
The @BonqDAO is exploited and its price oracle is manipulated to increase the #WALBT price. Here is the example hack tx: polygonscan.com/tx/0x31957ecc4… 

Using the above tx as an example, with the manipulated #WALBT price, the malicious actor is able to mint >100M #BEUR. 

In a follow-up tx, the actor further manipulates the #WALBT price and liquidates a bunch of (33) troves: polygonscan.com/tx/0xa02d0c3d1… 

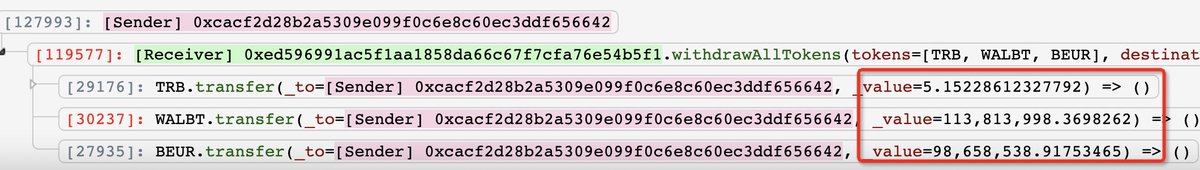
The actor then walks away by withdrawing the illicit gains with 113.8M #WALBT and 98M #BEUR (valued >$10M). Some of these tokens are then dumped, resulting in major drop! #WALBT dropped by >50% and #BEUR dropped by 34% 




• • •
Missing some Tweet in this thread? You can try to
force a refresh


















