1\ #ThreatHunting: How to detect fileless Linux malware
Look for processes in /proc/<PID>/exe where the path shows "(deleted)"
Here are two examples👇
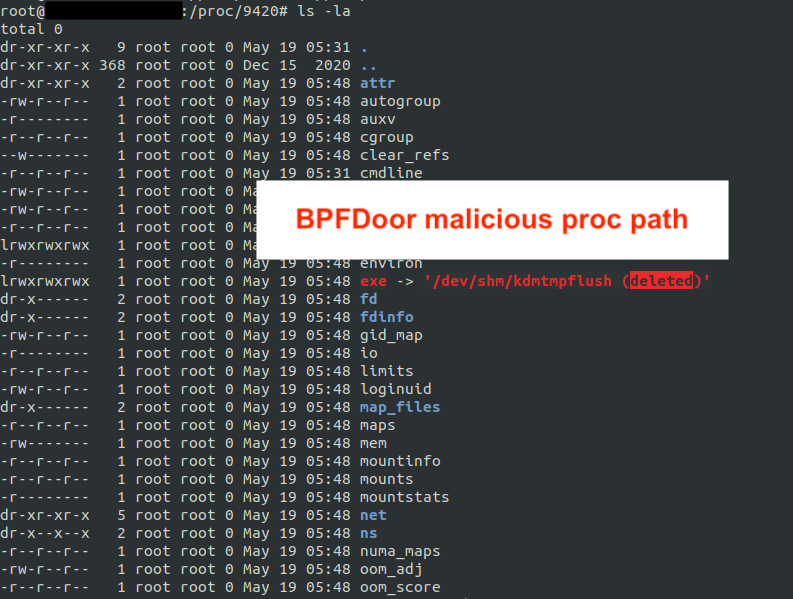
1. BPFDoor deleted binary
2. An attacker abusing memfd_create() to exec their malware in RAM w/o dropping files to disk.

Look for processes in /proc/<PID>/exe where the path shows "(deleted)"
Here are two examples👇
1. BPFDoor deleted binary
2. An attacker abusing memfd_create() to exec their malware in RAM w/o dropping files to disk.

2\ To recover/extract these binaries running in memory - you can copying them out from this location:
/proc/<PID>/exe
Also as an FYI for memfd_create() abuse detection you can hunt for the "memfd: (deleted)" string directly.
/proc/<PID>/exe
Also as an FYI for memfd_create() abuse detection you can hunt for the "memfd: (deleted)" string directly.

3\ You can also review what command line spawned the pid by reviewing:
/proc/<PID>/cmdline
This screenshot shows the cmdline used for the memdf_create() reverse shell. There are a lot of other interesting things you can also review in /proc/PID
/proc/<PID>/cmdline
This screenshot shows the cmdline used for the memdf_create() reverse shell. There are a lot of other interesting things you can also review in /proc/PID

4\ Btw if you're interested in the memdf_create() technique if you're a redteamer/pentester check out this awesome presentation discussing this technique
2018.zeronights.ru/wp-content/upl…
2018.zeronights.ru/wp-content/upl…
• • •
Missing some Tweet in this thread? You can try to
force a refresh