
1/5 What are boundary nodes and what role do they play on the #internetcomputer?
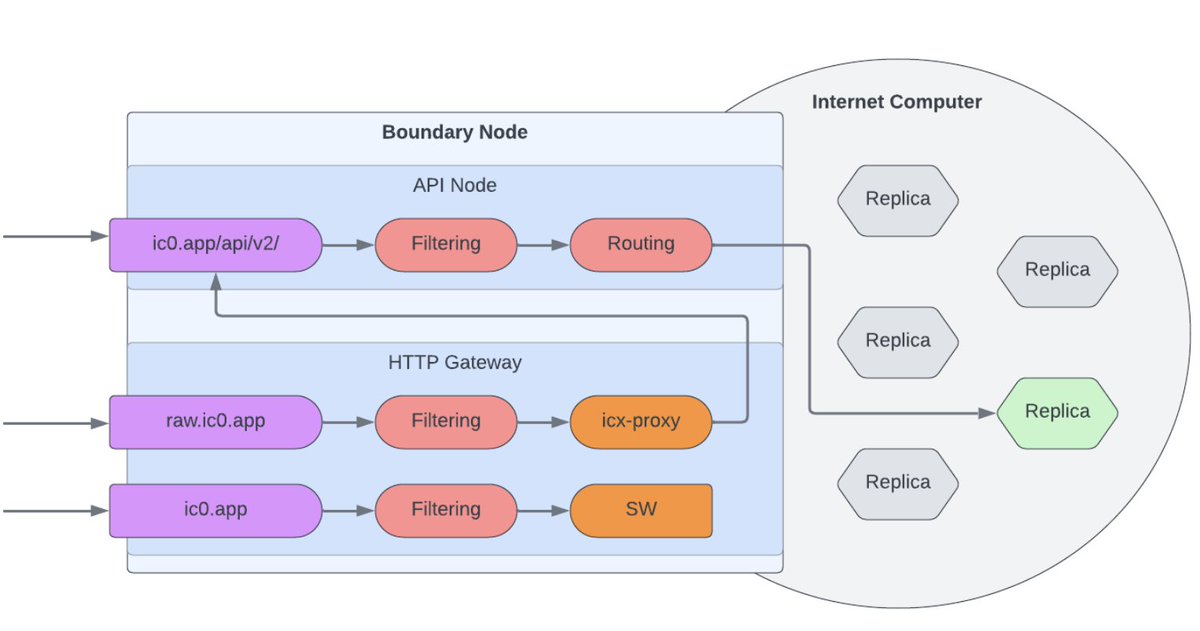
Boundary nodes provide a public endpoint for the IC, route all incoming requests to the right subnet, loadbalance requests across replica nodes, and cache responses for improved performance.
Boundary nodes provide a public endpoint for the IC, route all incoming requests to the right subnet, loadbalance requests across replica nodes, and cache responses for improved performance.

2/5 Boundary nodes provides canister access through the HTTP gateway which translates all incoming HTTP requests into API canister calls, which are then routed to the right subnet. 
3/5 The boundary nodes also provide caching to improve the performance of the dapps hosted on the IC.
The boundary nodes serving `ic0.app` are globally distributed. Requests are directed to the geographically closest pool and load balanced within that pool.
The boundary nodes serving `ic0.app` are globally distributed. Requests are directed to the geographically closest pool and load balanced within that pool.

4/5 boundary nodes detect crawlers and bots to `ic0.app` and internally redirect them to `icx-proxy`.
This allows the dapps running on the Internet Computer to be indexed by search engines and metadata can be read to generate previews on social platforms.
This allows the dapps running on the Internet Computer to be indexed by search engines and metadata can be read to generate previews on social platforms.
5/5 In the future, a new boundary node architecture currently being worked on will decompose boundary nodes into “HTTP gateways” and “API Boundary Nodes”.
• • •
Missing some Tweet in this thread? You can try to
force a refresh







