#BeosinAlert
Beosin EagleEye reported an exploit on @XaveFinance, allowing an attacker to mint 100,000,000,000,000 $RNBW.
Attack tx:
etherscan.io/tx/0xc18ec2eb7…
Beosin EagleEye reported an exploit on @XaveFinance, allowing an attacker to mint 100,000,000,000,000 $RNBW.
Attack tx:
etherscan.io/tx/0xc18ec2eb7…

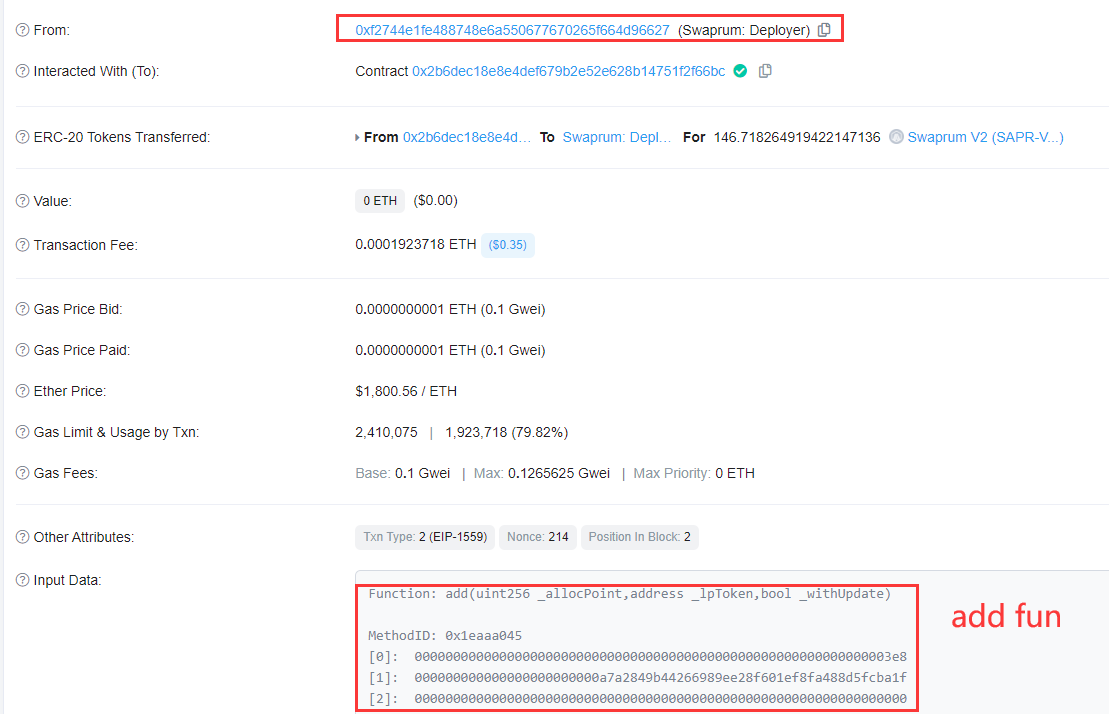
2/ The attacker first created the attack contract 0xe167cdaac8718b90c03cf2cb75dc976e24ee86d3 to call the DaoModule 0x8f90 contract's executeProposalWithIndex() function to execute a proposal. 

3/ The proposal is to call the mint() function to mint 100,000,000,000,000 $RNBW and transfer ownership to the attacker.
Finally the hacker swapped them to $xRNBW, which sit at the attacker's address 0x0f44f3489D17e42ab13A6beb76E57813081fc1E2.
Finally the hacker swapped them to $xRNBW, which sit at the attacker's address 0x0f44f3489D17e42ab13A6beb76E57813081fc1E2.
• • •
Missing some Tweet in this thread? You can try to
force a refresh