#Flashloan
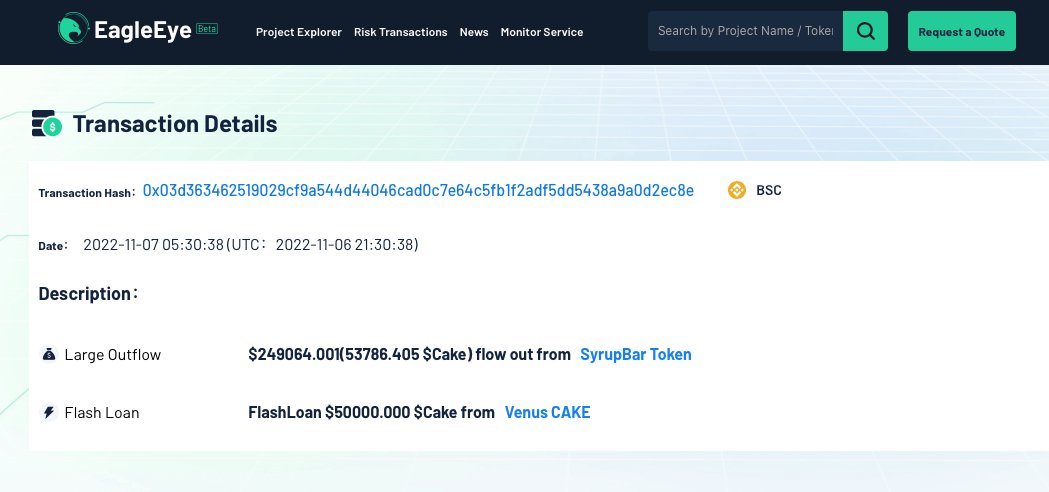
Beosin EagleEye monitored a flashloan attack on MooCakeCTX contract. The loss is ~$140K.
There is no time restrictions on collateral and rewards, and the prevention of caller is not comprehensive enough, enabling the attacker to increase dividends via flashloan.
Beosin EagleEye monitored a flashloan attack on MooCakeCTX contract. The loss is ~$140K.
There is no time restrictions on collateral and rewards, and the prevention of caller is not comprehensive enough, enabling the attacker to increase dividends via flashloan.
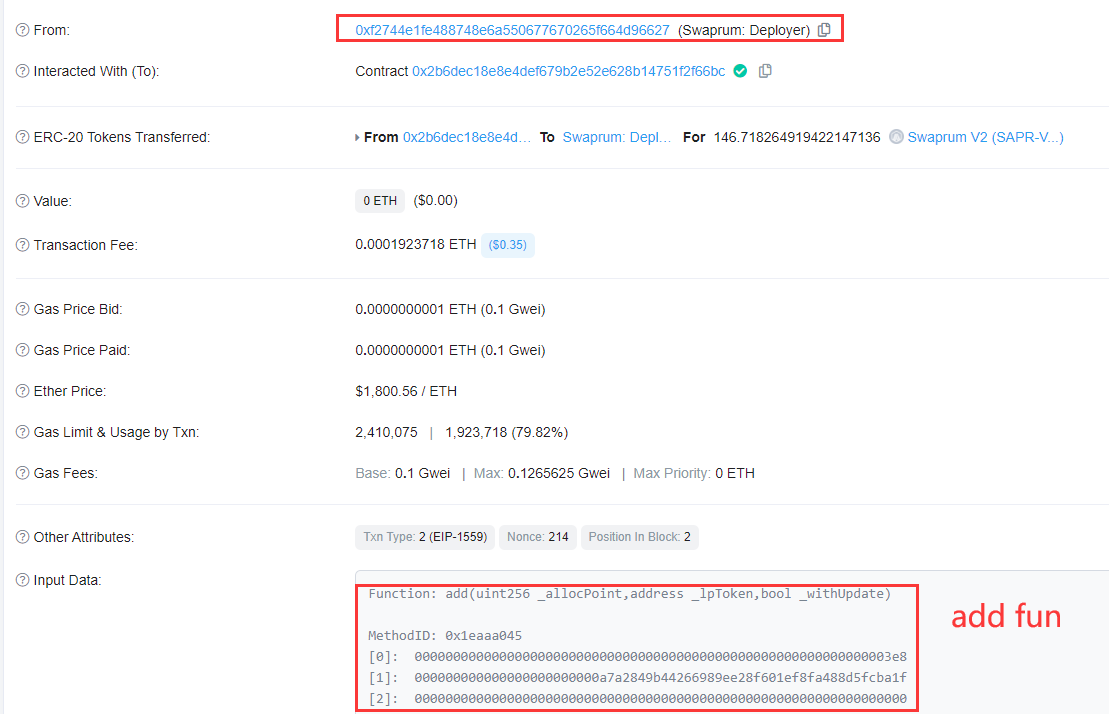
2/ Tx:
bscscan.com/tx/0x03d363462…
The attacker flashloaned $BUSD and swapped into vBUSD and then into $CAKE, as only $CAKE can be used as collateral in StrategySyrup. The $CTK are prepared at the same time, so that smartchef function can call a successfully performed transfer.

bscscan.com/tx/0x03d363462…
The attacker flashloaned $BUSD and swapped into vBUSD and then into $CAKE, as only $CAKE can be used as collateral in StrategySyrup. The $CTK are prepared at the same time, so that smartchef function can call a successfully performed transfer.


3/ After calling deposit function, the hacker called harvest function. Here the call address is the attack contract. The harvest function judges whether the call address is an EOA address, but when the initiating call in the case of the constructor, iscontract() can be bypassed. 





4/ In the BeefyVault contract, since the reward calculation is based on the share of the deposit, where the update reward is updated according to the account calling harvest function, then in one update round to claim the reward, the larger the share, the more the profit. 



5/ So the attacker used flashloan to amplify the proceeds (the last time 733 days ago), and bypassed the iscontract.
It is worth noting that here depositAll and withdrawAll are not time-related, so the attacker can call withdrawAll immediately after deposit to claim the reward.

It is worth noting that here depositAll and withdrawAll are not time-related, so the attacker can call withdrawAll immediately after deposit to claim the reward.


6/ The attacker executed two more attacks and returned the flashloan with a profit of 424 $BNB (~ $140,000).
Suggestion:
When developing contracts, pay attention to flashloan attack scenario, the security of the way rewards are issued, and the secure use of library functions.
Suggestion:
When developing contracts, pay attention to flashloan attack scenario, the security of the way rewards are issued, and the secure use of library functions.
• • •
Missing some Tweet in this thread? You can try to
force a refresh