
⚠️ WARNING: There is currently a high volume of so-called #Malvertising attacks. Threat actors are placing ads in search engines like Google to to distribute their malware payloads. 🧵1/7
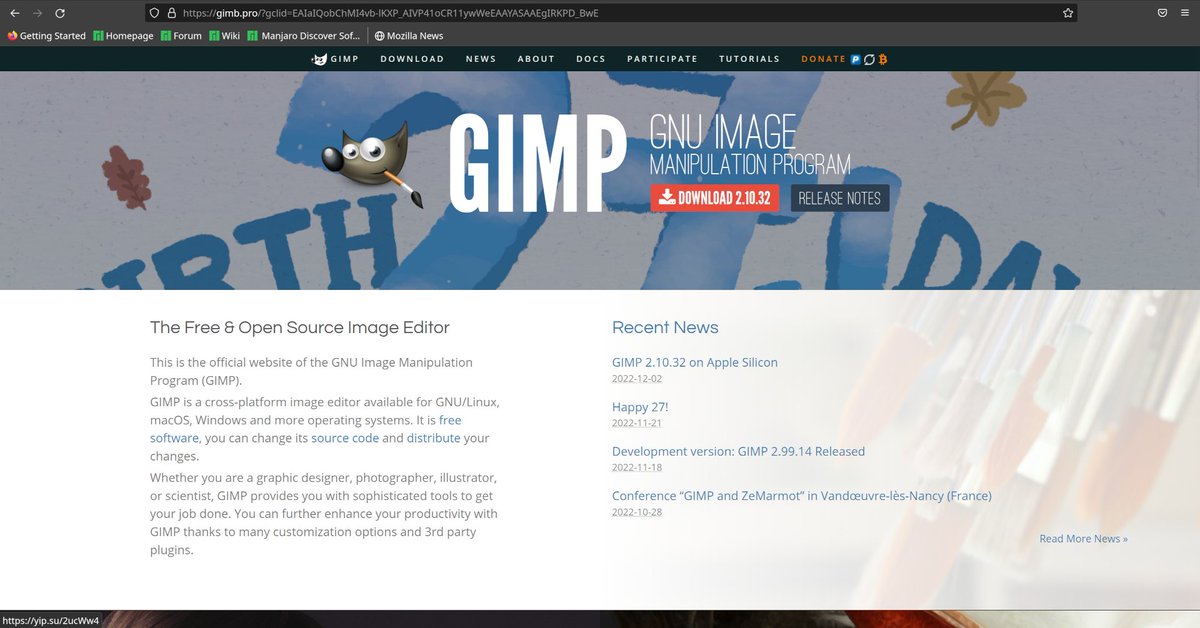
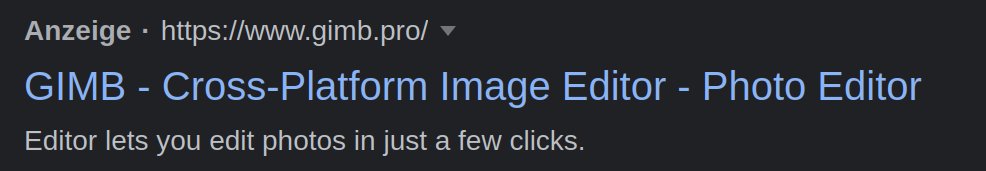
Their fraudulent web pages mimic the look of legitimate download pages for common software products. For example, here is a search advertisement and the corresponding fake website pretending to offer the software GIMP. 🧵2/7 

However, instead of the benign software package, information stealers and other malware 🔥 are contained in the downloaded files. Once a victim user downloads and opens such a file, sensitive information such as browser profiles, email messages and more is stolen. 🧵3/7 

As you can see in the screenshot, the downloaded files usually have a size of several hundred megabytes. This is a defense evasion technique commonly seen in the last months to hinder security and analysis tools. 🧵4/7
The current campaigns that we are tracking mostly lead to samples of #Vidar and #Rhadamanthys stealer, but other malware may be delivered as well. In the past, we have seen for example incidents involving #Raccoon stealer 🧵5/7
To protect from this threat, online users should check 🔍 twice before downloading files from dubious websites. When in doubt, users can check a trusted source to find the legitimate URL of a given product or software. 🧵6/7
Companies should setup policies to block software from untrusted sources. Software that is needed for normal business operation should be provided through trusted repositories. Furthermore, EDR solutions can help to spot suspicious information stealer behaviour. 🧵7/7
• • •
Missing some Tweet in this thread? You can try to
force a refresh











