Malware Analysis Tip - Use Process Hacker to watch for suspicious .NET assemblies in newly spawned processes.
Combined with DnSpy - it's possible to locate and extract malicious payloads without needing to manually de-obfuscate.
1/
#Malware #dnspy #analysis #RE



Combined with DnSpy - it's possible to locate and extract malicious payloads without needing to manually de-obfuscate.
1/
#Malware #dnspy #analysis #RE



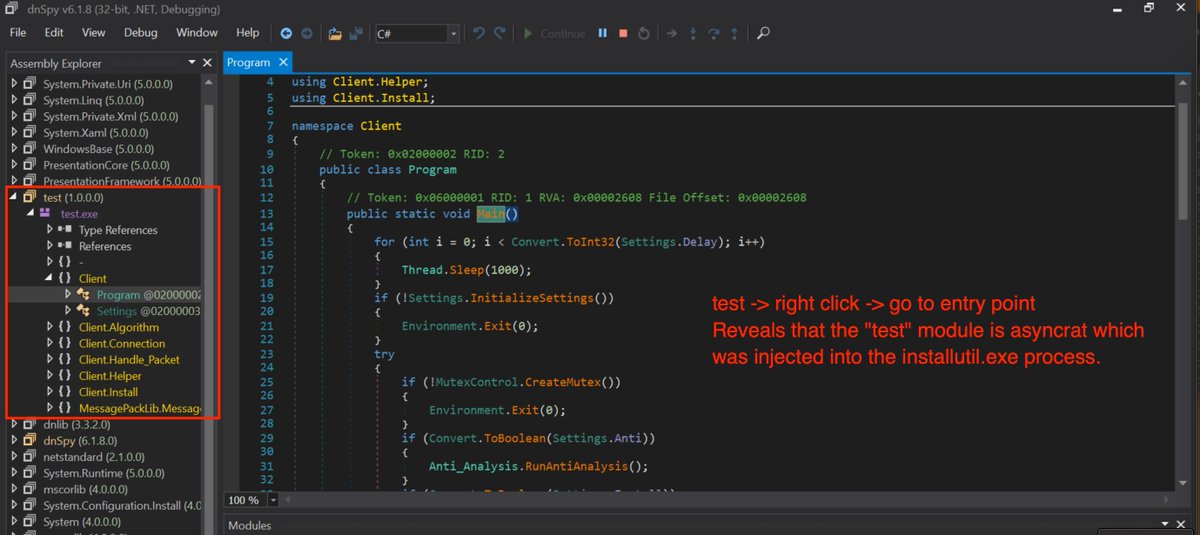
2/ For anyone wanting to try - The initial sample can be in the link below
Once executed (inside of a safe vm!) - You should see the installutil.exe detailed in the screenshots above.
(Make sure to use Dnspy-x86 for attaching to the process) 😄
bazaar.abuse.ch/sample/b24c75d…
Once executed (inside of a safe vm!) - You should see the installutil.exe detailed in the screenshots above.
(Make sure to use Dnspy-x86 for attaching to the process) 😄
bazaar.abuse.ch/sample/b24c75d…
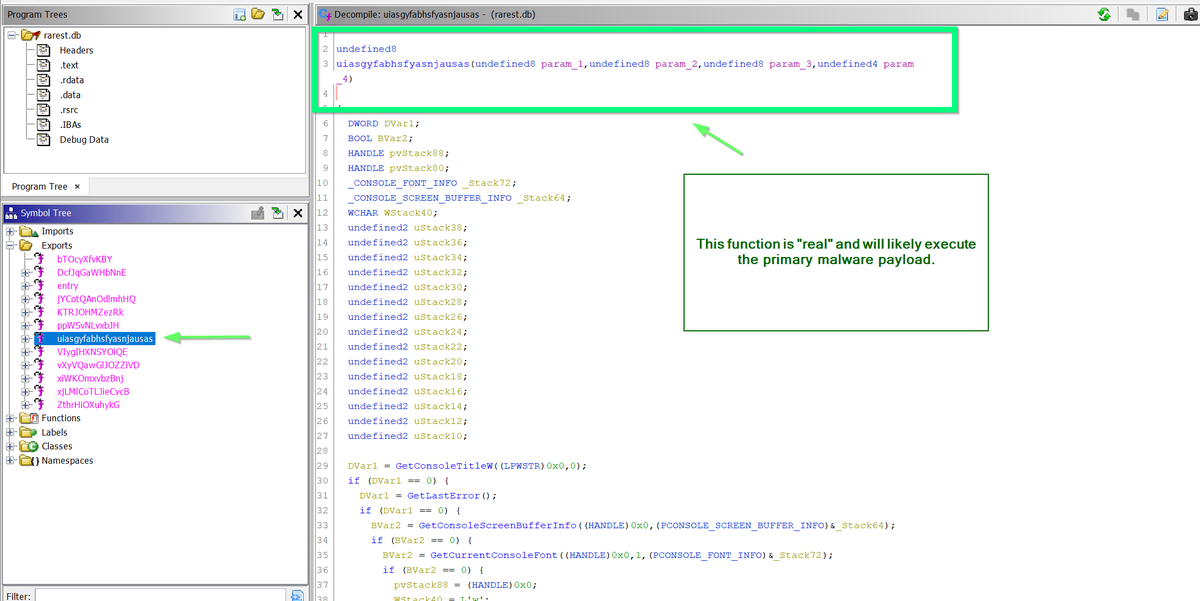
3/ Sometimes you'll get lucky and the modules will be named much more suspiciously.
See below for an example of a suspected #redlinestealer loader. Which injected multiple modules into a renamed powershell.exe.
bazaar.abuse.ch/sample/7e09174…

See below for an example of a suspected #redlinestealer loader. Which injected multiple modules into a renamed powershell.exe.
bazaar.abuse.ch/sample/7e09174…


• • •
Missing some Tweet in this thread? You can try to
force a refresh