Application programming interfaces (APIs) have become a critical part of almost every business.
APIs are responsible for transferring information between systems within a company or to external companies.
For example, 🧵:👇
APIs are responsible for transferring information between systems within a company or to external companies.
For example, 🧵:👇
when you log in to a website like Google or Facebook, an API processes your login credentials to verify they are correct.
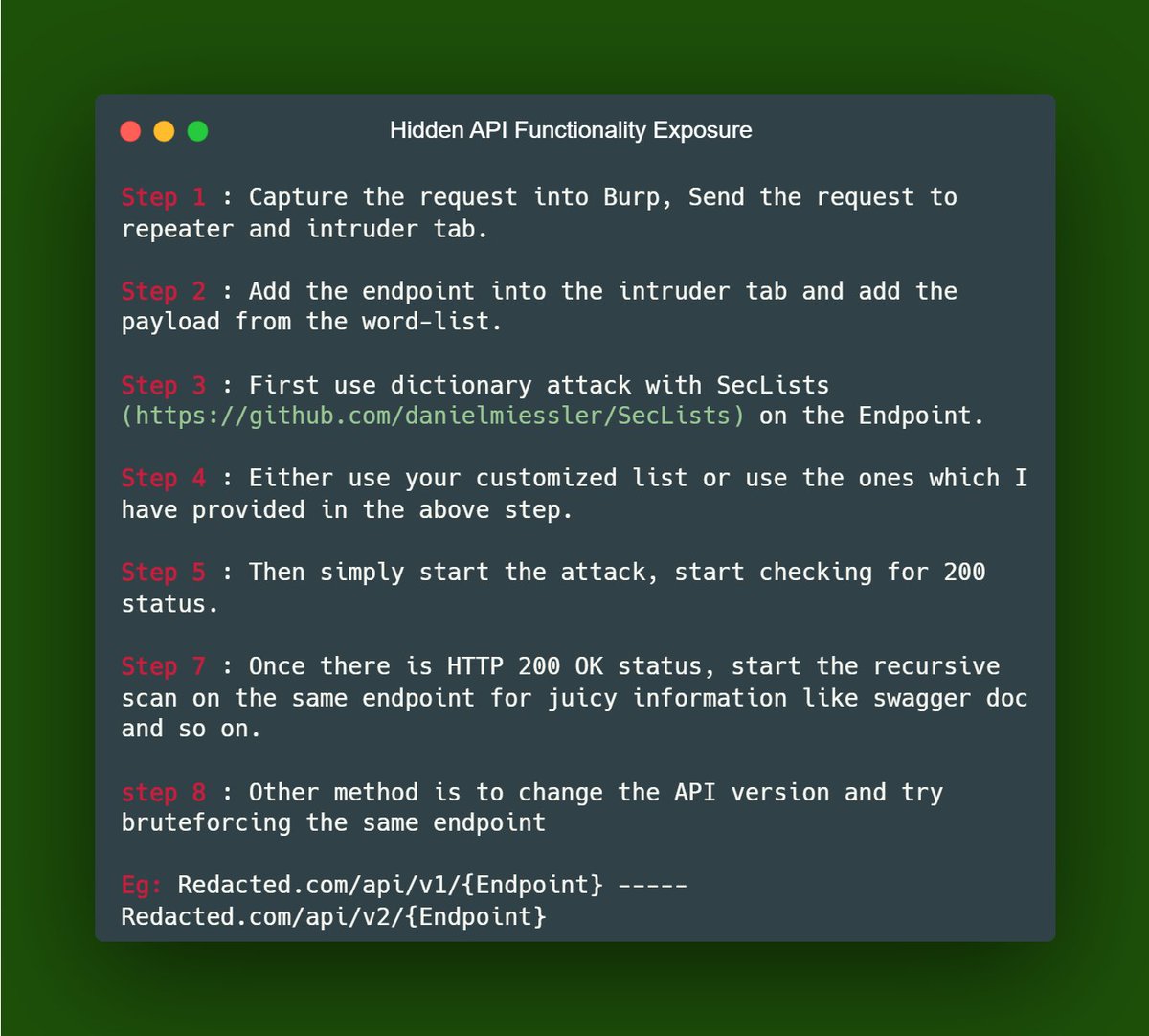
• Swagger UI Documentation
• Dictionary Attack | Brute force
• Common wordlist for API Enum:
1. wordlists.assetnote.io
2. github.com/Net-hunter121/…
:👇
• Swagger UI Documentation
• Dictionary Attack | Brute force
• Common wordlist for API Enum:
1. wordlists.assetnote.io
2. github.com/Net-hunter121/…
:👇
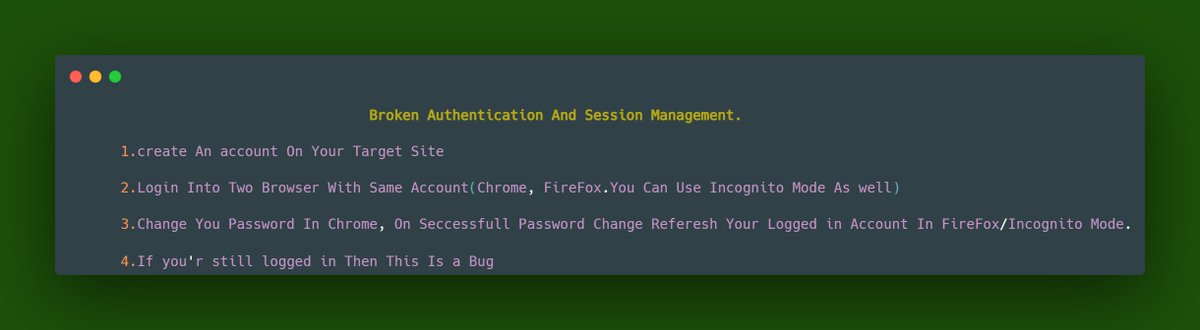
Steps to Perform This Attack :
#bugbounty #infosec
==
My Bugbounty Tips Group Link 🔗:👇
t.me/bugbountyresou…
==
Thread🧵:👇
#bugbounty #infosec
==
My Bugbounty Tips Group Link 🔗:👇
t.me/bugbountyresou…
==
Thread🧵:👇
• • •
Missing some Tweet in this thread? You can try to
force a refresh