1/ Today, someone tried to hack me with a crypto stealer, so I guess I've finally made it
Fortunately, they weren't successful, but all it would've taken was three clicks. Read on to learn about how the attack works, how to protect yourself, and some basic malware analysis🕵️
Fortunately, they weren't successful, but all it would've taken was three clicks. Read on to learn about how the attack works, how to protect yourself, and some basic malware analysis🕵️

2/ The first step is to create an urgent and compelling hook. When placed under pressure, even trained security professionals might act instinctively instead of rationally. This DM does both.
If you clicked the link, then you're only two clicks away from being pwned
If you clicked the link, then you're only two clicks away from being pwned

3/ Clicking the link automatically downloads this file to your computer. Once again, this is compelling - who is cryptogeng.eth, and what exactly does the statement claim?
If you open the download, then you're one click away from being pwned
If you open the download, then you're one click away from being pwned

4/ There are two files in the archive. If you have file extensions enabled, then you'll see the first as a URL. If you don't, then you'll see the second as a PDF. Both of these are malicious, and opening either of them would give the attacker full access to your tokens 



5/ So how do you protect yourself? Well, the first step is to recognize when a message looks suspicious. In this case, the phrasing in the DM was very clunky, and it came from an untrusted source. However, you can't always rely on this, since it's trivial to hire a proofreader
6/ The next step is to take a moment to gather your thoughts if you're in an urgent situation. If you're communicating async, you have all the time in the world to respond. If you're on a phone call, ask them to wait. There's almost nothing so urgent that they can't wait 30s
7/ Don't let curiosity get the better of you. It might be tempting to snoop around, but threat actors know this and they'll exploit it. This is also why you should never plug in USBs that you find laying around, or open files named "2021-12-payroll.xlsx". Curiosity killed the cat
8/ Finally, if someone wants you to download and run a program, you should almost always double check if it's legitimate. Once you run a program, it has full access to your computer, so make sure you trust and verify who the program is coming from
9/ Now on to the basic malware analysis. How did I know that this is a crypto stealer without getting hacked? The first step was to pick a sandbox. I chose Docker because I figured some Windows malware probably wouldn't have a Linux container escape if I accidentally ran it 

11/ I ran `strings` on the binary to see if anything interesting popped up and it crashed trying to render this seemingly infinite stream of Y 

12/ At this point I figured that the binary itself was obfuscated and the Y garbage was embedded in the program, and I contemplated whether I actually cared enough to continue. However, @gf_256 suggested just checking if the files were right-padded 

14/ At this point, I had two binaries that I could've opened in IDA or Binary Ninja or any other reverse engineering tool. However, no point working harder if I could work smarter 

15/ I dumped both files into @HybridAnalysis and let it run. Sure enough, both files came back malicious 



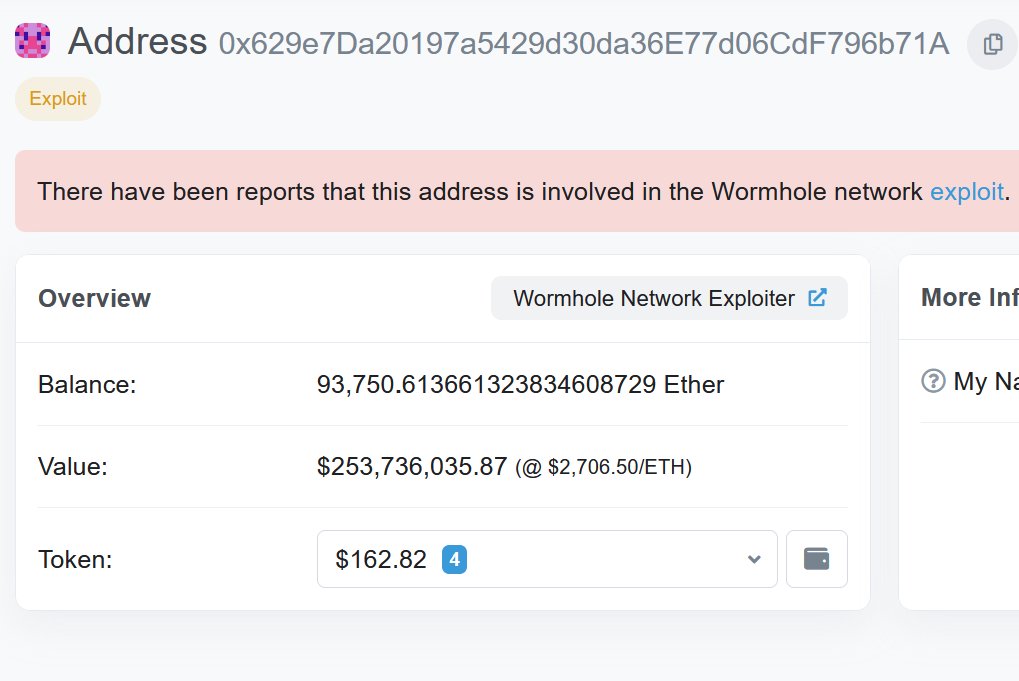
16/ Specifically, both files try to:
a) steal your wallet data directly
b) steal your wallet data from browser extensions
c) steal your Discord session token


a) steal your wallet data directly
b) steal your wallet data from browser extensions
c) steal your Discord session token



17/ So there you have it. All it takes is three clicks for a crypto stealer to get your wallets and session tokens, so make sure you watch for red flags in grammar, don't panic when facing an urgent situation, temper your curiosity, and never run software that you don't trust
• • •
Missing some Tweet in this thread? You can try to
force a refresh