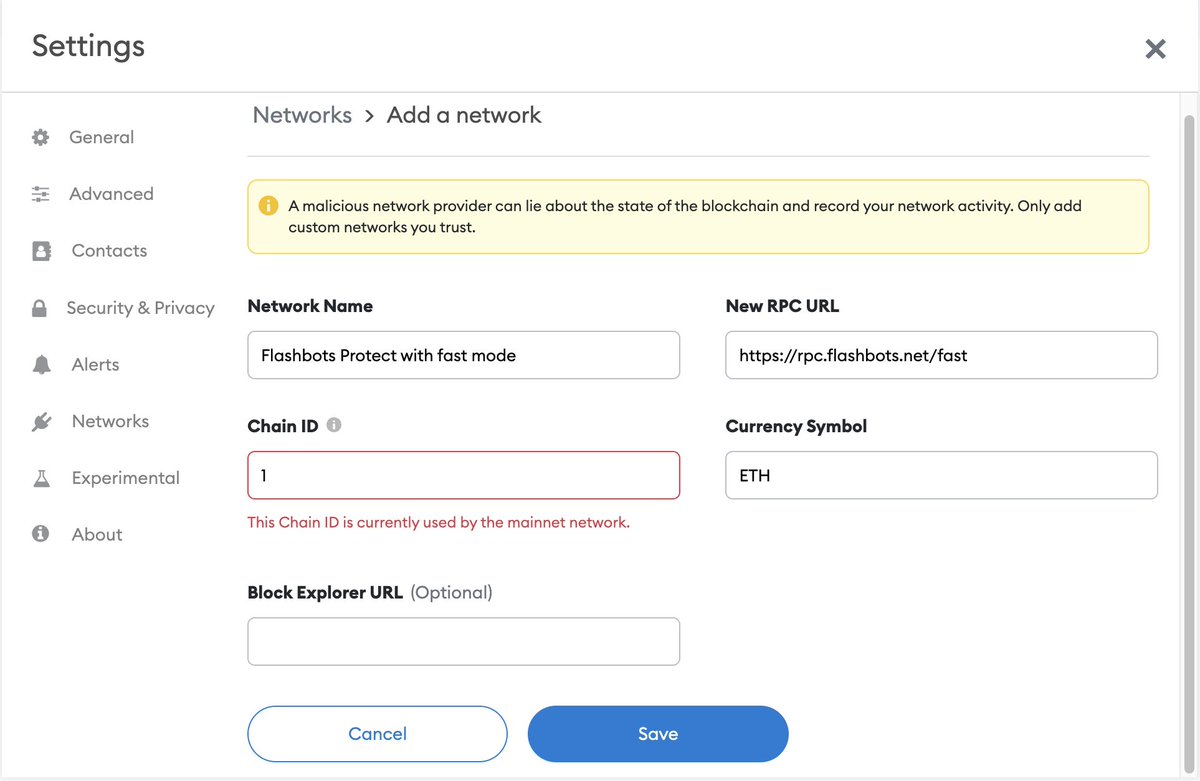
3. Add rpc.flashbots.net/fast with a chainID of 1 and currency of ETH.
4. Scroll to the bottom and click “Save”
4. Scroll to the bottom and click “Save”
Now your transactions are sent with fast mode 🏎️🔥
If you're excited about work like this or MEV in general we have open data, engineering, operations, and research roles!
See below for details and feel free to DM with any questions.
flashbots.notion.site/Flashbots-Job-…
See below for details and feel free to DM with any questions.
flashbots.notion.site/Flashbots-Job-…
• • •
Missing some Tweet in this thread? You can try to
force a refresh